Found a total of 36 related content

Detection and repair of PHP SQL injection vulnerabilities
Article Introduction:Overview of detection and repair of PHP SQL injection vulnerabilities: SQL injection refers to an attack method in which attackers use web applications to maliciously inject SQL code into the input. PHP, as a scripting language widely used in web development, is widely used to develop dynamic websites and applications. However, due to the flexibility and ease of use of PHP, developers often ignore security, resulting in the existence of SQL injection vulnerabilities. This article will introduce how to detect and fix SQL injection vulnerabilities in PHP and provide relevant code examples. check
2023-08-08comment 0943
sql注入漏洞解决方法
Article Introduction:SQL注入漏洞通过恶意输入影响数据库安全,解决方法包括:参数化查询:用占位符替换硬编码值,防止注入。数据验证:确保恶意字符不会传入SQL语句。使用预编译语句:编译SQL语句,防止运行时修改。限制数据库权限:只授予必要的权限。使用Web应用程序防火墙 (WAF):检测和阻止恶意尝试。持续监控和更新:定期检查漏洞并应用补丁。使用安全开发实践:遵循安全编码指南,考虑安全问题。
2024-08-20comment984

PHP SQL injection vulnerabilities and prevention measures
Article Introduction:What is a PHPSQL injection vulnerability? In the development of many websites, using PHP and MySQL is the most common solution. Although PHP is very portable and easy to use, MySQL is also a completely free database. Their combination can generally quickly and easily develop websites full of various functions. However, it should be noted that there is a potential security risk when developing with PHP and MySQL, which is SQL injection vulnerability. SQL injection vulnerabilities occur when an attacker exploits the
2023-06-09comment 0845
sql注入漏洞怎样防止
Article Introduction:为了防止 SQL 注入漏洞,组织应采取以下步骤:使用参数化查询替换敏感数据。验证数据输入的格式和字符。限制用户输入的字符列表。转义特殊字符以避免被解释为 SQL 命令。使用预编译的存储过程来提高安全性。集成安全框架以保护应用程序。定期更新软件和数据库以修复漏洞。
2024-06-17comment175

sql注入漏洞怎么修
Article Introduction:可以通过以下方法修复 SQL 注入漏洞:1. 参数化查询;2. 输入验证和清理;3. 使用安全 API;4. 限制数据库权限;5. 保持软件更新;6. 使用 Web 应用程序防火墙 (WAF);7. 培训意识。
2024-05-30comment776

Parsing SQL blind injection principles through laravel vulnerability examples
Article Introduction:This article brings you relevant knowledge about laravel. It mainly introduces how to explain the principle of blind SQL injection by creating a laravel vulnerability. The so-called blind injection is an injection attack completed when the server has no error echo. The following Let's take a look, I hope it will be helpful to everyone.
2022-07-27comment 02091
sql注入漏洞解决方法 sql注入怎么解决
Article Introduction:解决SQL注入漏洞的方法包括:使用参数化查询防止代码注入。限制用户输入减少注入尝试成功率。使用白名单仅允许接受已知安全值的输入。使用黑名单阻止提交包含已知恶意模式的输入。对错误消息进行模糊处理减少攻击者获取系统信息的能力。强制执行最小权限原则限制用户访问敏感信息的能力。使用防火墙阻止未经授权的访问。定期更新软件和补丁解决已知漏洞。监视数据库活动检测和阻止注入尝试。
2024-08-20comment803
PHP 框架安全指南:如何避免 SQL 注入漏洞?
Article Introduction:PHP框架安全指南:避免SQL注入漏洞SQL注入是Web应用程序中最常见的安全漏洞之一,它允许攻击者执行恶意SQL查询并访问或修改数据库数据。在PHP框架中,采取措施保护应用程序免受这些攻击至关重要。了解SQL注入SQL注入发生在攻击者能够构建输入字符串并将其注入到SQL查询中时。这可能会导致以下安全问题:数据泄露:攻击者可以访问敏感的数据库数据,例如用户信息或财务信息。数据篡改:攻击者可以修改或删除数据库中的数据,从而破坏应用程序。拒绝服务:攻击者可以执行资源密集型的
2024-05-24comment 0947

Strategies to deal with SQL injection vulnerabilities in PHP
Article Introduction:SQL injection is a common network attack method that uses the application's imperfect processing of input data to successfully inject malicious SQL statements into the database. This attack method is particularly common in applications developed using the PHP language, because PHP's handling of user input is usually relatively weak. This article will introduce some strategies for dealing with SQL injection vulnerabilities and provide PHP code examples. Using prepared statements Prepared statements are a recommended way to defend against SQL injection. It uses binding parameters to combine input data with
2023-08-09comment 0720

Nginx security practice: preventing SQL injection and vulnerability attacks
Article Introduction:Nginx is a fast, efficient, and reliable web server. Its high scalability, flexibility, and security make it a popular choice in the Internet industry. However, whether for developers or operation and maintenance personnel, security issues are always an easily overlooked issue. This article will introduce how to improve the security of the Nginx server through some simple techniques and tools, mainly involving preventing SQL injection and vulnerability attacks. 1. Prevent SQL Injection SQL injection is a common behavior in web security attacks. Hackers can take advantage of this
2023-06-10comment 01729
SonarSource发现严重漏洞!Gentoo Linux遭遇SQL注入攻击风险
Article Introduction:1.SonarSource近日发现GentooLinux发行版存在CVE-2023-28424严重漏洞。该漏洞位于Soko搜索组件中,可被利用进行SQL注入攻击,CVSS风险评分为9.1。GentooLinux开发团队已在24小时内修复该漏洞。Soko组件是一个公共API,用于提高搜索效率和提供错误跟踪。漏洞成因是数据库组态配置不当,导致攻击者可绕过ORM进行SQL注入。GentooLinux是一种基于源代码的发行版,用户应及时更新系统以获取安全修复。SonarSource的发现凸显了网络安全的持续重要性
2024-07-15comment106
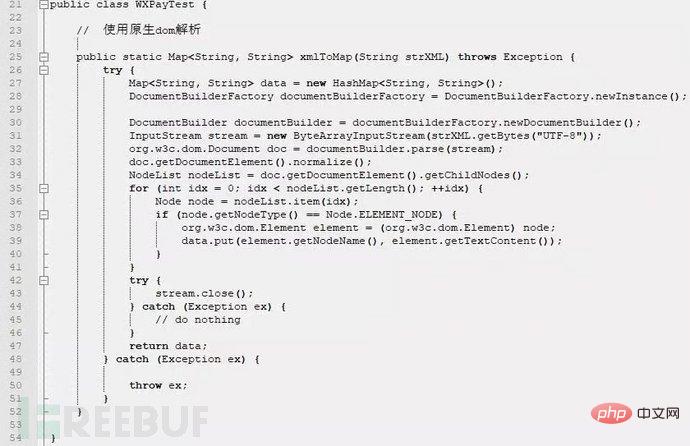
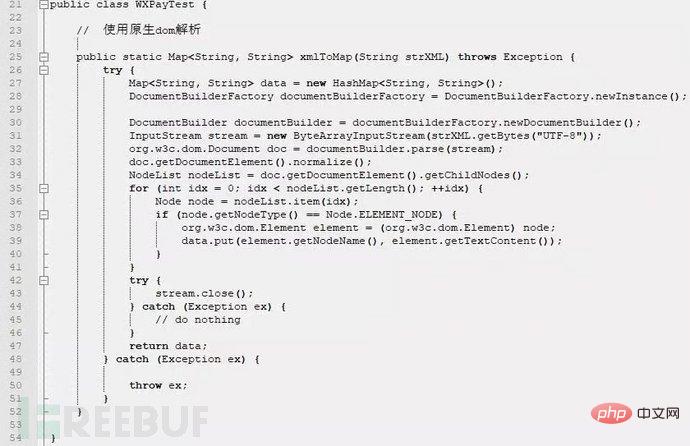
Example analysis of XML external entity injection vulnerability
Article Introduction:1. XML external entity injection XML external entity injection vulnerability is what we often call XXE vulnerability. XML is a widely used data transmission format, and many applications contain code for processing XML data. By default, many outdated or improperly configured XML processors will reference external entities. If an attacker can upload an XML document or add malicious content to the XML document, through vulnerable code, dependencies, or integrations, he or she can attack a flawed XML processor. The occurrence of XXE vulnerabilities has nothing to do with the development language. As long as the xml data is parsed in the application and the data is controlled by the user, the application may be vulnerable to XXE attacks. This article uses java
2023-05-11comment 01495

How to defend against PHP code injection vulnerabilities
Article Introduction:Introduction to defense methods for PHP code injection vulnerabilities: For PHP developers, they often encounter a vulnerability exploited by hackers, namely the PHP code injection (CodeInjection) vulnerability. In this vulnerability, hackers gain control of the server by injecting malicious code into user-entered data. In order to protect the security of our website and our users, we need to understand and implement some defense methods. This article will introduce you to some common defense methods for PHP code injection vulnerabilities and provide relevant code examples. Entered
2023-08-07comment 0796

PHP Secure Coding Practices: Preventing LDAP Injection Vulnerabilities
Article Introduction:PHP Secure Coding Practices: Prevent LDAP Injection Vulnerabilities Developing secure web applications is critical to protecting user data and system security. When writing PHP code, preventing injection attacks is a particularly important task. This article will focus on how to prevent LDAP injection vulnerabilities and introduce some best practices for secure coding in PHP. Understanding LDAP Injection Vulnerabilities LDAP (Lightweight Directory Access Protocol) is a protocol for accessing and managing information in distributed directory services. LDAP injection vulnerability is a security threat that attacks
2023-07-01comment 0337
Getting Started with PHP: Code Injection Vulnerabilities
Article Introduction:In recent years, network security issues have attracted more and more frequent attention. Among them, code injection vulnerabilities are one of the common security issues. PHP, as a commonly used back-end programming language, is widely used in website development. However, due to its flexibility and ease of use, PHP will have security vulnerabilities in the process of writing code. So, how to avoid code injection vulnerabilities? This article will introduce you to code injection vulnerabilities in PHP Getting Started Guide. 1. Definition of code injection vulnerability Code injection vulnerability, as the name suggests, means that hackers inject code into the program
2023-05-20comment 0616
PHP security protection: Prevent code injection vulnerabilities
Article Introduction:With the advent of the Internet era, PHP, as an open source scripting language, is widely used in Web development, especially playing an important role in the development of dynamic websites. However, security issues have also become an issue that cannot be ignored in the development of PHP. Among them, code injection vulnerabilities have always been one of the hot topics in the field of web security because of their difficulty to prevent and fatal harm. This article will introduce the principles, hazards and prevention methods of code injection vulnerabilities in PHP. 1. The principles and hazards of code injection vulnerabilities Code injection vulnerabilities are also called SQL
2023-06-24comment 01009

How to protect against LDAP injection vulnerabilities using PHP
Article Introduction:As network security issues receive more and more attention, more and more programmers are beginning to pay attention and learn how to prevent code from being attacked. Among them, common attack methods include SQL injection, XSS, CSRF, etc. However, there is another common attack method that is underestimated: LDAP injection vulnerabilities. This article will introduce the principle of this attack method and how to use PHP to prevent LDAP injection vulnerabilities. LDAP introduction LDAP (LightweightDirectoryAccessProtocol)
2023-06-24comment 0959

Let's talk about the sql injection vulnerability in thinkPHP3.2.3
Article Introduction:This article brings you relevant knowledge about thinkphp, which mainly introduces the related issues of thinkPHP3.2.3sql injection vulnerability, which also includes m method, d method, u method and other related contents. I hope it will be helpful to everyone.
2022-04-11comment 05533

Struts2 vulnerability S2-001 example analysis
Article Introduction:Vulhub vulnerability series: struts2 vulnerability S2-0011. Vulnerability description: struts2 vulnerability S2-001 is when the user submits form data and verification fails, the server uses OGNL expression to parse the parameter value previously submitted by the user, %{value} and refills the corresponding form data. For example, in a registration or login page. If the submission fails, the server will usually default to returning the previously submitted data. Since the server uses %{value} to perform OGNL expression parsing on the submitted data, the server can directly send the payload to execute the command. 2. Vulhub vulnerability exploitation: Using vulhub to reproduce vulnerabilities can save the environment construction process, which is very convenient. vu
2023-05-15comment 0906

Fixes for PHP remote execution and command injection vulnerabilities
Article Introduction:Title: Fix for PHP Remote Execution and Command Injection Vulnerabilities Introduction: In web development, PHP is a widely used back-end programming language. However, due to the characteristics of PHP and incorrect code writing, it is easy to cause some security vulnerabilities, such as remote execution vulnerabilities and command injection vulnerabilities. This article explains how these two vulnerabilities work and provides code examples to fix them. 1. Principle of Remote Execution Vulnerability Remote execution vulnerability means that the attacker causes the server to perform unexpected operations by sending malicious code. When developers use unsafe functions
2023-08-14comment 0816