Found a total of 1728 related content

How to implement base64 encryption in php
Article Introduction:In PHP, you can use the base64_encode() function to implement base64 encryption. This function can base64 encode string data with the syntax "base64_encode($data)"; if the encryption is successful, a base64-encoded string will be returned, and if it fails, False will be returned.
2021-09-28
comment 0
11012
The principle of Base64 encryption and its implementation method in PHP
Article Introduction:Base64 is an encoding method that encodes binary data into ASCII characters. It can convert any content (such as pictures, files) into a readable string. Base64 is widely used in email, web pages, apps and other fields, and is also one of the common encryption methods in PHP. This article will introduce the principle of Base64 encryption and its implementation method in PHP. 1. Base64 encryption principle The principle of Base64 is very simple. It takes 3 8-bit bytes (i.e. 24 bits) as a group, and each group is divided into 4 6-bit bytes (i.e. 18 bits), and then
2023-04-03
comment 0
1374
How to use base64 command to encrypt linux command and execute it
Article Introduction:1. Encrypt the command echo "ls-l" | 2. Decrypt the command and execute echobHMgLWwK | base64-d | At this time, you can only see the echo of the command, but not the command itself. What versions of Linux are there? Linux versions include: Deepin, UbuntuKylin, Manjaro, LinuxMint, Ubuntu and other versions. Among them, Deepin is one of the best-developed Linux distributions in China; Ubuntu Kylin is a derivative distribution based on Ubuntu; Manjaro is a Linux distribution based on Arch; LinuxMint's default Cinnamon desktop is similar to Win
2023-05-17
comment 0
1736

What are the encryption methods in php?
Article Introduction:PHP encryption methods include: 1. MD5 encryption method; 2. Crype encryption method; 3. Sha1 encryption method; 4. URL encryption method; 5. Base64 information encoding encryption method, etc.
2020-11-26
comment 0
6259
What are the six password encryption methods in php?
Article Introduction:The six password encryption methods in php are: 1. MD5 encryption; 2. Crype encryption; 3. Sha1 encryption; 4. URL encryption; 5. Base64 information encoding encryption; 6. phpass.
2021-02-12
comment 0
3893
What are the encryption methods in php?
Article Introduction:The encryption methods in php include: using MD5() for encryption, using Crype() for encryption, using Sha1() for encryption, using the urlencode() function for url encryption, using the base64_encode() function for Base64 information encoding encryption, etc.
2020-04-24
comment 0
1468

How to solve the php encryption garbled problem
Article Introduction:The solution to the garbled characters in PHP encryption: first encrypt the ciphertext with MD5; then use base64 encryption to avoid garbled characters. The code statement is "$bs_test = base64_encode($test);".
2020-11-20
comment 0
2992
What are the commonly used encryption algorithms in PHP?
Article Introduction:With the development of the Internet, data security has become a serious issue that we must pay attention to in our daily work. Encryption becomes especially important when it comes to sensitive personal information or business data. In PHP development, some encryption algorithms are widely used. Let's take a look at the encryption algorithms commonly used in PHP. 1. Base64 encoding Base64 encoding is often used to transmit binary data in web pages or emails, because web pages or emails can only transmit string type data and cannot directly transmit binary data. Base64 is a solution
2023-05-12
comment 0
1236

What are the commonly used encryption and decryption tools in Java function libraries?
Article Introduction:The Java function library provides a wealth of encryption and decryption tools, including JCE, JCA, Apache CommonsCrypt, etc. JCE provides encryption algorithms and functions, JCA provides interfaces to access encryption service providers, and Apache CommonsCrypt contains more encryption algorithms and tools. The practical case shows how to use JCE to AES encrypt text and generate Base64-encoded ciphertext.
2024-05-05
comment 0
889
How to use PHP functions for data encryption and decryption?
Article Introduction:How to use PHP functions for data encryption and decryption? Overview Data encryption and decryption is an important means of protecting sensitive information. In PHP, we can use some functions to implement data encryption and decryption operations. This article will introduce how to use PHP functions for data encryption and decryption, and provide corresponding code examples. Simple encryption and decryption using base64_encode and base64_decode functions The base64_encode function can encode a string into base64 format
2023-07-26
comment 0
398
How to encrypt and decrypt data in PHP?
Article Introduction:PHP is an open source server-side programming language widely used in the field of web development. Since web applications often involve users' sensitive information, such as passwords, bank card numbers, etc., it is particularly important to encrypt and decrypt this information. This article will introduce how to encrypt and decrypt data in PHP, mainly including the following: Commonly used encryption algorithms and their characteristics Using MD5 encryption in PHP Using sha1 encryption in PHP Using base64 encoding in PHP Using ope in PHP
2023-05-12
comment 0
1494

What should I do if php encryption cannot be used?
Article Introduction:In the Internet era, information security issues are receiving more and more attention. In web development, data transmission is an essential link. In order to protect user privacy, we usually encrypt sensitive information before transmitting it. As a scripting language, PHP is widely used in web development, but in actual applications, some developers will find that its encryption function is not available. This article will analyze and solve this problem. 1. Introduction to PHP encryption PHP provides a variety of encryption algorithms, such as md5, sha1, base64, etc. Among them, md5 and sha1 algorithms are the most common
2023-03-31
comment 0
270

Data encryption function of PHP function
Article Introduction:With the popularity of the Internet and the rapid development of applications, data security issues have gradually become prominent. In web development, it is often necessary to encrypt certain sensitive data to prevent network attacks and data leaks. In order to solve this problem, PHP provides many encryption functions, the most commonly used of which are md5, sha1 and base64. Next, we will introduce how to use these functions and the differences. 1. md5 function md5 is a commonly used encryption algorithm that can convert messages of any length into a 128
2023-05-18
comment 0
1612
What are the php encryption algorithms?
Article Introduction:PHP encryption algorithms include MD5 algorithm, SHA algorithm, AES algorithm, RSA algorithm, Base64 encoding, DES algorithm, RC4 algorithm, Blowfish algorithm, etc. Detailed introduction: 1. MD5 algorithm, used to convert data of any length into a fixed-length hash value. In PHP, you can use the md5() function to calculate the MD5 hash value of a string; 2. SHA algorithm, including SHA -1. SHA-256, SHA-512, etc. These algorithms have corresponding functions in PHP; 3. AES algorithm, etc.
2023-08-31
comment 0
563

How to encrypt cryptocurrency
Article Introduction:Cryptocurrencies use advanced encryption technologies to ensure security: 1. Hash algorithm; 2. Asymmetric encryption; 3. Symmetric encryption; 4. Blockchain; 5. Smart contracts
2024-04-26
comment

The Meaning of Cryptocurrency in Cryptocurrency
Article Introduction:Encryption in cryptocurrency refers to the use of encryption technology to protect the security of transactions and information. Plain text is converted into cipher text through encryption algorithms, which can only be read by the owner of the key. Cryptocurrencies make extensive use of cryptographic technologies, including hash functions, digital signatures, asymmetric encryption, and blockchain, to ensure transaction security, privacy, immutability, and transparency.
2024-04-26
comment

How cryptocurrencies are encrypted
Article Introduction:Cryptocurrencies are encrypted using hash functions, digital signatures, asymmetric encryption and blockchain technology to ensure that transaction and account information are secure and tamper-proof.
2024-04-26
comment
How to encrypt tables
Article Introduction:How to encrypt the table: first click the "File" menu bar and select "Information"; then click "Protect Workbook" and select "Encrypt with Password" in the pop-up drop-down list; finally enter the created password in the text box File password, click "OK".
2021-03-10
comment 0
70665
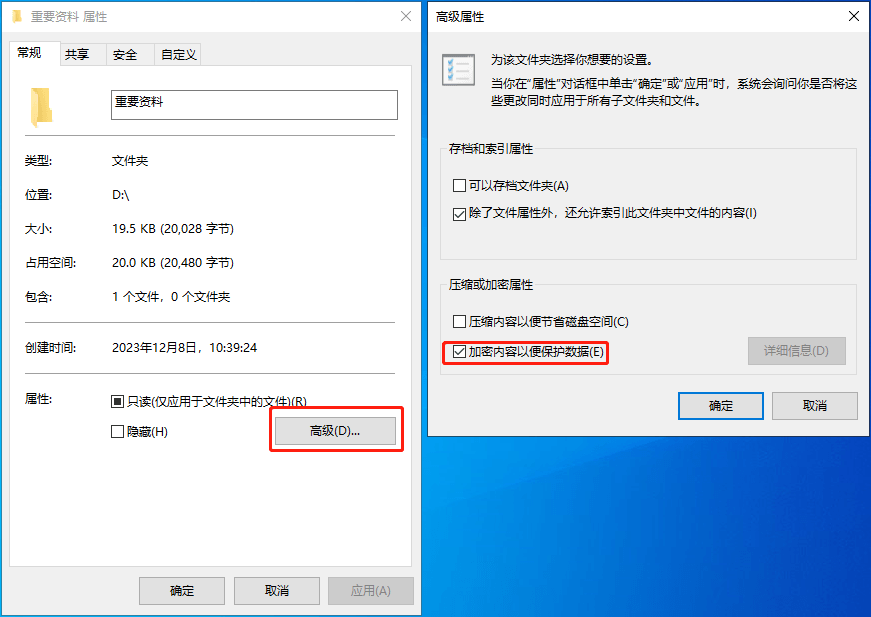
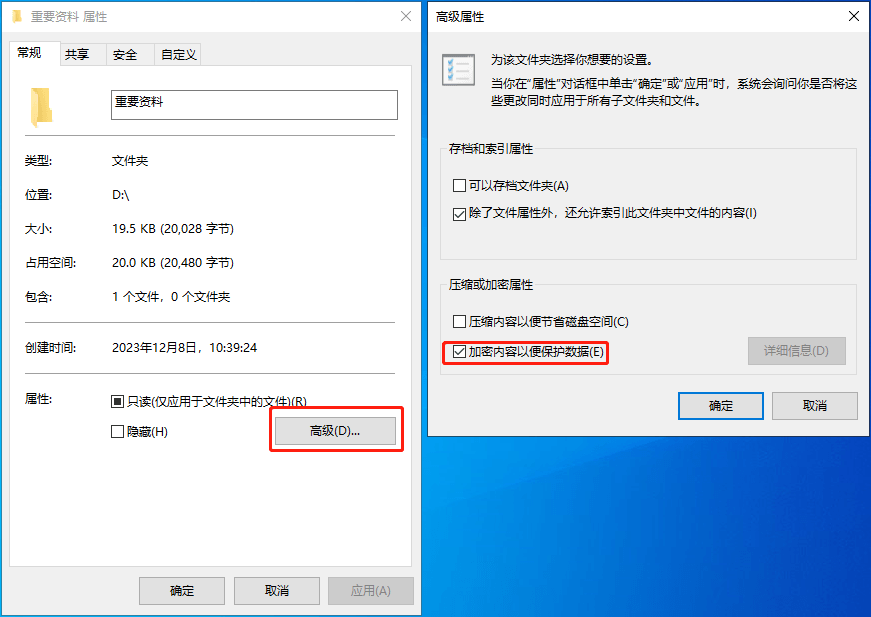
Windows文件加密EFS加密,电脑文件夹怎么加密
Article Introduction:EFS是Windows加密文件系统,对于NTFS卷上的文件和数据,都可以直接被操作系统加密保存,在很大程度上提高了数据的安全性。下面小编来说说如何使用Windows文件加密功能EFS。EFS在哪些情况下会导致拒绝访问1、重装系统2、系统帐户删除3、证书被删除重要的事情说三遍:加密后一定要备份好证书!重要的事情说三遍:加密后一定要备份好证书!重要的事情说三遍:加密后一定要备份好证书!开启文件夹加密在文件夹右键“属性”,点“高级”,勾上“加密内容以保护数据”,确定后,选择“将更改应用于此文件夹、子文件夹和文件
2024-06-19
comment
407