Found a total of 5888 related content

What are the methods of password encryption?
Article Introduction:Password encryption methods include: 1. Use symmetric encryption algorithms (such as 3DES, AES) to encrypt. Using this method of encryption can restore the original password through decryption. Of course, the prerequisite is to obtain the key; 2. Use One-way HASH algorithm (such as MD5, SHA1) is used for password, but the original password cannot be restored through calculation; 3. Use a special one-way HASH algorithm for password; 4. Use PBKDF2 algorithm for encryption; 5. Use BCrypt algorithm for encryption; 6. Use SCrypt algorithm for encryption.
2022-06-30
comment 0
29041
excel怎么加密码怎么设置密码
Article Introduction:Excel 加密教程包括以下步骤:打开文件,点击“审阅”选项卡,选择“保护工作簿”。选择“加密使用密码”,输入并确认密码。可设置密码复杂性要求,包括最小密码长度。要移除密码,选择“取消密码保护”,输入密码即可。
2024-06-16
comment
938
php加密源码如何解密
Article Introduction:PHP 加密源码的解密方法包括:1. 了解加密机制(哈希加密、对称加密);2. 获取加密密钥(配置文件、环境变量、代码内);3. 使用解密工具(PHP 函数、第三方库、在线解密器);4. 实际操作(根据机制和工具不同而异);5. 注意安全密钥保密、不可逆哈希无法解密、第三方工具应谨慎使用。
2024-06-02
comment 0
763

How to implement password encryption in PHP
Article Introduction:Password encryption is one of the important methods to ensure the security of user accounts. In PHP, password encryption can be implemented using encryption algorithms and hashing algorithms. This article will introduce how to implement password encryption in PHP. 1. Use encryption algorithm for password encryption Encryption algorithm is one of the commonly used methods in password encryption. PHP has a variety of built-in encryption algorithms, and we can use the functions provided by PHP to perform encryption operations. Currently, the most commonly used encryption algorithms are MD5 and SHA256. 1. Use MD5 for encryption. MD5 is a widely used
2023-06-11
comment 0
1834

Password encryption mechanism in PHP projects
Article Introduction:In PHP projects, password security is crucial. Because password theft may cause substantial losses to users and affect the normal operation of the system. In order to protect the security of passwords, we can use password encryption mechanisms. The password encryption mechanism can convert plain text passwords into cipher text passwords, thereby improving password security. Even if a hacker steals the password, he cannot easily obtain the clear text password. At the same time, the password encryption mechanism can also prevent malicious attacks and internal data leakage. In PHP projects, the password encryption mechanism can be implemented through
2023-06-22
comment 0
431

How to implement password encryption in vuejs
Article Introduction:How to implement password encryption in vuejs: 1. Introduce the "crypto-js" dependency through npm; 2. Create a js file to introduce "crypto-js" and write the encryption method; 3. Use the cryptoObj encryption method in the component that needs to be encrypted. .
2021-10-27
comment 0
6113

What are the php password encryption methods?
Article Introduction:PHP password encryption method: 1. Use password_hash(), the syntax is "password_hash(password, PASSWORD_BCRYPT)"; 2. Use password_verify(), the syntax is "password_verify(password, hash)".
2021-07-06
comment 0
5525
What encryption method is mysql password?
Article Introduction:MySQL password is SHA-1 encryption method. It is an encryption method based on a hash algorithm, which converts the entered password into a hash value of 40 characters in length. The hash value is unique and irreversible. In MySQL, when user passwords are stored, what is actually stored is a hash value rather than a clear text password. Even if the database is attacked and the password file is leaked, the hacker will not be able to know the user's real password because it cannot be reversed from the hash value. Push out the original password.
2023-07-11
comment 0
2542

Symmetric encryption cryptography in Java
Article Introduction:IntroductionSymmetric encryption, also known as key encryption, is an encryption method in which the same key is used for encryption and decryption. This encryption method is fast and efficient and suitable for encrypting large amounts of data. The most commonly used symmetric encryption algorithm is Advanced Encryption Standard (AES). Java provides strong support for symmetric encryption, including classes in the javax.crypto package, such as SecretKey, Cipher, and KeyGenerator. Symmetric encryption in Java The JavaCipher class in the javax.crypto package provides cryptographic functions for encryption and decryption. It forms the core of the Java Cryptozoology Extensions (JCE) framework. In Java, the Cipher class provides symmetric encryption functions, and K
2023-09-13
comment 0
1056
php源码加密后怎么解密
Article Introduction:PHP 源码加密后的解密方法:1. 使用原始密钥:若有加密时使用的密钥,反向使用即可解密。2. 第三方工具:可使用 PHP Decrypter、PHP Code Decrypter、PHP Decryptor Online 等工具解密。3. 查找加密算法漏洞:若具备高级加密知识,可探索漏洞以解密。
2024-06-04
comment 0
762
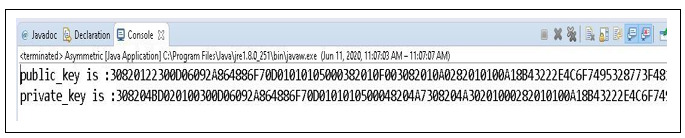
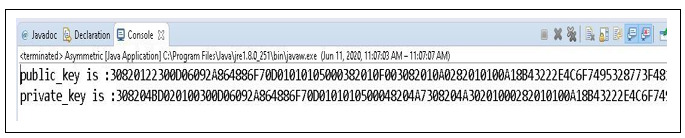
Asymmetric encryption cryptography in Java
Article Introduction:Cryptography is the study and practice of different techniques to protect communications from interference by third parties. It is used for network security. We attempt to develop methods and practices to protect sensitive data. The only goal of cryptography is to protect data from attackers. Asymmetric encryption is also known as public/private key encryption. The private key, as the name suggests, will remain private, while the public key can be distributed. Encryption is a mathematical relationship between two keys, one for encryption and the other for decryption. For example, if there are two keys "A1" and "A2", then if key "A1" is used for encryption, "A2" is used for decryption and vice versa. We use the RSA algorithm for asymmetric encryption. First we generate a pair of keys (public key, private key). Cryptozoology Togen of Asymmetric Encryption in Java
2023-08-19
comment 0
244
What are cryptosystems with different encryption and decryption keys called?
Article Introduction:Cryptosystems with different encryption and decryption keys are called public key encryption systems; public key encryption is also called asymmetric encryption, in which public key encryption is asymmetric. Compared with symmetric conventional encryption that uses only one key, It involves the use of two independent keys, one key is called the private key, which is kept secret, and the other key is called the public key and does not need to be kept secret.
2022-07-14
comment 0
8631
php代码怎么加密
Article Introduction:PHP代码加密是一种保护敏感信息的方法,方法包括:专有编码器(如ionCube编码器、Zend Guard)PHP代码混淆器PHP加密函数用户自定义编码加密方法的选择取决于安全要求、性能开销和预算。实施加密过程一般包括准备代码、选择方法、应用加密和测试加密。代码加密增强安全性,降低未经授权访问敏感信息的风险。
2024-05-25
comment 0
341

In-depth analysis of MySQL password encryption method
Article Introduction:With the development of the Internet, MySQL, as an open source relational database management system, is widely used in various applications. One of the important security issues is the encryption and storage of MySQL user passwords. So, what are the methods for MySQL password encryption? This article will give you an in-depth analysis. How MySQL passwords are stored Before understanding the MySQL password encryption method, let’s first understand how MySQL passwords are stored. Before MySQL version 5.7, the one-way hash algorithm (S
2023-06-15
comment 0
1725

How to use PHP to implement password encryption function
Article Introduction:How to use PHP to implement password encryption function Password is a security verification method that we often need to use in life and work. In order to protect users' privacy, we must encrypt and store users' passwords to prevent them from being stolen and abused by criminals. This article will introduce how to use PHP to implement password encryption function to increase the security of user passwords. In PHP, there is a very powerful encryption function password_hash() that can be used to generate a hash value of a password. This function can accept two parameters: plain text password and a
2023-08-19
comment 0
552
PHP password encryption and secure storage method?
Article Introduction:How to handle password encryption and secure storage in PHP? With the rapid development of the Internet, the protection of user privacy and data security has become an important issue. It is crucial for website and app developers to keep user passwords secure. In the PHP language, there are many ways to handle the encryption and secure storage of passwords. This article will introduce some common technologies and best practices to help developers strengthen the security of user passwords. Password Encryption Using Hash Functions When storing passwords, they should never be stored in clear text;
2023-06-30
comment 0
1182

Detailed explanation of MySQL password encryption and decryption
Article Introduction:There are a variety of front-end encryption algorithms that can be used for data encryption and decryption. This is a simple database-level data encryption and decryption solution. Taking the MySQL database as an example, it has built-in corresponding encryption function (AES_ENCRYPT()) and decryption function (AES_DECRYPT()).
2020-04-16
comment 0
4493

PHP password encryption and secure storage method
Article Introduction:With the continuous development and popularization of the Internet, the security of user passwords has attracted increasing attention when performing various operations online. As a commonly used server-side programming language, PHP also has its own set of implementation methods for password encryption and secure storage. This article will introduce how PHP encrypts and secures passwords, helping readers understand and protect their user passwords. 1. Password encryption Password encryption refers to converting user passwords to generate a seemingly random sequence of characters. Even if a hacker obtains this character sequence, it cannot be restored to
2023-06-30
comment 0
1043
What are the methods of password encryption?
Article Introduction:The methods of password encryption include: 1. Save in plain text; 2. Save with symmetric encryption algorithm; 3. One-way HASH algorithms such as MD5 and SHA1; 4. PBKDF2 algorithm; 5. Algorithms such as bcrypt and scrypt.
2020-08-11
comment 0
26192

PHP and SQLite: How to implement password encryption and verification
Article Introduction:PHP and SQLite: How to implement password encryption and verification Introduction: In the modern Internet era, the security of user passwords is particularly important. In order to protect users' privacy, websites generally use password encryption and verification methods to store and process users' password information. This article will introduce how to use PHP and SQLite database to implement password encryption and verification functions. 1. Password Encryption Password encryption refers to converting the user's plaintext password into a seemingly unreadable random string. Through this conversion process, even if the database is leaked,
2023-07-29
comment 0
538