# As open source products become more and more popular, as a Linux operation and maintenance engineer, it is crucial to be able to clearly identify whether an abnormal machine has been invaded. Based on my own work experience, I have compiled a few A common situation where a machine is hacked is for reference: Background information: The following situation is viewed on a CentOS 6.9 system, and is similar to other Linux distributions.
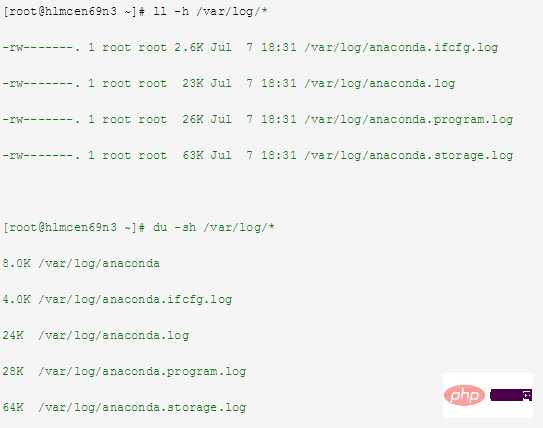
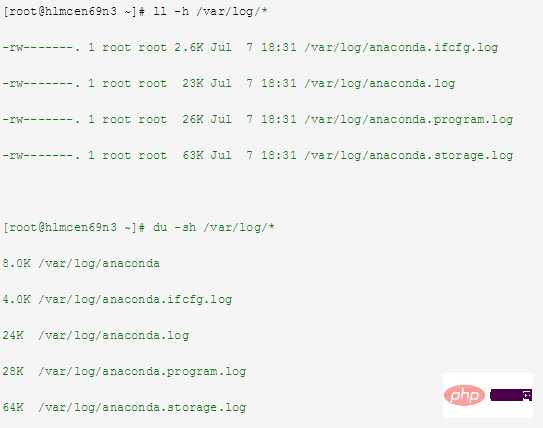
1Intrudermay delete the log information of the machine
You can check whether the log information still exists or whether it has been cleared, related commands Example:
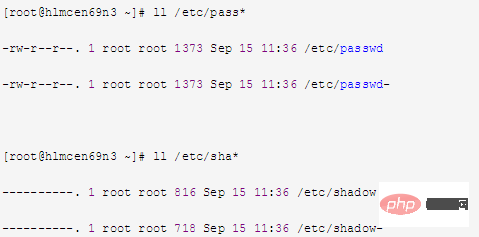
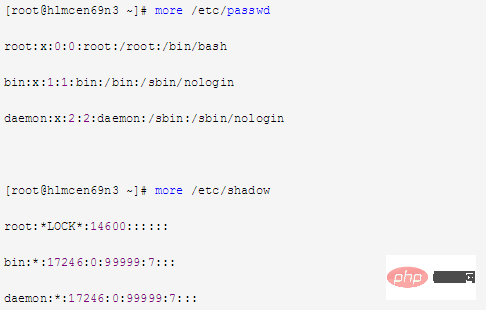
##2Intrudermay create a new file to store username and password
##You can view /etc/passwd and /etc/ shadow file, related command examples:
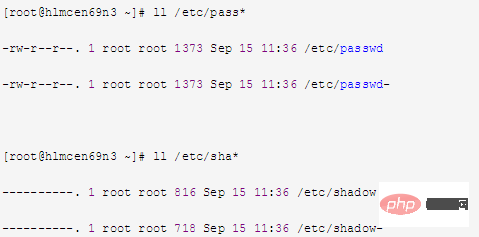
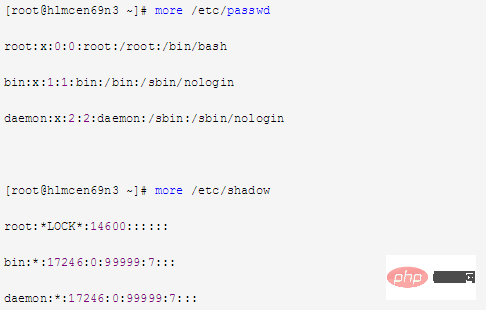
##3
Intrudermay modify username and password files##Can view /etc/passwd and /etc/shadow To identify the file content, related command examples:
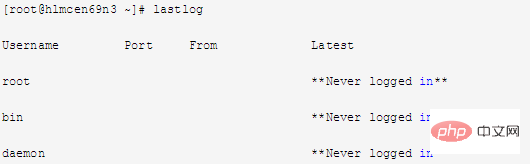
##4
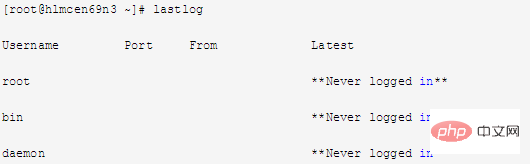
View The latest successful login event of the machine and the last unsuccessful login event corresponds to the log "/var/log/lastlog", related command examples:
5
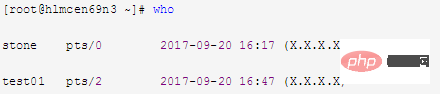
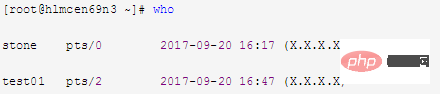
##View all users currently logged in to the machine
corresponds to the log file "/var/run/utmp", related command examples:
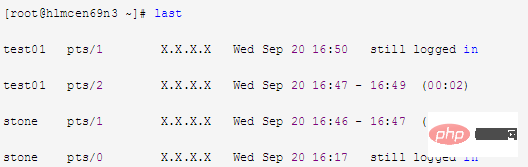
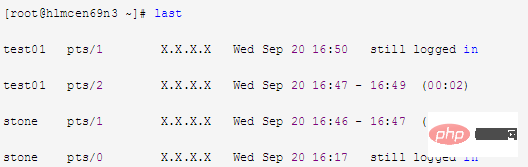
##6ViewMachineThe corresponding logs of users
who have logged in since the server was created File "/var/log/wtmp", related command examples:
In addition, search the public account Linux to learn how to reply "git books" in the background, and get a surprise gift package.
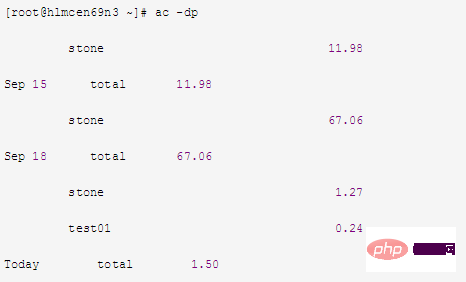
7
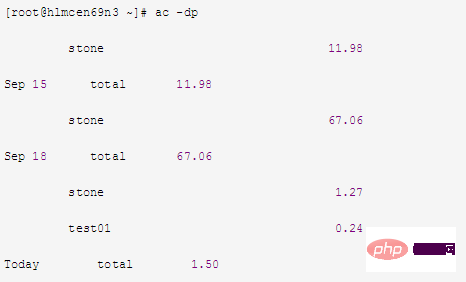
ViewThe connection time (hours) of all users of the machinecorresponds to the log file "/var/log/wtmp", related Command example:
##8
If finds that the machine generates abnormal trafficYou can use the command "tcpdump" to capture network packets to view the traffic situation or use tools" iperf" Check the traffic situation
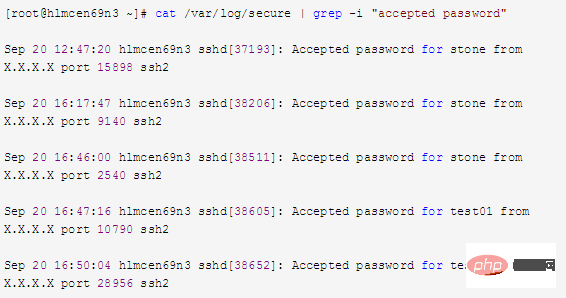
9
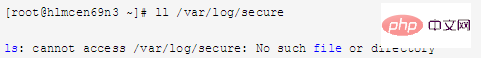
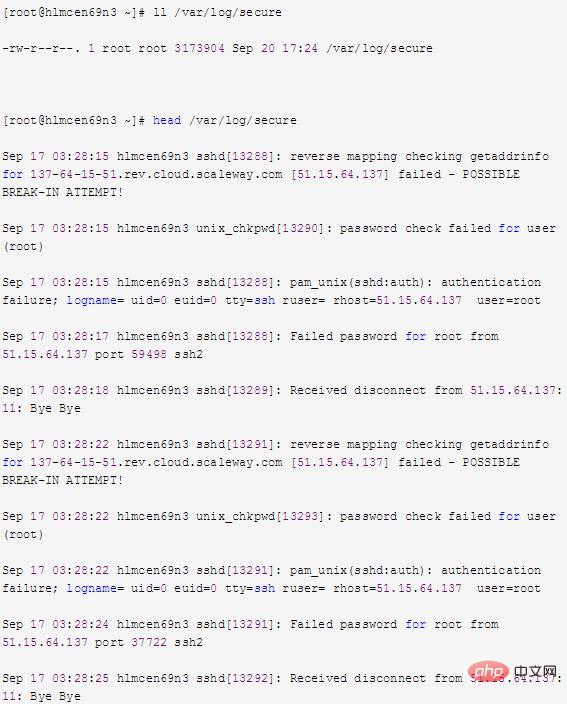
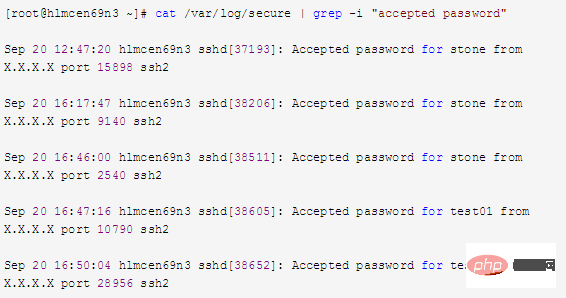
##You can view /var/log/secureLog file Try to find information about the intruder, related command examples:
10
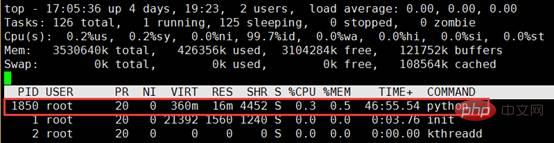
Query the execution script file corresponding to the abnormal process
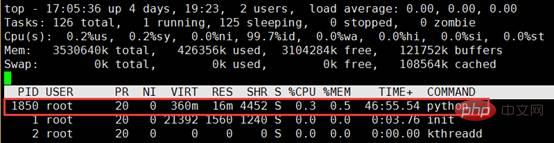
a.top command Check the PID corresponding to the abnormal process
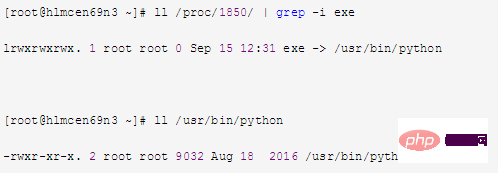
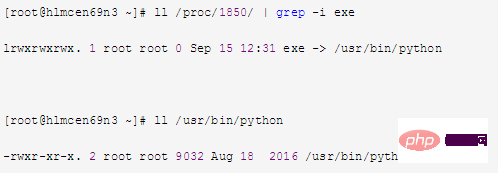
b. Find the executable file of the process in the virtual file system directory Follow Linux Chinese Community
11
If it is confirmed that the machine has been invaded and important files have been deleted, you can try to retrieve the deleted files Note: 1. When a process opens a file, as long as The process keeps the file open and even if it is deleted, it still exists on the disk. This means that the process is not aware that the file has been deleted, and it can still read and write to the file descriptor given to it when it was opened. This file is not visible except to the process because its corresponding directory inode has been deleted. 2. In the /proc directory, it contains various files reflecting the kernel and process tree. The /proc directory mounts an area mapped in memory, so these files and directories do not exist on the disk, so when we read and write these files, we are actually getting them from memory. Related Information. Most of the information related to lsof is stored in directories named after the process's PID. That is, /proc/1234 contains information for the process with PID 1234. Various files exist in each process directory that allow applications to easily understand the process's memory space, file descriptor lists, symbolic links to files on disk, and other system information. The lsof program uses this and other information about the kernel's internal state to produce its output. Therefore, lsof can display information such as the file descriptor and related file name of the process. That is, we can find relevant information about the file by accessing the file descriptor of the process. 3. When a file in the system is accidentally deleted, as long as there are still processes in the system accessing the file at this time, we can use lsof to retrieve the file from the /proc directory. to restore the contents of the file. Assuming that the intruder has deleted the /var/log/secure file, the method of trying to restore the /var/log/secure file can be as follows: a. Check the /var/log/secure file and find that the file no longer exists
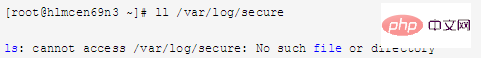
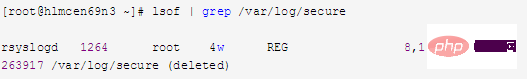
b. Use the lsof command to check whether A process opens /var/log/secure,
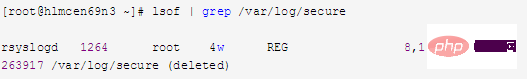
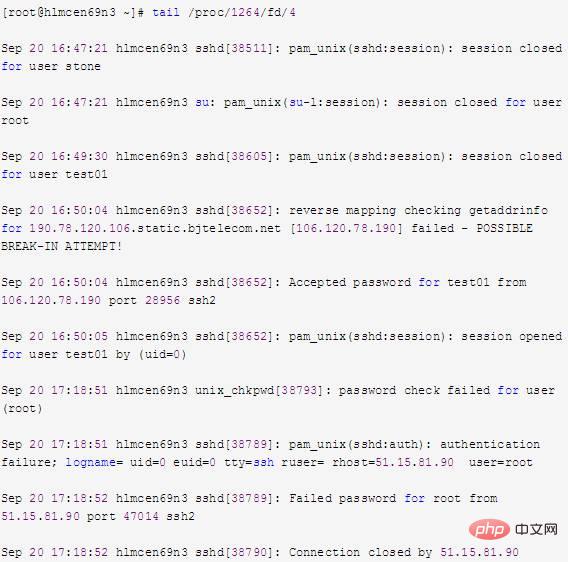
c. From the above information, you can see that the file descriptor of the file opened by PID 1264 (rsyslogd) is 4. You can also see that /var/log/secure has been marked as deleted. Therefore, we can view the corresponding information in /proc/1264/fd/4 (each numerically named file under fd represents the file descriptor corresponding to the process), as follows: 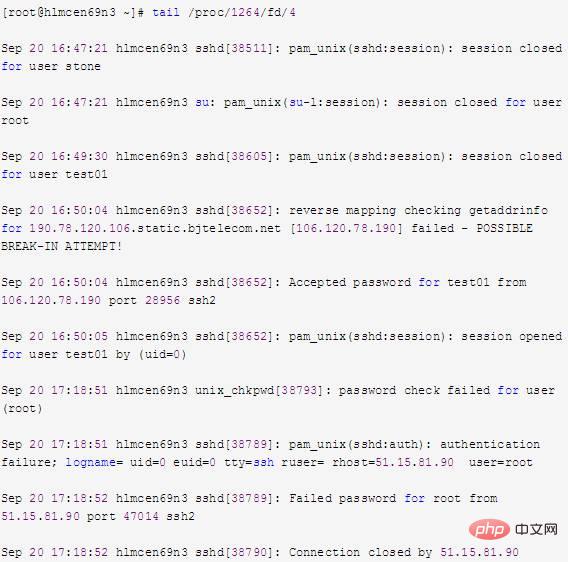
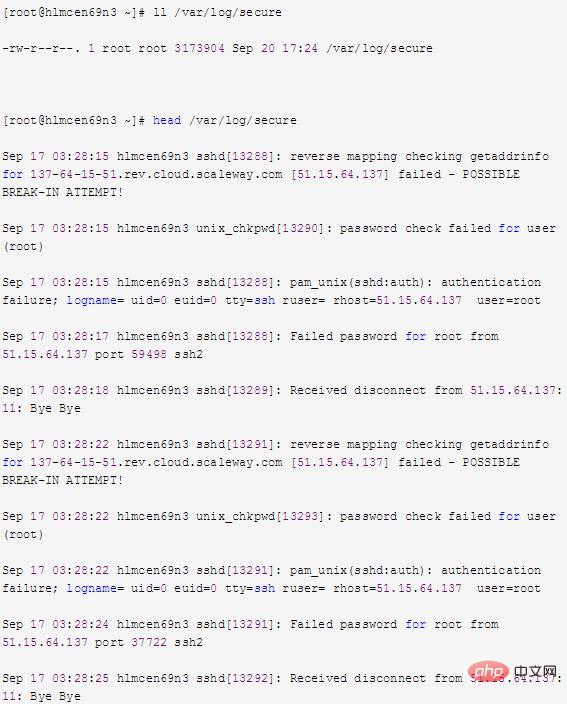
d. As can be seen from the above information, the data to be recovered can be obtained by viewing /proc/1264/fd/4. If the corresponding data can be viewed through the file descriptor, then I/O redirection can be used to redirect it to the file, such as:

# #e. Check /var/log/secure again and find that the file already exists. This method of recovering deleted files is very useful for many applications, especially log files and databases.
The above is the detailed content of Linux - 11 steps to teach you how to perfectly check whether your server has been compromised. For more information, please follow other related articles on the PHP Chinese website!