
The role of SELinux: 1. Provides improved security for the Linux system by using MAC control for processes and file resources; 2. Grants the subject minimal access privileges to minimize the risk of The resources accessible to the service process can prevent the subject from adversely affecting other users or processes; 3. Each process has its own running area. Each process only runs in its own domain and cannot access other processes and files; 4. SELinux can limit malicious code activities in Linux systems to the greatest extent possible.

#The operating environment of this tutorial: linux7.3 system, Dell G3 computer.
SELinux, the abbreviation of Security Enhanced Linux, is security-enhanced Linux. It was jointly developed by the National Security Agency (NSA) and other security agencies (such as SCC) to enhance the traditional Linux operating system. It improves security and solves various permission problems in the Discretionary Access Control (DAC) system in traditional Linux systems (such as excessive root permissions, etc.).
Beginners can understand SELinux in this way. It is a functional module deployed on Linux to enhance system security.
Traditional Linux system security uses DAC (discretionary access control), while SELinux is a security enhancement function module deployed in Linux systems. It uses MAC (MAC) for process and file resources. Mandatory access control) provides improved security for Linux systems.
The main function of SELinux
adopts MAC (mandatory access control) control method for processes and file resources , provides improved security for Linux systems.
Minimize the resources accessible to the service process in the system (principle of least privilege).
It gives the subject (user or process) the least access privileges, which means that each subject is only given a limited set of permissions necessary to complete the relevant tasks. By granting least access privileges, you can prevent a principal from adversely affecting other users or processes.
During the SELinux management process, each process has its own running area (called a domain). Each process only runs in its own domain and cannot access other processes and files unless it is Special permissions granted.
SELinux can limit the activities of malicious code in Linux systems to the maximum extent possible.
Extended knowledge:
Basic concepts of SELinux:
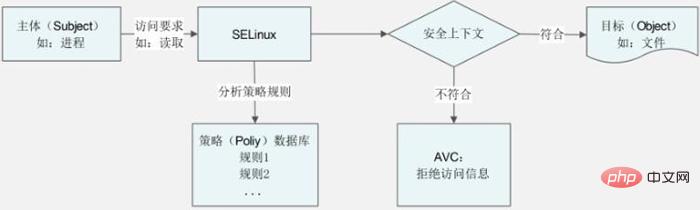
1. Subject: It is a process that wants to access file or directory resources. To obtain resources, the basic process is as follows: the user calls a command, the command generates a process, and the process accesses the file or directory resource. In a discretionary access control system (Linux default permissions), the subject controlled by permissions is the user; in a mandatory access control system (SELinux), the subject controlled by policy rules is the process.
2. Object: This concept is relatively clear, it is the file or directory resource that needs to be accessed.
3. Policy: There are a huge number of processes and files in the Linux system, so the number of SELinux rules that limit whether processes can access files is even more cumbersome. If each rule requires manual setting by the administrator, Then the availability of SELinux will be extremely low. Fortunately, we don't need to manually define the rules. SELinux defines two policies by default. The rules have been written in these two policies. By default, just call the policy and it can be used normally. The two default policies are as follows:
-targeted: This is the default policy of SELinux. This policy mainly limits network services and has very few restrictions on the local system. This strategy is enough for us.
-mls: Multi-level security protection policy, this policy is more restrictive.
4. Security Context: Each process, file and directory has its own security context. Whether a process can access files or directories depends on this security context. Whether it matches. If the security context of the process matches the security context of the file or directory, the process can access the file or directory. Of course, to determine whether the security context of a process matches the security context of a file or directory, you need to rely on the rules in the policy. For example, we need to find a partner, men can be regarded as the subject, and women are the targets. Whether a man can pursue a woman (whether the subject can access the target) mainly depends on whether the two people's personalities are suitable (whether the security context of the subject and the target matches). However, whether the personalities of two people are suitable needs to be judged based on specific conditions such as living habits, behavior, family environment, etc. (Whether the security context matches needs to be determined through the rules in the policy).
SELinux working mode
SELinux provides 3 working modes: Disabled, Permissive and Enforcing, and each mode provides different benefits for Linux system security.
1. Disable working mode (off mode)
In Disable mode, SELinux is turned off and the default DAC access control method is used. This mode is useful for environments that do not require enhanced security.
For example, if a running application is working fine from your perspective, but is generating a large number of SELinux AVC reject messages, it may eventually fill up the log file and render the system unusable. In this case, the most straightforward solution is to disable SELinux, but you can also set the correct security context on the files your application accesses.
It should be noted that before disabling SELinux, you need to consider whether SELinux may be used again on the system. If you decide to set it to Enforcing or Permissive in the future, the system will Process remarking via an automatic SELinux file.
The way to turn off SELinux is also very simple. Just edit the configuration file /etc/selinux/config and change SELINUX= in the text to SELINUX=disabled. After restarting the system, SELinux will be disabled.
2. Permissive working mode (permissive mode)
In Permissive mode, SELinux is enabled, but security policy rules are not enforced. When security policy rules should deny access, access is still allowed. However, a message is sent to the log file indicating that access should be denied.
SELinux Permissive mode is mainly used in the following situations:
Audit the current SELinux policy rules;
Test new applications to see how SELinux policy rules are applied to these What effect will the program have;
Solve the problem that a specific service or application no longer works properly under SELinux.
In some cases, the audit2allow command can be used to read the SELinux audit log and generate new SELinux rules to selectively allow denied behavior, and this is also a case where SELinux is not disabled. Here's a quick way to get your application working on a Linux system.
3. Enforcing working mode (enforcement mode)
As can be seen from the name of this mode, in Enforcing mode, SELinux is started and all security policy rules are enforced.
Related recommendations: "Linux Video Tutorial"
The above is the detailed content of What is the use of selinux in linux?. For more information, please follow other related articles on the PHP Chinese website!