
| Introduction | Samba has long been the standard for providing shared file and print services to Windows clients on Linux systems. Used by home users, mid-sized businesses and large companies, it stands out as the best solution in environments where multiple operating systems coexist, something that most Samba installations face due to the widespread use of tools. The risk of an attack that exploits a known vulnerability that was considered unimportant until news of the WannaCry ransomware attack came out. |
Outdated and unpatched systems are vulnerable to remote code execution vulnerabilities. In simple terms, this means that someone with access to a writable share can upload an arbitrary piece of code and have it executed using root privileges in the server.
This issue is described as CVE-2017-7494 on the Samba website and is known to affect Samba v3.5 (released in early March 2010) and later. It was unofficially named SambaCry due to similarities to WannaCry: they both target the SMB protocol and are likely worms - which could cause it to spread from one system to another.
Debian, Ubuntu, CentOS and Red Hat have taken quick action to protect their users and released patches for their supported versions. Additionally, unsupported security workarounds are provided.
Update SambaAs mentioned previously, there are two ways to update depending on how you installed it previously:
Let’s look at what you need to do in this situation:
Fixing SambaCry under Debian
Add the following line to your sources list (/etc/apt/sources.list) to ensure that apt gets the latest security updates:
deb http://security.debian.org stable/updates main deb-src http://security.debian.org/ stable/updates main
Next, update the available packages:
# aptitude update
Finally, make sure that the version of the samba package matches the bug-fixed version (see CVE-2017-7494):
# aptitude show samba
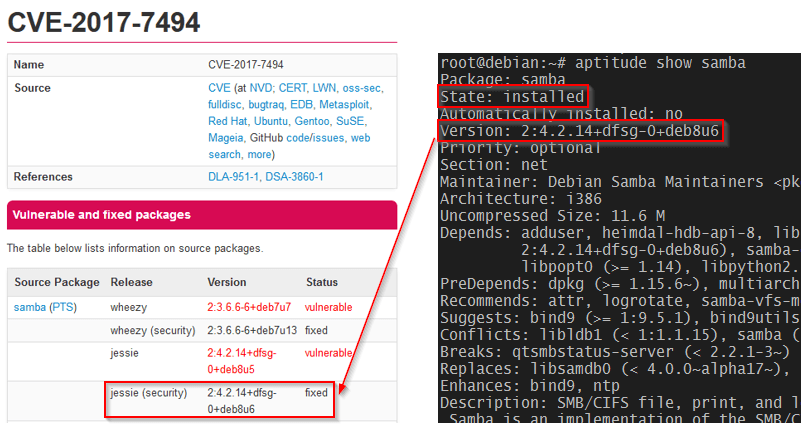
Fixing SambaCry in Debian
Fixing SambaCry in Ubuntu
To start the repair, check for new available packages and update the Samba package as follows:
$ sudo apt-get update $ sudo apt-get install samba
The Samba versions that have fixed CVE-2017-7494 are as follows:
Finally, run the following command to verify that your Ubuntu has the correct version installed.
$ sudo apt-cache show samba
Fixing SambaCry in CentOS/RHEL 7
The patched Samba version in EL 7 is samba-4.4.4-14.el7_3. To install it, do these:
# yum makecache fast # yum update samba
As before, make sure you have the patched version of Samba installed:
# yum info samba
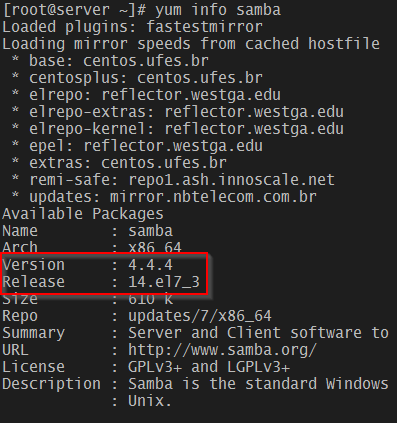
Fixing SambaCry in CentOS
Old supported CentOS and older versions of RHEL are also fixed. See RHSA-2017-1270 for more.
Note: The following procedure assumes you have previously built Samba from source. It is strongly recommended that you try it in a test environment before deploying to a production server.
Also, make sure you back up the smb.conf file before starting.
In this case, we will also compile and update Samba from source. However, before we begin, we must first ensure that all dependencies are installed. Note that this may take several minutes.
In Debian and Ubuntu:
# aptitude install acl attr autoconf bison build-essential / debhelper dnsutils docbook-xml docbook-xsl flex gdb krb5-user / libacl1-dev libaio-dev libattr1-dev libblkid-dev libbsd-dev / libcap-dev libcups2-dev libgnutls28-dev libjson-perl / libldap2-dev libncurses5-dev libpam0g-dev libparse-yapp-perl / libpopt-dev libreadline-dev perl perl-modules pkg-config / python-all-dev python-dev python-dnspython python-crypto xsltproc / zlib1g-dev libsystemd-dev libgpgme11-dev python-gpgme python-m2crypto
In CentOS 7 or similar:
# yum install attr bind-utils docbook-style-xsl gcc gdb krb5-workstation / libsemanage-python libxslt perl perl-ExtUtils-MakeMaker / perl-Parse-Yapp perl-Test-Base pkgconfig policycoreutils-python / python-crypto gnutls-devel libattr-devel keyutils-libs-devel / libacl-devel libaio-devel libblkid-devel libxml2-devel openldap-devel / pam-devel popt-devel python-devel readline-devel zlib-devel
Stop the service (LCTT translation: not necessary here):
# systemctl stop smbd
Download and unzip the source code (4.6.4 is the latest version at the time of writing):
# wget https://www.samba.org/samba/ftp/samba-latest.tar.gz # tar xzf samba-latest.tar.gz # cd samba-4.6.4
For informational purposes, check the available configuration options with the following command.
# ./configure --help
If you have used some options in the previous version of the build, you may be able to include some options in the return of the above command, or you may choose to use the default value:
# ./configure # make # make install
Finally restart the service.
# systemctl restart smbd
And verify you are using the updated version:
# smbstatus --version
The returned value here should be 4.6.4.
Other situationsIf you are using an unsupported distribution and for some reason cannot upgrade to the latest version, you may want to consider these suggestions:
There are also generals:
nt pipe support = no
Add to the [global] field of smb.conf. You might want to keep in mind that this "may disable certain features of the Windows client" according to the Samba Project.
Important: Note that the nt pipe support = no option disables the share list for Windows clients. For example: when you enter //10.100.10.2/ in Windows Explorer on a Samba server, you will see "permission denied". Windows clients have to manually execute the share, such as //10.100.10.2/share_name to access the share.
SummarizeIn this post, we have described the SambaCry vulnerability and how to mitigate the impact. We hope you can use this information to protect the systems you are responsible for.
If you have any questions or comments about this article, please use the comment box below to let us know.
About the Author:
Gabriel Cánepa is a GNU/Linux system administrator and web developer at Villa Mercedes in San Luis, Argentina. He works for a large international consumer products company and has great fun using FOSS tools in his daily work to increase productivity.
The above is the detailed content of Application of methods to repair SambaCry vulnerabilities in Linux systems. For more information, please follow other related articles on the PHP Chinese website!




