
Course Advanced 11321
Course Introduction:Shell scripting skills will never go out of style: "Shangguan Shell Video Tutorial" lets you know that they can allow UNIX to fully realize its true potential. For uNIx users and system administrators, writing shell scripts is a must, which allows you to quickly control and customize the powerful functions of any UNIX system.

Course Advanced 10535
Course Introduction:The course content covers common PHP security vulnerabilities in web development, vulnerabilities in common PHP functions, and PHP file system security. At the same time, the security issues of server software are introduced.
Course Intermediate 3387
Course Introduction:A firewall is a system used to control access to a computer network. Firewalls can isolate risk areas from safe access areas and prevent unpredictable or unauthorized external access from invading the internal network. Learning firewalls under Linux is not only for these reasons. The most important thing is that during the learning stage, through the use of firewalls, you can better master the principles of network communication, become familiar with the operation of Linux, and master network services and network protocols. It is also important for learning Linux operation and maintenance or Cybersecurity is helpful. There are many firewalls under Linux, including iptables, firewalld, selinux, tcp_warppers, etc. This course summarizes these firewall-related technologies.
Distinguish between idle shell exchange window and text window
2018-09-10 14:42:39 0 1 1492
linux - How to save another configuration file in the shell.
2017-05-16 13:22:42 0 3 632
vim - Is there any better shell plug-in?
Is there a better shell plug-in for vim? For example, if and fi are paired
2017-05-27 17:44:18 0 1 774

Course Introduction:Security of Linux Shell Scripting: Avoiding Security Vulnerabilities Introduction: With the popularity and application of Linux operating system, Linux shell script programming has become a very important skill. However, due to the nature and usage of shell scripts, writing unsafe scripts may lead to security vulnerabilities. This article explores how to write secure shell scripts and uses code examples to illustrate how to avoid common security vulnerabilities. 1. Avoid using clear text passwords in shell scripts to avoid
2023-09-09 comment 0 1628
Course Introduction:PHP Security-Shell RFI Scanner。?php /*************************************************************************** * PHP Security-Shell RFI Scanner * * * * Copyright (C) 2007 by pentest * * * * http://security-she
2016-07-13 comment 0 848
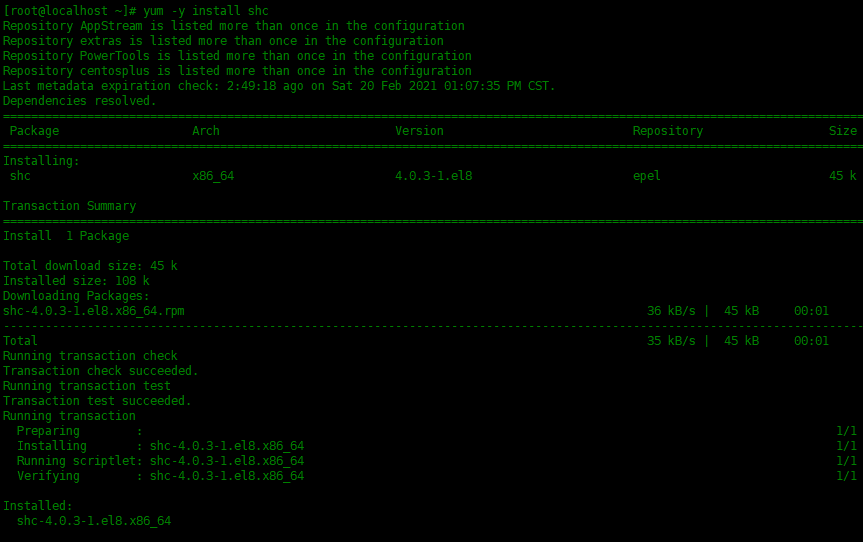
Course Introduction:It is very common to use scripts on Linux systems. However, due to the openness of script codes, scripts sometimes become maliciously modified, copied, and spread. To do this, we need a way to secure our script code. SHC is a very practical encryption tool that can help us encrypt Shell scripts and protect the security of the code. How to encrypt shell script in Linux environment? The shell script contains the password and you don't want someone else with execution permissions to view the shell script and get the password. You can install and use the shc tool. Ordinary users cannot read the encrypted shell script created by shc. SHC refers to: Shell Script Compiler (ShellScriptCompi
2024-02-11 comment 0 592

Course Introduction:The main differences between PHP functions and Shell functions are security (PHP functions are more secure), reliability (Shell functions vary by operating system), functionality (Shell functions are more powerful but limited by the shell), and performance (PHP functions are usually faster) and complexity (Shell functions are more complex). They are both used for file system, process and command operations, but PHP functions are built-in, while Shell functions are called through an external shell. Therefore, in server file download scenarios, the file_put_contents() function is safer, while the wget command is more flexible.
2024-04-24 comment 0 470