
Hello everyone, I am Lao Tian who specializes in sharing useful information with you. In addition, friends who need interview materials, remember to reply backstageInterview
But you may not be able to answer the following three soul torture questions:
But in fact, HTTPS uses symmetric encryption to encrypt content transmission, and asymmetric encryption only works in the certificate verification phase.
The overall process of HTTPS is divided into certificate verification and data transmission stages. The specific interaction process is as follows:
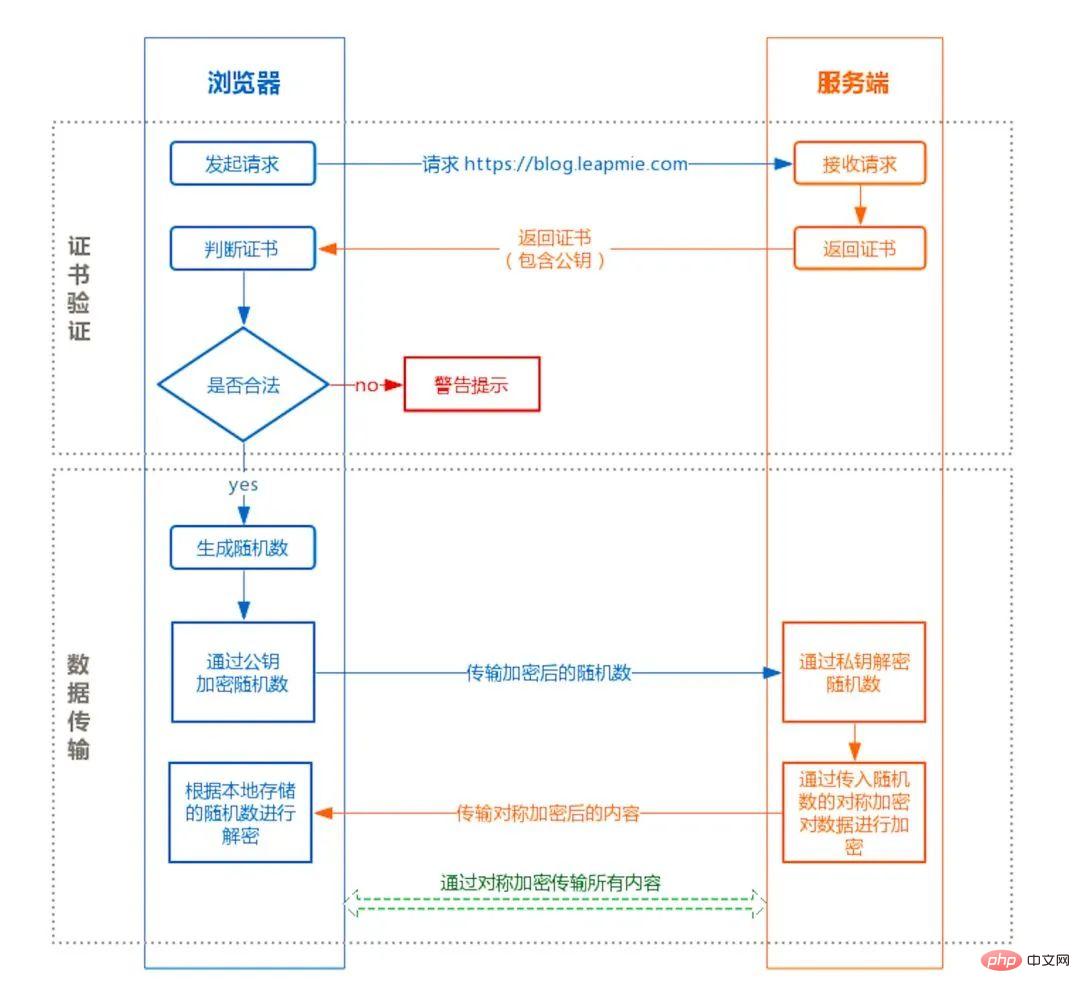
Certificate verification stage :
Data transmission phase:
First of all, the encryption and decryption efficiency of asymmetric encryption is very low, and in HTTP application scenarios, there is usually a lot of interaction between ends, and asymmetric encryption The efficiency is unacceptable.
In addition, in the HTTPS scenario, only the server saves the private key, and a pair of public and private keys can only achieve one-way encryption and decryption. Therefore, the content transmission encryption in HTTPS adopts symmetric encryption instead of asymmetric encryption. encryption.
The HTTP protocol is considered unsafe because the transmission process can easily be hooked by listeners to monitor and forge servers, while the HTTPS protocol mainly solves the security problem of network transmission. .
First of all, we assume that there is no certification authority and anyone can create a certificate. The security risk this brings is the classic "man-in-the-middle attack" problem.
The specific process of "man-in-the-middle attack" is as follows:
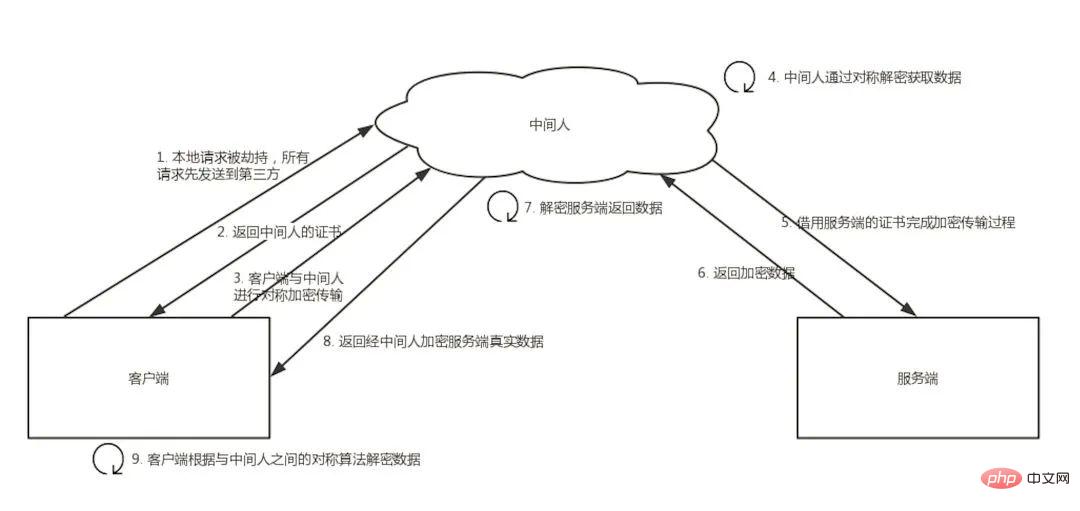

The browser will consider the certificate to be legitimate only if any of the above steps are met.
**Insert a question here that I have thought about for a long time but the answer is actually very simple: **Since the certificate is public, if I want to launch a man-in-the-middle attack, I download a certificate from the official website as my server certificate, then the client will definitely agree that this certificate is legitimate. How to avoid this kind of certificate fraud?
In fact, this is the use of public and private keys in non-encrypted symmetry. Although the middleman can obtain the certificate, the private key cannot be obtained.
It is impossible to deduce the corresponding private key from a public key. Even if the middleman obtains the certificate, it cannot pretend to be a legitimate server because it cannot decrypt the encrypted data passed in by the client.
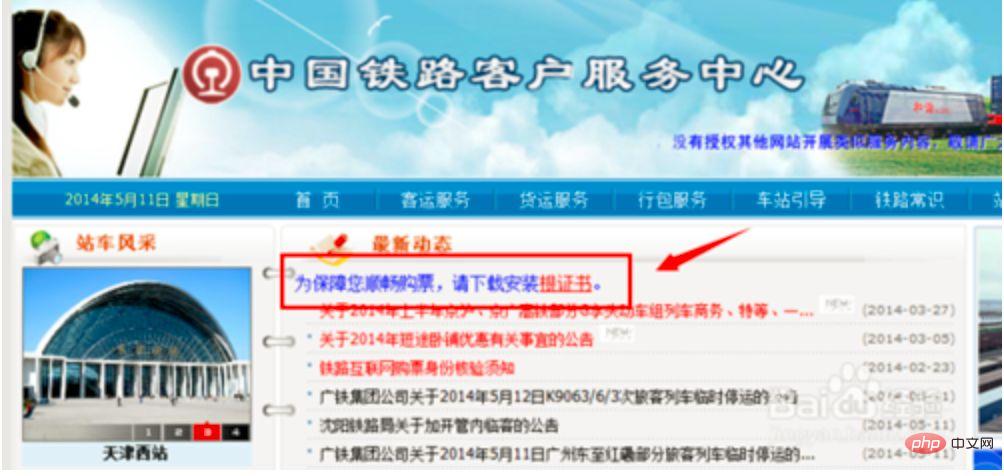
If you need the browser not to prompt for security risks, you can only use certificates issued by certification authorities.
But browsers usually only prompt for security risks and do not restrict the website from being accessible, so technically anyone can generate a certificate, and as long as there is a certificate, the HTTPS transmission of the website can be completed.
For example, the early 12306 used manual installation of private certificates to achieve HTTPS access.
Certificate verification is implemented using asymmetric encryption, but the transmission process uses symmetric encryption, and the important random numbers in the symmetric encryption algorithm are locally generated and stored locally Yes, how does HTTPS ensure that the random number will not be stolen?
In fact, HTTPS does not include security guarantees for random numbers. HTTPS only guarantees the security of the transmission process, and the random numbers are stored locally. Local security belongs to another security category. The countermeasures include installing anti-virus software, Anti-Trojan horses, browser upgrades to fix vulnerabilities, etc.
HTTPS data is encrypted. Under normal circumstances, the packet content captured by the packet capture tool after proxy request is encrypted and cannot be viewed directly.
However, as mentioned above, the browser will only prompt the security risk. If the user authorizes it, he can still continue to access the website and complete the request.
Therefore, as long as the client is our own terminal and we authorize it, we can set up a middleman network, and the packet capture tool serves as the agent of the middleman.
Usually, the HTTPS packet capture tool is used to generate a certificate. The user needs to manually install the certificate into the client, and then all requests initiated by the terminal complete the interaction with the packet capture tool through this certificate.
Then the packet capture tool forwards the request to the server, and finally outputs the result returned by the server to the console and then returns it to the terminal, thereby completing the closed loop of the entire request.
Since HTTPS cannot prevent packet capture, what is the point of HTTPS? HTTPS can prevent users from being monitored on communication links without their knowledge. It does not provide protection for active credit-granting packet capture operations because users in this scenario are already aware of the risks.
To prevent packet capture, application-level security protection needs to be adopted, such as private symmetric encryption, and anti-decompilation reinforcement on the mobile terminal to prevent local algorithms from being cracked.
Q: Why is HTTPS safe?
A: Because HTTPS ensures transmission security, prevents the transmission process from being monitored, prevents data from being stolen, and can confirm the authenticity of the website.Q: What is the transmission process of HTTPS?
A: The client initiates an HTTPS request, the server returns a certificate, the client verifies the certificate, and after passing the verification, it locally generates a random number used to modify the symmetric encryption algorithm. The random number is encrypted and transmitted to the server through the public key in the certificate. After receiving it, the server decrypts the random number through the private key. Subsequent data interactions are encrypted and decrypted through the symmetric encryption algorithm.Q: Why do I need a certificate?
A: Prevent "man-in-the-middle" attacks and provide identity proof for the website.Q: Will packets be captured when using HTTPS?
A: Packets will be captured. HTTPS only prevents users from being monitored without their knowledge. If the user actively grants credit, a "middleman" network can be built, and the proxy software can monitor the transmitted content. Decrypt. I would like to share a process diagram of learning HTTPS: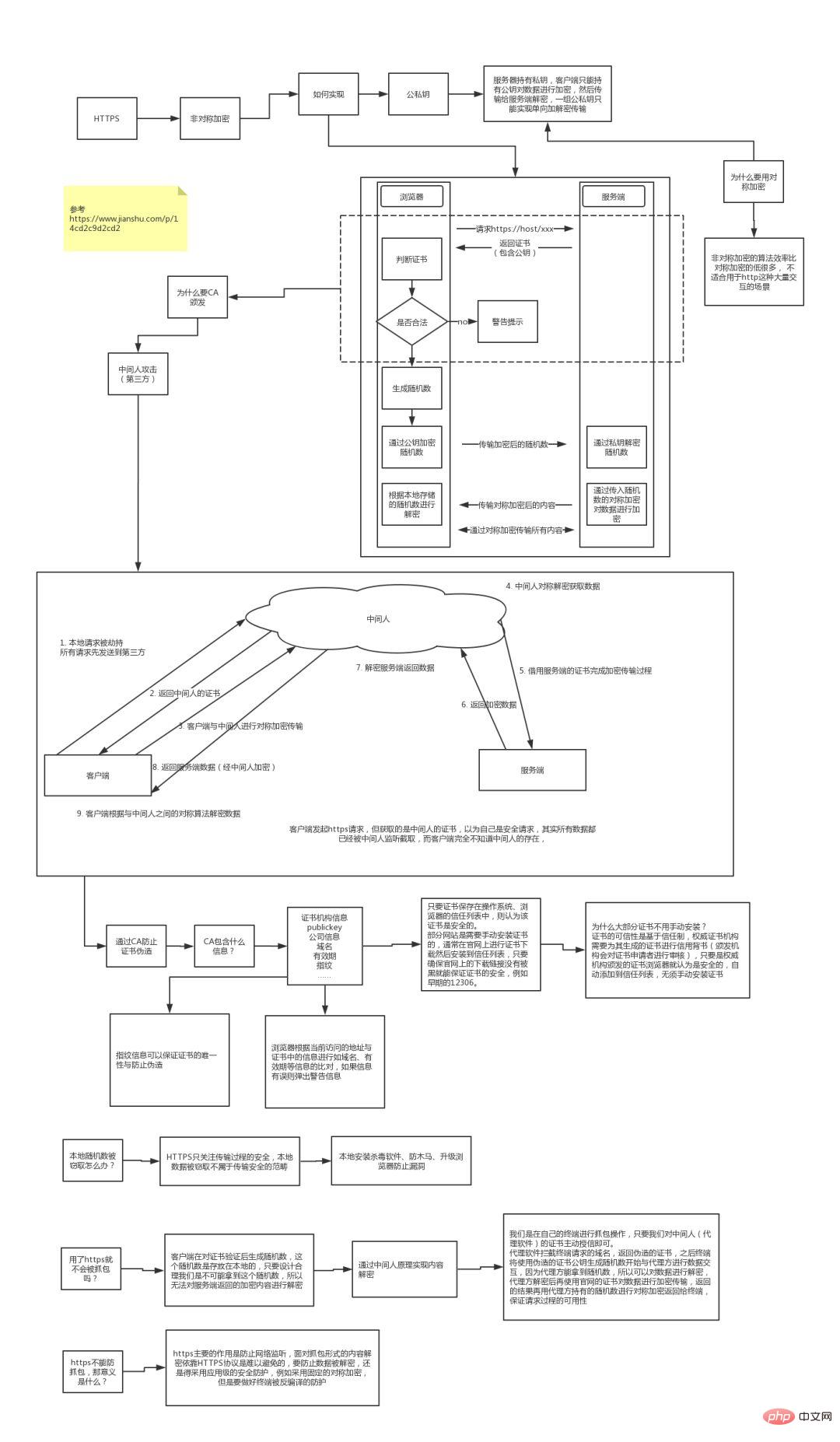
The above is the detailed content of Interview with a big factory: HTTPS was asked three times in a row, and the last question was whether there are many people. For more information, please follow other related articles on the PHP Chinese website!
 How to open html files on mobile phone
How to open html files on mobile phone File type introduction
File type introduction The difference between currentregion and usedrange
The difference between currentregion and usedrange Computer prompts that msvcr110.dll is missing and how to solve it
Computer prompts that msvcr110.dll is missing and how to solve it ps curve shortcut key
ps curve shortcut key How to use imfinfo function
How to use imfinfo function How to clean up your computer's C drive when it's full
How to clean up your computer's C drive when it's full How to solve the problem that Win10 folder cannot be deleted
How to solve the problem that Win10 folder cannot be deleted



