Found a total of 327 related content
java框架的威胁建模最佳实践
Article Introduction:对于Java框架,威胁建模最佳实践包括:识别威胁:数据泄露、代码注入和服务拒绝等;分析威胁:评估可能性和影响;减轻威胁:实施加密、输入验证和防火墙等措施;使用威胁建模工具:例如ThreatModeler和OWASPThreatDragon。
2024-07-12
comment
553

Explore Python network security threat analysis cases
Article Introduction:Python is a powerful and flexible programming language with a wide range of applications in the field of cybersecurity. This article will introduce a case study of network security threat analysis application based on Python. With the rapid development of the Internet, network security threats are also increasing. Cyber attackers use a variety of sophisticated technical means to carry out attacks, so cyber security personnel need to identify and respond to these threats in a timely manner. Cybersecurity threat analysis is the process of identifying potential threats by collecting, analyzing, and interpreting network data. Python as a high-level
2023-07-01
comment 0
555

How to turn off virus and threat protection in Windows 10
Article Introduction:How to turn off virus and threat protection in Windows 10 is a problem encountered by some players. When users play various legendary games, the system will automatically activate virus and threat protection, identify the game as malware and then delete the protection. Then If you want to continue playing this game, there is only one way, and that is to turn off virus and threat protection, but this also reduces the security factor. Here is an introduction to how to turn off virus and threat protection in Windows 10. How to turn off virus and threat protection in Windows 10 1. Go to Windows Settings from the menu bar; 2. In Windows Settings, go to Security and Updates; 3. After turning it on, go to Windows Security Center, and then go to
2023-07-11
comment 0
3774
PHP安全实践:威胁建模在安全设计中的作用
Article Introduction:威胁建模是识别、分析和降低安全风险的关键做法,本文通过登录系统案例演示了威胁建模在PHP安全设计中的应用:威胁识别:使用STRIDE方法识别破坏性、篡改、抵赖等威胁。威胁分析:评估威胁的可能性和影响,确定高风险威胁。风险缓解:采取措施缓解风险,如使用强加密、防钓鱼措施和限制登录尝试。通过威胁建模,可以系统地提高PHP应用程序的安全性,防止潜在的攻击。
2024-06-10
comment 0
412
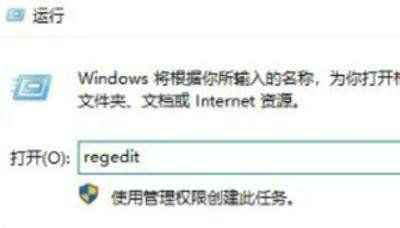
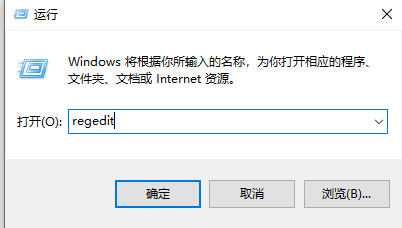
How to solve the problem when Windows 10 finds that threats cannot be dealt with? What should I do if a threat cannot be dealt with in Windows 10?
Article Introduction:When we use the security detection function in win10 system, we will find some existing threats, but what should we do if we find that the threats cannot be dealt with? It may be because there are file restrictions under the registry. Users can enter the WindowsDefender folder under the registry editor to make settings. Let this site carefully introduce to users how to deal with threats that cannot be dealt with in Windows 10. What should I do if Win10 finds that threats cannot be dealt with? Method 1. "Win+R" shortcut key to open Run, enter "regedit", and press Enter to open. 2. Enter the Registry Editor and click "HKEY_" on the left
2024-02-10
comment 0
447

PHP框架安全威胁的类型
Article Introduction:PHP框架中的安全威胁类型PHP框架的广泛使用,一方面给开发人员带来了便利,另一方面也带来了安全威胁。黑客可能利用框架中的漏洞发起攻击,从而窃取敏感数据、破坏系统或发动恶意活动。了解PHP框架中的安全威胁类型对于保护您的应用程序至关重要。常见安全威胁跨站点脚本(XSS):XSS攻击允许攻击者在受害者的浏览器中执行恶意脚本,窃取cookie、会话ID或其他敏感信息。SQL注入:SQL注入允许攻击者执行未经授权的SQL查询,修改数据库表或检索敏感数据。命令注入:命令注入攻击允许攻击者在
2024-06-01
comment
103
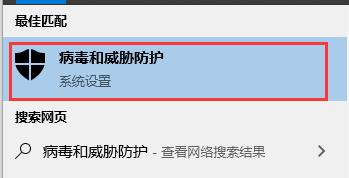
How to disable virus and threat protection in Windows 10?
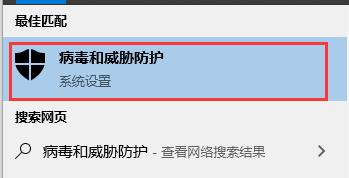
Article Introduction:Although the virus and threat protection function of win10 can help us block many viruses and protect the computer, it can also block many software and files by mistake, making it impossible for us to download and install them normally. At this time we need to temporarily turn off virus and threat protection. How to turn off virus and threat protection in win10 1. We can directly search for "virus and threat protection" in the search box in the lower left corner, and then turn it on. 2. Then click "Manage settings" under "Virus and threat protection settings". 3. Then just turn off all three options shown in the image.
2024-01-04
comment 0
823

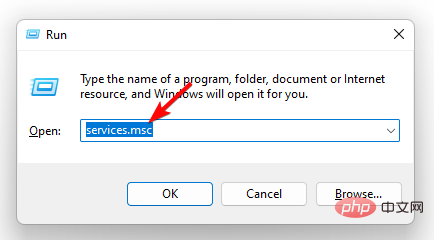
Example tutorial on how to turn off virus and threat protection in win10. Turn off virus and threat protection in win10
Article Introduction:Many users don’t know how to turn off virus and threat protection in win10. First, users open the settings option of win10 computer, click on the upgrade and security options, and then they can easily find the Windows Defender Security Manager option. Here, click on viruses and For the threat protection option, just turn off the power switches of the two options of real-time maintenance and cloud-based maintenance. In this way, people will turn off the virus and threat protection of win10. Example tutorial for turning off virus and threat protection in win10 1. Open the Win menu bar, click the [Settings] icon to enter the system configuration 2. Select [Update and Security] in the settings, and then click Enter 3. Open and enter [ WindowsDefender Security Manager], with
2023-07-07
comment 0
2863
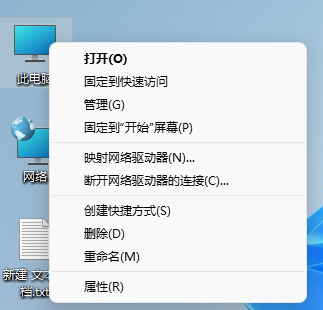
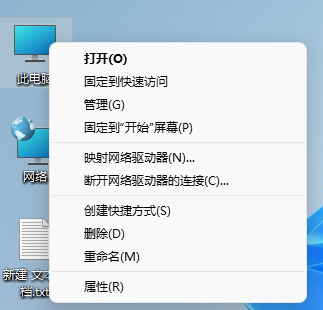
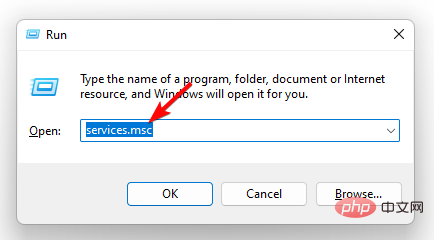
win11病毒和威胁防护怎么关闭?win11关闭病毒和威胁防护教程
Article Introduction:win11病毒和威胁防护如何关闭?很多人电脑的这个功能都是开启的状态,虽然能够很好的拦截下来各种微信的内容,可是我们网上下载的文件也会被拦截下来,那么这个问题应该如何解决呢,本期的win11教程就来和大伙分享解决方法,接下来让我们一起来看看详细的操作步骤吧。win11病毒和威胁防护如何关闭1、首先鼠标右击此电脑,然后选择属性。3、打开Windows安全中心,点击病毒和威胁防护。4、展开Microsoft,Defender防病毒选项,关闭定期扫描功能即可。
2024-07-17
comment
270

PHP框架开源社区如何应对安全威胁
Article Introduction:PHP框架开源社区应对安全威胁的方法包括:定期更新框架和组件,以修复已知漏洞。遵循安全编码指南,编写防范常见安全威胁的代码。进行安全审核,识别潜在漏洞。建立漏洞报告和披露机制,以便快速解决漏洞。传播安全意识,提高开发者对安全威胁的认识。
2024-06-14
comment
360
Artificial Intelligence and Cybersecurity Guard against Emerging Threats
Article Introduction:Threats against technology are also growing exponentially with technology. Cybercrime is big business; hackers are using increasingly sophisticated methods to break into systems and steal data. Artificial intelligence may be the answer to defeating these evil forces. AI can help identify new threats as they emerge in real time and even predict future attacks by employing machine learning algorithms and predictive analytics. Cybersecurity should be a top priority for organizations to protect digital assets and consumer data. For security teams, AI can be a powerful tool for network visibility, anomaly detection, and threat automation. Artificial Intelligence is Key to Detecting Emerging Cyber Threats As cyber threats rapidly evolve and sophisticate, artificial intelligence (AI) has become key to identifying and stopping cyber threats. Artificial intelligence systems can
2023-06-06
comment 0
489
Fix: Microsoft Defender Threat Service has stopped
Article Introduction:WindowsDefender is a built-in security solution in Windows. It protects your system from malware and other types of harmful threats. This makes Windows Defender your only security against threats if you don't have another antivirus program. If Windows Defender is not working, your system will be exposed to many vulnerabilities. Usually, when the threat service is stopped, you can click the "Restart" button, but this does not always work. Luckily, we've put together this article to help you solve this problem. Why did Windows Defender stop working? Windows Defender stops working most often
2023-04-30
comment 0
1691

Looking at the attack surface threats and management of AI applications from the STRIDE threat model
Article Introduction:STRIDE is a popular threat modeling framework that is widely used to help organizations proactively discover threats, attacks, vulnerabilities, and countermeasures that may impact their application systems. If you take apart each letter in "STRIDE", they represent counterfeiting, tampering, denial, information disclosure, denial of service and privilege enhancement. As the application of artificial intelligence (AI) systems gradually becomes a key component of the digital development of enterprises, many Security practitioners call for the need to identify and protect the security risks of these systems as soon as possible. The STRIDE framework can help organizations better understand possible attack paths in AI systems and enhance the security and reliability of their AI applications. In this article, security researchers use the STRIDE model framework to comprehensively map A
2023-10-13
comment 0
1036

Does Golang pose a threat to the C language?
Article Introduction:Does Golang pose a threat to the C language? In recent years, Golang, as an emerging programming language, has emerged in the field of software development and attracted much attention. At the same time, the C language, which has always been dominant, has always been one of the first choices for programmers. So, does Golang pose a threat to the C language? This article will explore this through specific code examples. First, let us take a look at the respective characteristics of Golang and C language. Golang is a programming language developed by Google that is simple, efficient and
2024-03-05
comment 0
642

Share network security threat intelligence analysis skills written in Python
Article Introduction:Network security threat intelligence analysis technology written in Python shares network security threats that have always been an important issue in today's Internet field. With the continuous development of technology, hacker attack methods are becoming more and more complex and hidden, and enterprises and individual users are facing more and more network security threats. In order to better deal with these threats, network security experts have been continuously working hard to research and develop various technical means to protect our network security. In the field of network security, threat intelligence analysis is a very important task. By analyzing and mining the web
2023-06-30
comment 0
509

Log analysis and threat detection in Linux environment
Article Introduction:Introduction to log analysis and threat detection in Linux environment: With the rapid development of the Internet, network attacks have become a problem that cannot be ignored. To protect our networks and systems from attacks, we need to analyze logs and perform threat detection. This article will introduce how to perform log analysis and threat detection in a Linux environment, and provide some code examples. 1. Introduction to log analysis tools In the Linux environment, we usually use some open source log analysis tools to help us analyze log files. Among the most commonly used tasks
2023-07-28
comment 0
1171
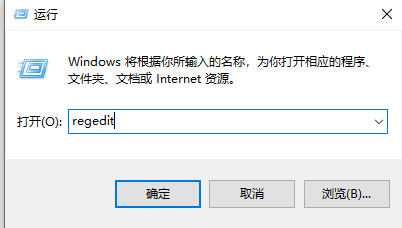
What to do if a threat is detected but cannot be removed in Windows 10?
Article Introduction:What to do if a threat is detected but cannot be removed in Windows 10? Some of our users have detected some threatening content on their computers, but they have tried many methods and are unable to clean it out. This happens because there is an extra file in our registry, so it cannot be cleared. The situation arises. In response to this problem, today's win10 tutorial will answer it for everyone. Users in need can come to this site to view the complete steps. Solution to the problem that Win10 cannot clear threats: 1. "Win+R" shortcut key to start running, enter "regedit" and press Enter to open. 2. After entering the registry editor interface, change "HKEY_LOCAL_MA
2024-02-11
comment 0
874
What security threats to operating systems do not include
Article Introduction:The security threats faced by the operating system do not include "information shielding". Improper use of the system by users is one of the main factors that threatens the security of the operating system; this includes damage to system resources caused by legitimate users due to misoperation, as well as malicious Attackers pretend to be legitimate users to attack and damage the system.
2022-10-31
comment 0
4157
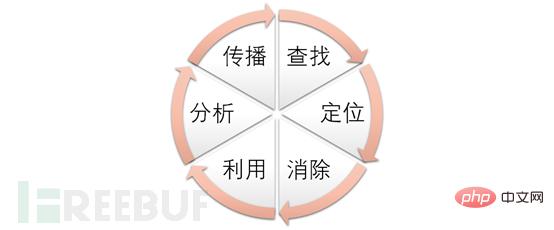
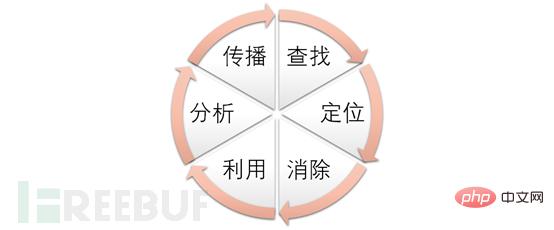
How to analyze APT Trojans based on the threat intelligence cycle model
Article Introduction:About the Threat Intelligence Processing Cycle Model The term "Threat Intelligence Processing Cycle" (F3EAD) originates from the military. It is a method for organizing resources and deploying troops designed by the US Army's commanders at all levels of the main combat arms. The Network Emergency Response Center draws on this method and processes threat intelligence information in the following six stages: Threat Intelligence Processing Cycle Application of the F3EAD Threat Intelligence Processing Cycle Model Step 1: Find a date on a certain month and deploy it on the partner's public cloud server The "Onion" system alarm found a suspected Trojan horse program, so the emergency response team quickly started the emergency response process: stakeholders and others gathered the group with one click and called in. The victim system is isolated for investigation. The security system and audit logs are exported for traceability analysis. Preparation of business system architecture and code-related information to analyze intrusion breaches and victims
2023-05-14
comment 0
1448
PHP Code Security: Threats in Service-Oriented Architecture (SOA)
Article Introduction:PHP code security in service-oriented architecture (SOA) faces threats such as SQL injection, cross-site scripting (XSS), remote code execution (RCE), and data leakage. To mitigate these threats, best practices include input validation, output encoding, using secure functions, restricting access to sensitive data, and regularly updating components.
2024-05-11
comment
646