Found a total of 2526 related content
PHP Secure Programming Guide: Preventing Sensitive Files from Leaking
Article Introduction:PHP Security Programming Guide: How to Avoid Sensitive File Leakage Introduction: In today's digital era, with the rapid development of the Internet, information security issues are receiving more and more attention. Especially in website development, how to avoid the leakage of sensitive files has become an extremely important topic. This article will introduce you to some basic principles and techniques of PHP security programming to help developers avoid the risk of leaking sensitive files during the process of writing code. Part One: Understanding the Concept of Sensitive Files Before we start discussing how to avoid the leakage of sensitive files, we first need to clarify
2023-07-01
comment 0
614
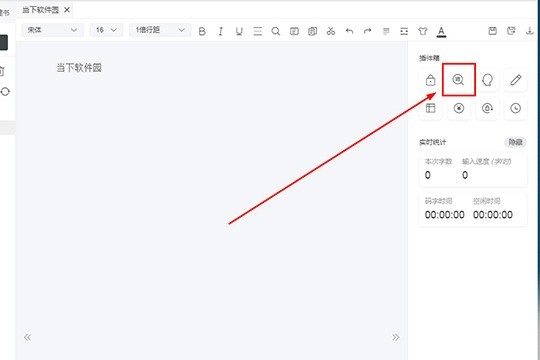
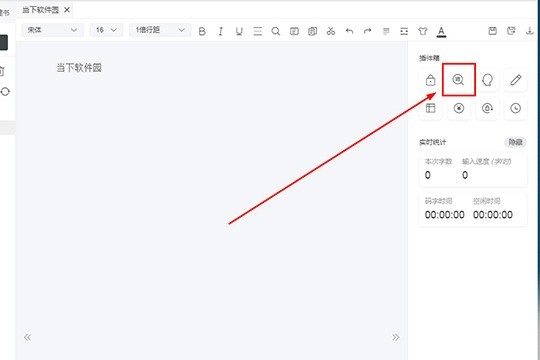
橙瓜码字怎么添加敏感词_让你更加放心的写作
Article Introduction:1、首先需要先进入到橙瓜码字软件中,敏感词功能非常的强大,它可以帮助用户解决由于误输入而引起内容不过审的问题,帮助用户在写作完成时能够对自己的文章有个全名的检查,把各种敏感词汇汇扼杀在摇篮中,小编随意点击某个书籍,进入到橙瓜码字的编辑器界面,用户可以点击右边插件箱内红框标注的【敏感词】功能,开始敏感词的添加,如下图所示:为了更好地调整文本内容,以下是重写的版本:2、弹出敏感词的设置界面,首先需要先设置替换方式,一共有六种替换方式供大家选择,你可以对检测到的敏感词进行字体颜色高亮、增加分隔线、增加竖线、将汉
2024-05-16
comment
928

How to handle and desensitize sensitive data in MySQL?
Article Introduction:How to handle and desensitize sensitive data in MySQL? As the Internet develops, data privacy and security protection become increasingly important. In the database system, the saved data may contain sensitive information of users, such as ID number, mobile phone number, bank account number, etc. In order to protect users' privacy while being able to use this data in business, we need to process and desensitize sensitive information. This article will introduce how to process and desensitize sensitive data in MySQL, and give corresponding code examples. Field data
2023-07-30
comment 0
2364

How SpringBoot implements filtering sensitive words
Article Introduction:Filter sensitive words 1. Create a text file to store the sensitive words to be filtered. First create a text file to store the sensitive words to be filtered. In the following tool class, we will read this text file. @PostConstruct//this is given in advance. The annotation indicates that when the container instantiates this bean (when the service is started), after calling the constructor, this method will automatically call publicvoidinit(){try(//Read files written with "sensitive words", getClass means compiling from the program After that, target/classes reads the configuration file. After reading, it is the byte stream //java7 syntax. At the end of the sentence here, the close statement InputS will be automatically executed.
2023-05-20
comment 0
1225
How to implement sensitive word filtering in laravel
Article Introduction:Laravel is a popular PHP framework that provides many powerful features such as routing, ORM, form validation, and more. In practical applications, many websites need to filter the content input by users for sensitive words to ensure the civility and health of the website. This article will introduce how to use Laravel to implement sensitive word filtering function. 1. Principle of sensitive word filtering Sensitive word filtering refers to detecting sensitive words in text content and replacing or marking them to achieve the purpose of blocking sensitive words. There are many ways to implement sensitive word filtering, the most commonly used of which is to use regular tables
2023-04-14
comment 0
4531

PHP form filtering: sensitive word filtering and replacement
Article Introduction:PHP form filtering: sensitive word filtering and replacement In the process of developing web applications, we often need to filter and clean the data submitted by users to protect the security of the website and the privacy of the users. Among them, filtering and replacing sensitive words is a very important task. This article will introduce how to use PHP to filter and replace sensitive words, and provide corresponding code examples. The principle of sensitive word filtering and replacement. Sensitive word filtering and replacement refers to detecting sensitive words contained in the data submitted by users and replacing them with specified words.
2023-08-09
comment 0
874

How to protect sensitive files of PHP website through security configuration files?
Article Introduction:How to protect sensitive files of PHP website through security configuration files? When developing and deploying PHP websites, protecting sensitive files is very important. By properly configuring your server and using security profiles, you can effectively prevent unauthorized access to sensitive files. This article will introduce how to protect sensitive files of PHP website through security configuration files. Configuring the Web Server First, we need to ensure that the Web server is configured correctly to prevent sensitive files from being accessed directly. Commonly used web servers include Apache and Ngin
2023-08-27
comment 0
314
How to implement sensitive word replacement in Python
Article Introduction:How to implement sensitive word replacement in python: first pour the sensitive word text; then when the user inputs the sensitive word and the match is successful, replace it with [*], the code is [new_string = string.replace(words,"*"*len(words) )].
2020-10-23
comment 0
16222

How to implement sensitive word replacement in php
Article Introduction:How to implement sensitive word replacement in PHP: first create a PHP sample file; then specify the sensitive word; then replace the sensitive word through the "strtr($bb, $badword1);" method; and finally output the replacement result through echo.
2020-08-08
comment 0
2916

How to replace sensitive words in php
Article Introduction:How to replace sensitive words in PHP: 1. Create a PHP sample file; 2. Define a form comment form; 3. Use "str_replace($word, "***", $pinglun);" to replace sensitive words in comments Just replace it with an asterisk.
2022-11-01
comment 0
1279

Is linux case sensitive?
Article Introduction:Linux is case-sensitive; for example, Mozilla, MOZILLA, mOzilla and mozilla are four different commands, but only mozilla is a truly valid command; and because UNIX systems and the C language have always been case-sensitive, the user's login Names and secrets are also case-sensitive.
2023-03-10
comment 0
1684

MySQL case-sensitive processing method
Article Introduction:MySQL case-sensitive handling methods and code examples MySQL is a commonly used relational database management system, which requires special attention when dealing with case-sensitive issues. In MySQL, it is case-insensitive by default, that is, it is not case-sensitive. But sometimes we need to perform case-sensitive processing, which can be achieved through the following methods. When creating databases and tables, specify the default character set as Bin (binary) type, so that the database will be case-sensitive. The specific operations are as follows: CREATE
2024-03-15
comment
505
Detailed introduction to the method of replacing specified characters in PHP (case sensitive)
Article Introduction:In the previous article, we learned about the method of replacing specified characters in a string. If you need it, please read "Replacing specified characters in PHP in one step (case insensitive)". This time we introduce to you another method of replacing specified characters in a string. You can refer to it if you need it.
2021-08-04
comment 0
2177
What are the sensitive exceptions in java
Article Introduction:Java sensitive exceptions include: 1. [java.io.FileNotFoundException] leaks the file system structure and file name enumeration; 2. [java.util.jar.JarException] leaks the file system structure.
2020-10-29
comment 0
7483

How to use Python for NLP to process PDF files with sensitive information?
Article Introduction:How to use PythonforNLP to process PDF files with sensitive information? Introduction: Natural language processing (NLP) is an important branch in the field of artificial intelligence, used to process and understand human language. In modern society, a large amount of sensitive information exists in the form of PDF files. This article will introduce how to use Python for NLP technology to process PDF files with sensitive information, and combine it with specific code examples to demonstrate the operation process. Step 1: Install the necessary Python libraries Before we begin, we need
2023-09-29
comment 0
609

How to use PHP bloom filter for sensitive word filtering
Article Introduction:How to Use PHP Bloom Filter to Filter Sensitive Words With the rapid development of the Internet, people often encounter some unpleasant remarks and inappropriate content when using various social platforms, forums and chat tools. In order to protect the user experience and maintain the health and order of the online environment, many websites and applications use sensitive word filtering technology. Sensitive word filtering is a method of using known sensitive words to check the text entered by the user to find and filter out the sensitive content. The traditional method of filtering sensitive words is mainly through string matching
2023-07-07
comment 0
1301

PHP learning steps: How to use sensitive word filtering
Article Introduction:PHP learning steps: How to use sensitive words to filter Introduction: In the Internet age, freedom of speech also brings the risk of information dissemination. In order to maintain the health of the network environment and provide a user-friendly experience, sensitive word filtering has become an indispensable part. This article will introduce the learning steps of using sensitive word filtering in PHP and provide corresponding code examples. Step 1: Establish a sensitive lexicon. To use the sensitive word filtering function, you first need to create a sensitive lexicon. The sensitive word library is a list containing all sensitive words to be filtered. OK
2023-08-19
comment 0
727

Secure Storage: Protect Sensitive Data on Your Linux Server
Article Introduction:Secure Storage: Protecting Sensitive Data on Your Linux Server Overview: In today’s digital age, data is one of the priceless assets of a business. Protecting sensitive data is critical to maintaining corporate reputation and complying with regulations. This article will explain how to securely store sensitive data on a Linux server to protect the confidentiality and integrity of the data. Background: On Linux servers, sensitive data is usually stored in the form of files, such as user credentials, database passwords, API keys, etc. This data is used for authentication, data encryption and access
2023-09-09
comment 0
671
How to handle sensitive data and privacy protection in PHP development
Article Introduction:How to deal with sensitive data and privacy protection in PHP development? Introduction: In today's digital era, privacy and data protection issues have received increasing attention. For PHP developers, handling sensitive data and privacy protection is a crucial task. This article will introduce some best practices for handling sensitive data and enhancing privacy protection, and provide specific code examples. Use HTTPS protocol to transmit data The HTTPS protocol encrypts communication through SSL/TLS, which can protect the security of data during transmission. When handling sensitive data, it is important to
2023-10-10
comment 0
882

How to encrypt sensitive data using PHP
Article Introduction:With the advent of the Internet age, privacy security issues have become increasingly important. Confidentiality of sensitive data is an important aspect of protecting personal privacy. PHP is a widely used server-side scripting language that can encrypt sensitive data using various algorithms. This article will explain how to use PHP to encrypt sensitive data. 1. What is Encryption? Encryption refers to using a certain algorithm to convert plain text into an incomprehensible cipher text that looks like gibberish, thereby protecting its confidentiality. Only someone with the decryption key can restore it to readable plaintext, guaranteeing confidentiality and
2023-06-24
comment 0
482