Found a total of 3451 related content

The impact of trusted computing technology on personal privacy
Article Introduction:With the popularization of the Internet and the acceleration of digital life, personal privacy has become the focus of social attention. Whether in daily life or in the digital world, our personal privacy faces different security risks. In order to protect personal privacy, trusted computing technology has been widely used in cloud computing, Internet of Things, big data analysis and other fields. This article will explore the impact of trusted computing technology on personal privacy. 1. Definition and principles of trusted computing technology Trusted computing technology refers to ensuring the credibility, integrity and integrity of computing processes and results in computer systems.
2023-06-11
comment 0
582
Application practice of privacy computing in the field of big data AI
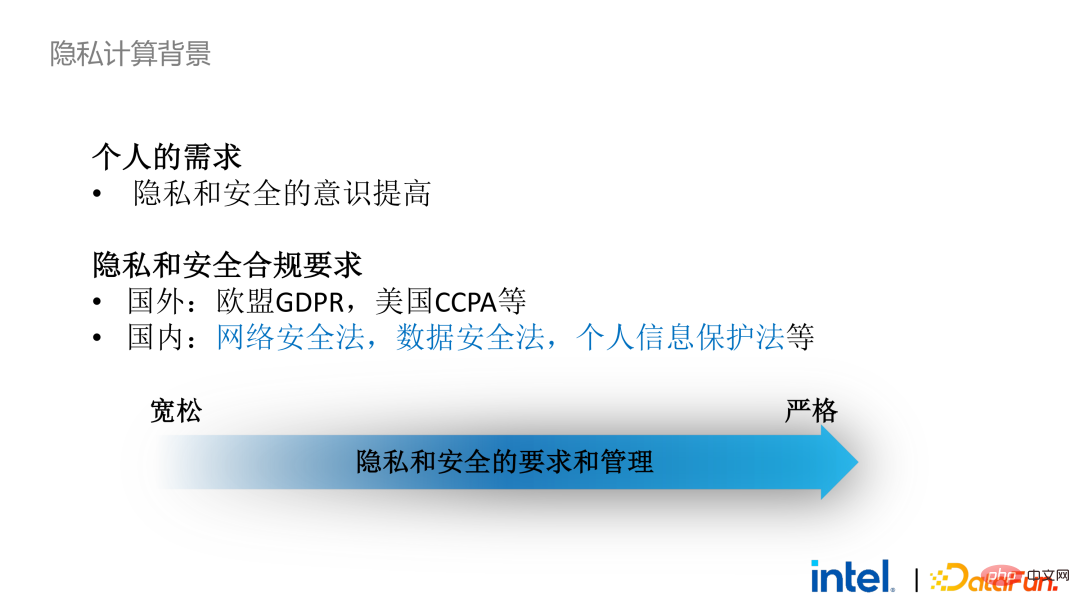
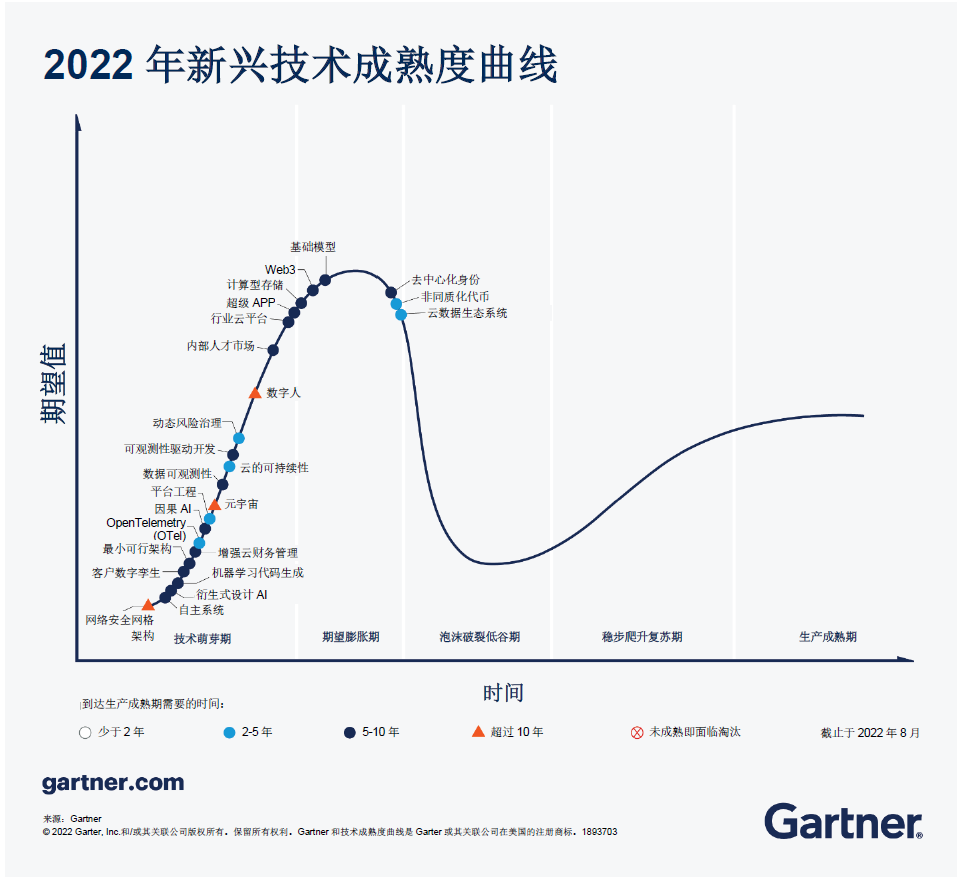
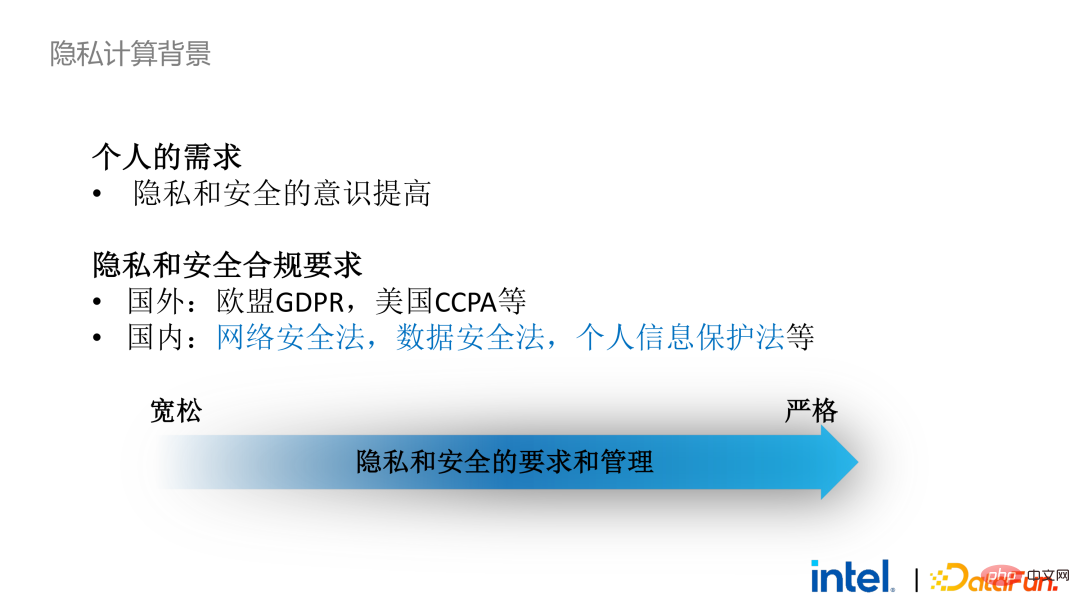
Article Introduction:01 Background and Current Situation of Privacy Computing 1. Background of Privacy Computing Privacy computing has now become a necessity. On the one hand, individual users’ demands for personal privacy and information security have become stronger. On the other hand, there are a large number of privacy and security-related laws and regulations issued, such as the European Union’s GDPR, the United States’ CCPA and domestic personal information protection laws. Regulations and policies have gradually changed from loose to strict, mainly reflected in rights and interests, implementation scope and execution. Strength, etc. Taking GDPR as an example, since it came into effect in 2018, more than 1,000 cases have emerged, with a total fine of more than 11 billion, and the highest single fine exceeds 5 billion (Amazon). 2. Current status of privacy computing In this context, data security has changed from optional to mandatory. This results in a large number of
2023-04-28
comment 0
1104

Application of trusted computing technology in the field of data privacy protection
Article Introduction:With the rapid development of digitization and networking, big data has become an indispensable resource in today's Internet era. But at the same time, the risk of personal privacy leaks also increases. In order to protect data security and privacy, trusted computing technology emerged as the times require. This article will explore the application of trusted computing technology in the field of data privacy protection. First, we need to understand the concept of trusted computing technology. Trusted computing technology refers to establishing a protection mechanism for computing tasks and computing results through various means such as hardware, software, and protocols when performing computing tasks in an untrusted environment.
2023-06-11
comment 0
883

The relationship between trusted computing technology and privacy protection
Article Introduction:With the rapid development and popularization of the Internet, people increasingly rely on the network to transmit, store and process data. The ensuing problem is data security and privacy protection. Trusted computing technology emerged as the times require, and this technology has been widely used and promoted. So what is the relationship between trusted computing technology and privacy protection? Let’s explore it together. The basic concept of trusted computing technology refers to ensuring the integrity and credibility of calculation results during the calculation process. Simply put, it is to ensure that the data and programs used as input and output are not tampered with or stolen.
2023-06-11
comment 0
858
Federated Learning in Privacy Computing
Article Introduction:Data assets have become a key tool in product and service design, but centralized collection of user data puts personal privacy at risk and, in turn, exposes organizations to legal risks. Starting in 2016, people began to explore how to use the ownership and origin of data under the protection of user privacy, which made federated learning and federated analysis a hot spot of concern. As the scope of research continues to expand, federated learning has begun to be applied to broader fields such as the Internet of Things. So, what is federated learning? Federated learning is a machine learning setup in which multiple entities collaborate to solve machine learning problems under the coordination of a central server or service provider. Raw data for each client is stored locally and is not exchanged or transferred; instead, it is implemented using focused data updates for instant aggregation
2023-04-29
comment 0
1204
解读Aleo最新算法Synthesis Puzzle:引领Web3隐私革命
Article Introduction:Aleo是一个专注于隐私保护的区块链项目,通过零知识证明技术(ZKP)实现更高的隐私和可扩展性。Aleo的核心理念是让用户能够在不泄露个人数据的前提下进行身份验证和数据处理。本文主要介绍了Aleo的项目概要及最新进展,对市场十分关心的puzzle算法更新做了详细的解读。最新算法抢先看;)TLDRAleo网络每小时随机生成一个ZK电路;矿工在这一小时内需要尝试不同的nonce作为电路的输入,计算出witness(即电路中的所有变量,这个计算过程也叫synthesize),对witn
2024-06-29
comment 0
765

Where are the privacy settings in win7? How to open the privacy settings in win7
Article Introduction:Where are the privacy settings in win7? How to open the privacy settings in win7? Recently, many friends need to open the privacy settings when using the win7 system, but they don't know how to do it. First we click on the Start icon, then click on Control Panel Options, then change the category and select the small icon, and finally click on Internet Options to change the properties. Next, this site will take you to learn more about the privacy settings of win7. How to open privacy settings in win7: 1. Click the "Start" icon in the lower left corner of the computer desktop to open the Start menu dialog box. Look for the "Control Panel" option in the Start dialog box and click on it. 2. After clicking the Control Panel menu option, the system will open the "Control Panel" session.
2024-01-26
comment 0
346

Linyu open source the first industrial-grade multi-party secure data analysis system SCQL: 'easy to use' private computing like writing SQL
Article Introduction:Linyu open source the first industrial-grade multi-party secure data analysis system SCQL, which fills the gap in the industry and will further extend the link of data security collaboration and expand the scenarios of data value circulation. The rise of large models has once again profoundly recognized the importance of data as a new production factor. As an important path to balance data utilization and data security, privacy computing has further highlighted its academic and application values. In recent years, driven by policy and market demand, private computing technology and industry have developed steadily and have been applied in many fields such as finance, communications, the Internet, government affairs, and medical care. But overall, due to issues such as technical thresholds and construction costs, there are truly large-scale production applications, but the number is very small. On March 29, the first Hidden Language Open Source Society
2023-04-04
comment 0
578
How to use trusted computing technology to build a multi-party secure computing system?
Article Introduction:In modern society, ensuring privacy and security has always been an important issue. The development of computer technology enables people to perform various forms of calculations on the network, thus bringing great convenience and innovation to digital life. However, the openness of computer networks and the easy leakage of information also make it necessary to adopt corresponding technical means to ensure the privacy and security of multi-party data calculations. To this end, trusted computing technology emerged. It can not only meet the current needs of big data applications, but also ensure the efficiency of multi-party data calculations while ensuring data privacy.
2023-06-11
comment 0
873

OnePlus 9 Cancel Privacy Password_OnePlus 9 Privacy Password Method
Article Introduction:1. Open the phone settings and click Privacy. 2. Select App Lock and click the settings icon in the upper right corner. 3. Click to modify the privacy password and related settings. 4. Enter the privacy password to enter, and click to close the privacy password. 5. Click to close. 6. Or in settings, click Fingerprint, Face and Password, click Privacy Password, and turn off Privacy Password.
2024-03-23
comment
943
Born for data, fighting for privacy: the accelerated rise of the private computing industry
Article Introduction:In the era of digital economy, data, as a new production factor and strategic resource, is an important driving force for scientific and technological progress, policy formulation and economic development. However, the value of data can only be maximized if privacy and security are guaranteed. In recent years, with the promulgation and implementation of the "Cybersecurity Law", "Data Security Law" and "Personal Information Protection Law", the state, industry and local governments have successively issued a series of supporting policy documents related to data security to improve the data element governance system. , ensuring the security of data circulation transactions. In particular, the "Twenty Data Articles" released at the end of 2022 have further promoted the compliant and efficient circulation and use of public data, corporate data, and personal data. Data "usable but not visible" and "controllable and measurable" have become legal requirements. In promoting the implementation of the twenty concepts of data
2023-05-17
comment 0
734

How to set privacy on Migu video
Article Introduction:As a popular video application, Migu Video attaches great importance to the protection of users' personal information and privacy. Its privacy permission setting function is designed to meet users' needs for privacy protection. Many users may still not know how to find the privacy settings in Migu Video. So below, the editor of this website will bring you a detailed introduction to the location of privacy settings. Users who want to know more, please come here Read this article to find out more. How to set privacy on Migu Video 1. Open the Migu Video app and click My in the lower right corner. 2. Click My Settings. 3. Click Privacy Settings. 4. Click to enter the privacy settings.
2024-04-26
comment
671

What is trusted computing technology?
Article Introduction:With the rapid advent of the digital era, the digital application field is facing more and more risks. Protecting data privacy, ensuring the accuracy of calculation results, and preventing hacker attacks have become huge challenges in the field of digital applications. In order to solve these problems, trusted computing technology emerged as the times require. Trusted computing technology is a technology that can provide safe and reliable calculations. During the calculation process, it can verify the accuracy of data, ensure the security and trustworthiness of the server, and improve the robustness of the system. Trusted computing technology realizes data protection, privacy protection, computing reliability, cloud security, etc.
2023-06-11
comment 0
1019

The increase has nearly tripled in 4 days. Can COTI, which launched a new technology solution, really increase the speed of privacy computing by a thousand times?
Article Introduction:Recently, the price of COTI has experienced a huge increase, from around US$0.093 on February 22 to around US$0.27 on the 26th, with the increase nearly tripling within 4 days. COTI’s surge was due to the launch of “garbled circuit” privacy technology. It is said that this technology can significantly increase the computing speed on the chain, reaching 1,000 times that of traditional encryption technology, and improve the transparency of data processing on the chain. The news ignited investor enthusiasm. The following will introduce the COTI project and its latest technical solutions. What does COTIV2 mean for privacy-preserving technology? How does the MPC agreement affect the COTI project itself? In the blockchain space, the balance of privacy and transparency is crucial. C
2024-03-24
comment 0
264

美柚怎么设置隐私 设置隐私的操作方法
Article Introduction:在美柚这个专注于女性健康与生活的平台上,我们深刻理解用户对于隐私保护的需求与重视。为此,美柚提供了详尽的隐私设置选项,让您能够全面控制个人信息的可见范围,确保您的隐私安全得到最大限度的尊重和保护。那么是如何设置隐私的呢?下面跟随我们去看看吧。设置隐私的方法步骤一:打开美柚app,点击右下角我。步骤二:点击右上角设置图标。步骤三:点击进入隐私设置即可。
2024-05-31
comment 0
657

Types of privacy public chains and introduction to some important privacy public chains
Article Introduction:For blockchain technology, expansion is no longer the only problem that needs to be solved. The next issue to be realized is privacy. This is also the main reason why the blockchain privacy track has become a hot topic. Currently, the public chain uses privacy chain technology. , mainly the two technologies of zero-knowledge proof and fully homomorphic encryption. For investors, what are the privacy public chains? Only by seizing the privacy track can you earn your first pot of gold. Currently, the most popular privacy public chains include PlatON, Aleo, Aztec, SecrerNetwork, etc. Next, the editor will introduce to you some of the larger privacy public chains. How many privacy public chains are there? Currently popular privacy public chains mainly include PlatON, Aleo, Aztec, and SecrerNetwor.
2024-01-24
comment 0
969

爱奇艺隐私政策怎么看 隐私政策查看方法
Article Introduction:大家在使用爱奇艺的时候,经常会选择自己想看的电视电影的,为保留自己观看电视电影等相关数据,用户就需要绑定自己手机号,注册一个爱奇艺账号。这时很多用户考虑到个人信息问题,想知道爱奇艺能保护用户那些隐私,就可以通过查看隐私政策,下面是小编整理的隐私政策查看方法,如大家有需要的话可以看看。爱奇艺隐私政策怎么看答:右上角方块-帮助-隐私政策1、打开爱奇艺,在主页点击右上角方块,如图所示。2、在下方弹出的菜单栏中,选择【帮助】,再选择【隐私政策】。3、最后点击隐私政策,自动打开浏览器,进入爱奇艺隐私政策页面。
2024-07-11
comment
128

全民k歌隐私权限怎么设置 隐私权限设置方法
Article Introduction:《全民k歌》隐私权限如何设置,有些用户比较在意个人隐私,不想让自己的作品或者歌房被其他用户查看到,想知道隐私权限在哪设置,下面一起去看看设置方法吧。全民k歌怎么设置隐私权限第一步,点击我的,点击设置图标。第二步,点击进入隐私权限选项。第三步,即可设置隐私权限。
2024-06-06
comment
210

汽水音乐怎么设置隐私 设置隐私的操作方法
Article Introduction:汽水音乐在设置隐私方面提供了多种选项,以确保用户在使用音乐服务时的个人信息安全和隐私保护。那么是如何设置隐私的呢?下面跟随我们去看看吧。汽水音乐设置隐私的操作方法1、打开汽水音乐app,点击右下角我的。2、点击右上角设置图标。3、点击隐私设置即可。
2024-05-31
comment
783

咪咕视频怎么设置隐私 设置隐私的操作方法
Article Introduction:在咪咕视频,我们深知您的隐私安全至关重要。因此,我们设立了全面的隐私设置选项,旨在为您提供一个安心、可控的观看环境。在会员中心的隐私设置模块,您可以灵活自定义个人资料的可见范围,选择是否公开观看历史、喜欢的视频列表,以及对评论和点赞的隐私权限进行管理,确保您的观影偏好不被无意分享。设置隐私的操作方法1、打开咪咕视频app,点击右下角我的。2、点击我的设置。3、点击隐私设置。4、点击进入隐私设置即可。
2024-05-31
comment
408