Found a total of 6071 related content

How to set Windows security policy?
Article Introduction:To set a security policy in Windows, you need to follow the following steps: Open the "Security Policy Snap-in"; select the policy category to be managed (for example, local policy, account policy); browse the policy list, double-click the policy to be modified; adjust as needed settings; click OK to save changes. How to set Windows security policy Step 1: Open the security policy snap-in, press Win+R, enter "secpol.msc", and then press Enter. Step 2: Select a policy category In the left pane, expand Security Settings and select the policy category you want to manage, for example: Local Policy Account Policy Restricted Group Policy Step 3: Browse and modify the policy In the right pane, Browse the list of strategies. Double-click the policy you want to modify, and then root
2024-04-01
comment 0
540
How to open local security policy
Article Introduction:How to open the local security policy: 1. Click Start, find and open the Control Panel; 2. Change the view mode to large icons, find and enter the management tools option; 3. Double-click the local security policy option.
2020-12-30
comment 0
9966
C++技术中的安全编程:如何采用基于 CLIST 的安全策略?
Article Introduction:安全编程采用CLIST策略:CLIST是一组用于实施安全策略的类和接口,用于.NET和C++应用程序,可防止缓冲区溢出和SQL注入等安全漏洞。使用CLIST,开发人员可定义安全策略(例如访问控制列表),并使用SecurityTransparent特性应用于代码块,指示CLR透明地应用该策略。通过安全策略限制对数组索引的访问,防止超出数组界限导致的缓冲区溢出。
2024-05-18
comment 0
328

Linux Server Security: Strategies for Optimizing Web Interface Protection Strategies.
Article Introduction:Linux Server Security: Strategies for Optimizing Web Interface Protection Strategies With the rapid development of the Internet, more and more businesses are turning online, and the security of Web interfaces has become a focus that cannot be ignored in server operation and maintenance. On a Linux server, we can adopt a series of strategies to protect our Web interface and ensure the security of the server. This article will discuss optimization measures for Web interface protection strategies and give corresponding code examples. Firewall Settings Configuring the firewall is to protect the web interface security
2023-09-08
comment 0
687

Network security strategy models and applications
Article Introduction:As an important part of information security, network security has become a major problem in the development of the current world Internet. In this context, network security strategies have become the foundation and key to achieving network security. This article will discuss the patterns and applications of network security strategies. 1. Network security policy model 1.1 "Blacklist" mechanism The "blacklist" mechanism is to define a list of people who are not allowed to access in the system, and use firewalls or other network security devices to control network resources. When an IP address in the blacklist appears Immediately block access requests
2023-06-11
comment 0
1398

MySQL and PostgreSQL: Data Security and Backup Strategies
Article Introduction:MySQL and PostgreSQL: Data Security and Backup Strategies Introduction: In modern society, data has become an indispensable part of business and personal life. For database management systems, data security and backup strategies are crucial, both to protect data from loss or damage and to ensure the reliability and integrity of recovered data. This article will focus on the data security and backup strategies of two mainstream relational database systems, MySQL and PostgreSQL. 1. Data security: (1) User rights
2023-07-13
comment 0
660

How to configure network security policy on Linux
Article Introduction:How to configure network security policy on Linux Introduction: With the rapid development of the network, network security issues have become more and more prominent. In Linux systems, through appropriate network security policy configuration, the system can be effectively protected from network attacks. This article will introduce how to configure network security policies on the Linux operating system and provide corresponding code examples. 1. Install a firewall A firewall is an important part of protecting network security. On Linux systems, you can use iptables or nftables to achieve
2023-07-07
comment 0
1463
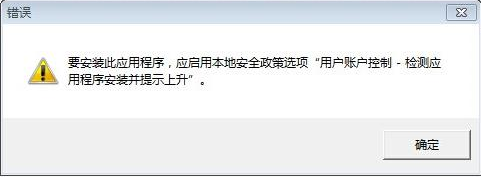
Is there a security policy issue when installing the touchpad driver in Windows 10?
Article Introduction:What should I do if the touchpad driver prompts for security policy issues? Laptops generally have touchpad drivers that allow users to set multiple parameters of the touchpad, including whether the touch command is with one finger or two fingers. Recently, some users want to install a new driver, but the following problems occur. This tutorial Let’s introduce the solution to you. "Security policy problem" encountered when installing the touchpad driver: Solution 1. Press the Win+R keys to open the run window, enter the secpol.msc command and press Enter to open the local security policy interface (as shown below). 2. Click the expanded "Local Policy" and select "Security Options" (as shown below). 3. in&ldqu
2024-02-13
comment 0
615
How to develop an effective computer security strategy?
Article Introduction:How to set computer security policy? First, use the Windows key + R to quickly open the computer running interface. 2. Enter the "secpol.msc" command during operation. 3. Log in to the local security policy interface. 4. Find the local policy. 5. Find the security options under the local policy. 6. Here we mainly talk about is part of the security options ------ Regarding the account setting method, 7 administrator status account can be selected to be turned on, 8 if you want to set "local accounts with empty passwords are only allowed to log in to the console", you can Disable it. You can also directly rename the guest account name in 9. How to lower the security level of win11? The method to lower the security level of win11 is as follows: 1. Click "Control Panel" at the beginning of the lower left corner of the computer and click Enter
2024-01-16
comment
513

Security configuration management and access control policies in Java
Article Introduction:Security Configuration Management and Access Control Policies in Java Security is a crucial aspect in Java application development. To protect applications from potential attacks, we need to implement a series of security configuration management and access control policies. This article will explore security configuration management and access control strategies in Java and provide some relevant code examples. Security configuration management Security configuration management refers to setting and managing various security mechanisms and policies in Java applications to ensure the security of the application. Java mention
2023-08-07
comment 0
1055

Nginx URL security policy writing guide
Article Introduction:As a high-performance web server and reverse proxy server, Nginx is widely favored by website architects. But when using Nginx, we also need to pay attention to security issues, especially when processing URLs. Due to the flexibility of Nginx, if we do not adopt some URL security policies, we may be subject to the following attacks: SQL injection XSS attack illegal file download CSRF attack illegal request access, etc. This article will introduce the guide for writing Nginx URL security policies. 1. The precondition is writing N
2023-06-10
comment 0
665

What to do if win10 local security policy is gone
Article Introduction:Solution to the problem that win10 local security policy is gone: 1. We can right-click the start button in the lower left corner of the desktop and click the "Run" menu item in the pop-up menu; 2. Enter the command secpol.msc in the open run window, and then Click the OK button to quickly open the local security policy window.
2020-03-04
comment 0
10925

How to set a strong password policy on Linux
Article Introduction:How to set up a strong password policy on Linux Introduction: In the information age, protecting the sensitive information of individuals and enterprises is crucial. Passwords are one of the most commonly used authentication methods. In Linux systems, we can increase the security of account passwords by setting strong password policies to protect the security of our computers and data. This article will introduce how to set a strong password policy on Linux, and attach relevant code examples. Modify the password policy file First, we need to edit the password policy file/
2023-07-05
comment 0
3070

Nginx security management strategy [Practical]
Article Introduction:As an efficient web server and reverse proxy server, Nginx is widely used in modern Internet applications. However, as the number of people using Nginx continues to increase, Nginx security management becomes increasingly important. In Nginx's security management strategy, details matter. This article will introduce Nginx’s security management strategy [Practical] to help you better protect your Nginx server. Preventing DDoS attacks Nginx can effectively prevent DDoS attacks, but to achieve the best effect, it needs to be configured
2023-06-10
comment 0
979
PHP Forms Security Strategy: Use the OWASP Top 10 Security Recommendations
Article Introduction:With the high diffusion and widespread use of modern applications, security issues have become a hot topic. Cybercrime and hacking are becoming increasingly common, and many websites have become targets, especially those involving user authentication or sensitive data storage. To resist these attacks, websites should adopt a series of security measures, including forms security policies. In this article, we will cover PHP forms security strategies, specifically using the OWASP Top 10 security recommendations to protect your website and applications. this
2023-06-24
comment 0
587
What are the security optimization strategies for PHP websites?
Article Introduction:What are the security optimization strategies for PHP websites? With the rapid development of the Internet, more and more websites use PHP as the development language. This choice makes PHP very popular around the world. However, while PHP is a powerful and easy-to-learn language, it also faces some security risks. In order to protect their websites and users' information, website developers need to adopt a series of security optimization strategies. This article will introduce some common PHP website security optimization strategies and provide relevant code examples.
2023-08-25
comment 0
332

Firewall and Security Policy Implementation Guide in PHP
Article Introduction:Firewall and Security Policy Implementation Guide in PHP With the popularity of the Internet and the continuous expansion of application fields, network security issues have become increasingly prominent. As a widely used programming language, the security of PHP has also attracted much attention. To protect the security of our websites and applications, we need to implement some firewall and security policies. This article will introduce you to the firewall and security policy implementation guide in PHP and provide code samples for your reference. 1. Firewall Implementation Guide Data Filtering Before receiving user input, the data must be filtered to ensure that only
2023-07-05
comment 0
1115

How to configure Cookie security policy in Nginx
Article Introduction:With the continuous development and popularization of the Internet, Web applications have become an indispensable part of people's daily lives, which also determines that the security issues of Web applications are very important. In web applications, cookies are widely used to implement functions such as user identity authentication. However, cookies also present security risks. Therefore, when configuring Nginx, you must set appropriate cookie security policies to ensure the security of cookies. The following are some configuration cookie security policies in Nginx
2023-06-10
comment 0
3221

PHP and SOAP: How to deal with cross-domain access and security policies
Article Introduction:PHP and SOAP: How to handle cross-domain access and security policies Summary: Cross-domain access and security policies are common issues in web development. When using PHP and SOAP for server-side development, we often need to solve these problems. This article will introduce how to handle cross-domain access and security policies, and provide corresponding code examples to help readers better understand. Introduction: With the continuous development of the Internet, cross-domain access and security policies have become a major challenge in network development. When we use PHP and SOAP for server-side development, we need
2023-07-28
comment 0
497

How to use Nginx to configure the same origin policy to protect front-end security
Article Introduction:As the complexity of front-end applications continues to increase, web application security issues are becoming more and more important. The same-origin policy is an important security measure to avoid security issues such as cross-site scripting attacks. Nginx is a powerful web server software. This article will introduce how to use Nginx to configure the same-origin policy to protect front-end security. 1. Same-origin policy The same-origin policy is a security principle in web development that is used to restrict how documents or scripts under one domain name interact with resources under another domain name. Same origin refers to the protocol, domain name and terminal
2023-06-10
comment 0
1766