
This article mainly introduces intermediate and advanced PHP interview questions, which has certain reference value. Now I share it with everyone. Friends in need can refer to it
Related recommendations: "2019 PHP Summary of interview questions (collection) 》
1. Give you four coordinate points and judge whether they can form a rectangle, such as judging ([0,0],[0,1],[ 1,1],[1,0]) can form a rectangle.
2. Write a piece of code to determine whether a ring is formed in the one-way linked list. If a ring is formed, please find the entrance of the ring, which is point P
3. Write a function to obtain a All pictures in the article content and download
4. Obtain the IP address of the current client and determine whether it is (111.111.111.111,222.222.222.222)
5. nginx’s log_format configuration As follows:
log_format main 'remoteaddr−remote_user [timelocal]"request"'
'statusbody_bytes_sent "httpreferer"""http_user_agent" "upstreamresponsetime""request_time" "http_x_forwarded_for"';
From today's nginx log file In access.log:
a. List the 20 largest rows of "request_time"?
b. List the number of visits at 10 a.m. 20 url addresses to buy?
6. What is a CSRF attack? XSS attack? How to prevent it?
7. In applications, we often encounter user The table randomly retrieves 10 pieces of data to display the situation. Briefly describe how you implement this function.
8. Randomly draw 5 cards from the poker cards to determine whether they are a straight, that is, these 5 cards It is continuous
9. How to find the first common node of two intersecting one-way linked lists
10. The longest common subsequence problem LCS. If there are two arrays [1,2,5,11,32,15,77] and [99,32,15,5,1,77], find them To write code with optimal time complexity for numbers that we all have in common, array_intersect cannot be used (there are pitfalls here, and you need to study dynamic programming).
11. Linux memory allocation and multi-threading principles
12. The difference between primary key and unique index in MYSQL
13. The main difference between http and https
14. http status code and its meaning
15. How to check system resource usage in Linux
16. What is the principle of SQL injection? How to prevent SQL injection
17. isset(null) isset(false) empty(null) empty(false) output
18. Methods to optimize MYSQL
19. Database What is the transaction in?
20. Write a function to extract the file extension from a standard URL as efficiently as possible
21. The parameters are arrays of multiple dates and times, and return the one closest to the current time. time
22. The difference between echo, print, and print_r
23. What are the keys and their meanings in the header of the http protocol
24. Code for front, middle and back traversal of the binary tree
25. What are the structural differences between PHP arrays and C language arrays?
26. How to implement Redis's jump table
27. What is hash? How to store data after hash conflict?
28. Clustered index, what is the difference between clustered index?
29. How does B Tree search?
30. What is the difference between array and hash?
31. Write a function to determine whether the following expansion sign is closed. Left and right symmetry means closed: ((())),)(()),(()))), (((((((((()) ()), (()()), ()()
32. Find the unique values in the array [1,2,3,3,2,1,5]
What is your time complexity for questions 33 and 32? In some cases, you write an algorithm, and then the interviewer will ask you to write down the time complexity expression of your algorithm
34. How is this weak type variable implemented in PHP?
35. During HTTP communication, does the client or the server actively disconnect?
36. What are the ways to initiate http requests in PHP? What's the difference?
37. There is a binary tree. Write code to find the shortest path from the root node to the flag node and print it out. There are multiple flag nodes. For example, 6 and 14 in the tree below are flag nodes. Please write code to print the two paths 8, 3, 6 and 8, 10, 14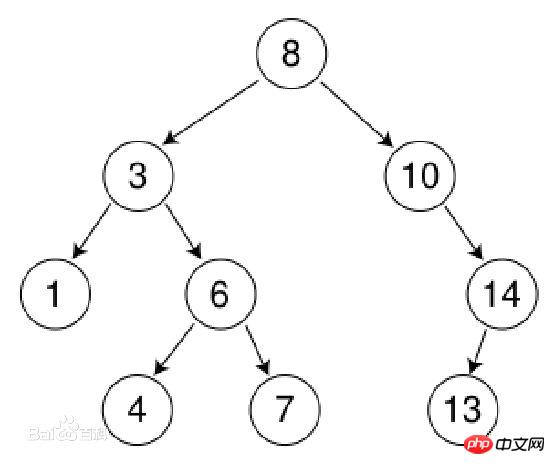
38. There are two files. The size of the files exceeds 1G. There is one data per line, and each line of data does not exceed 500 bytes. Some of the contents in the two files are exactly the same. Please write code to find the same lines and write them to the new file. The maximum allowed size of PHP is 255M.
39. Please write at least two PHP functions that support callback processing, and implement a PHP function that supports callback.
40. Please write at least two PHP functions that support callback processing.
40. Please write at least two PHP functions that support callback processing. How to download all files (code or ideas).
41. Please write down at least three methods or functions for intercepting file name suffixes (both PHP native functions and self-implemented functions are acceptable)
42. How does PHP implement cookies without its own The function issues cookies to the client. For distributed systems, how to save session values.
###43. Please use SHELL to count the most visited URL addresses in the nginx log within 5 minutes. What are the corresponding IPs? ###44. Write a shell script to back up the specified mysql library (such as test) to the specified folder and package it, delete the backup 30 days ago, then push the new backup to the remote server, and send an email notification after completion.
45. The difference between innodb and myisam engines in mysql database
46. From the time the user enters the URL in the browser and presses Enter, to seeing the complete meeting, what process does it go through? .
47. How to analyze the performance of a sql statement.
48. When pinging a server fails, which command should be used to trace routing packets?
linux:traceroute,windows:tracert
49、$a=[0,1,2,3]; $b=[1,2,3,4,5]; $a =$ b; What is var_dump($a) equal to?
50. $a=[1,2,3]; foreach($a as &$v){} foreach($a as $v){} var_dump($a) is equal to;
51. The user ID and many deduction rows are stored in the database. The user's wallet is stored in redis. Now we need to write a script to synchronize the deduction records in the database to redis. Execute once every 5 minutes. What issues should be considered?
52. MYSQL master and slave servers. If the master server is the innodb engine and the slave server is the myisam engine, what problems will be encountered in practical applications?
53. What are the process signals in Linux?
54, the underlying implementation of redis
55, asynchronous model
56, 10g file, use php to check its row number
57, there are 1 billion order data, belonging to 1000 drivers, please take out the order amount Top 20 drivers
58, design a WeChat red envelope function
59, count the qps of the last 5 seconds based on the access.log file, and display it in the following format, 01 1000 (the difficulty is 01 Serial number)
60. Why is the performance of php7 improved so much?
61. Traversing a multi-dimensional array
62. There is such a string abcdefgkbcdefab...random length , write a function to find the number of times bcde appears in this string
63. There is a file of 1G size. Each line in it is a word. The size of the word does not exceed 16 bytes. There is a memory limit. The size is 1M. Return the 100 most frequent words
65, PHP process model, how PHP supports multiple concurrency
66, nginx process model, how to support multiple concurrency
67, php-fpm configuration meaning, fpm's daemonize mode
static - the number of child processes is fixed (pm.max_children)
ondemand - the process is only generated when there is a demand (when requested, Contrary to dynamic, pm.start_servers is started when the service starts
dynamic - the number of child processes is set dynamically based on the following configuration: pm.max_children, pm.start_servers, pm.min_spare_servers, pm.max_spare_servers
68. Let you implement a simple architecture and maintain high availability. Two interfaces, one to upload a text and one to obtain the uploaded content. How do you design it? To avoid single computer room failures, and at the same time make the code level insensitive .
69. Two mysql servers, one of which is down, how to make the business end switch without any sense and ensure that the data of the podium server is consistent under normal circumstances
70.http protocol Specific definition
71. What is a lock and how to solve the lock problem
72. The difference between rand and mt_rand
73. How is mysql transaction isolation implemented
74. How to implement mysql lock
75. Symmetric encryption and asymmetric encryption methods
76. 10 bottles of water, one of which is poisonous. After drinking the poisonous water, there will be He died from the poison after 23 hours and 59 minutes. Please use the fewest mice to find this bottle of water within 24 hours.
Related recommendations:
Summary of PHP interview questions
The above is the detailed content of Intermediate and advanced php interview questions. For more information, please follow other related articles on the PHP Chinese website!




