Found a total of 110 related content
How to prevent PHP encryption algorithm from being cracked?
Article Introduction:How to prevent PHP encryption algorithm from being cracked? With the rapid development of the Internet, encryption algorithms play a vital role in the field of network security. As a widely used programming language, PHP also provides a rich library of encryption algorithm functions to protect users' sensitive data. However, due to the continuous advancement of hacking technology and computing power, simple encryption algorithms are easily cracked. This article will introduce several methods to prevent the PHP encryption algorithm from being cracked and provide corresponding code examples. PHP provides a variety of encryption using strong encryption algorithms
2023-08-19
comment 0
1095
Encryption and decryption in PHP: md5, SHA1, AES and other algorithms
Article Introduction:As a widely used programming language, PHP plays an important role in web development. In web development, security is a crucial issue, involving the transmission and storage of sensitive information such as user passwords and user input. In order to ensure the security of user information, developers usually use various encryption algorithms to encrypt this sensitive information. In PHP, commonly used encryption algorithms include MD5, SHA1, AES, etc. This article will introduce in detail the characteristics, usage and application scenarios of these encryption algorithms. 1. M
2023-05-11
comment 0
1663
Comparison and selection of PHP encryption algorithm and hash algorithm
Article Introduction:Overview of comparison and selection of PHP encryption algorithms and hash algorithms When protecting data, PHP provides many encryption algorithms and hash algorithms to ensure data security. This article will compare several common encryption algorithms and hashing algorithms, and discuss how to choose and use them in actual projects. 1. Encryption Algorithm Symmetric encryption algorithm Symmetric encryption algorithm uses the same key for encryption and decryption. In PHP, the most commonly used symmetric encryption algorithm is AES (Advanced Encryption Standard).
2023-08-17
comment 0
493

How to protect user passwords using PHP encryption algorithm
Article Introduction:How to use PHP encryption algorithm to protect user passwords Introduction: In modern Internet application development, the security of user passwords is crucial. In order to prevent user passwords from being leaked, developers need to encrypt and store passwords to protect the security of user accounts. The PHP language provides a variety of encryption algorithms. This article will introduce how to use PHP encryption algorithms to protect user passwords. Selection of encryption algorithms PHP provides a variety of encryption algorithms, the most commonly used of which are hash functions and symmetric encryption algorithms. A hash function is a one-way encryption algorithm that
2023-07-08
comment 0
947
What are the PHP encryption algorithms that cannot be cracked?
Article Introduction:As a widely used server-side language, PHP encryption is an important method to protect website security. The security of the encryption algorithm directly affects the website's resistance to hacker attacks, so the selection and use of the encryption algorithm is particularly important. This article mainly introduces the PHP encryption algorithm that cannot be cracked. 1. Symmetric encryption algorithm Symmetric encryption algorithm is an algorithm that uses the same key for encryption and decryption. It is widely used in data transmission, data storage and file protection. Symmetric encryption algorithms supported by PHP include DES, AES, Blowfish, etc., among which the most popular
2023-04-10
comment 0
607
PHP data filtering: using secure encryption algorithms
Article Introduction:PHP data filtering: Use secure encryption algorithms As network security issues become increasingly serious, protecting the security of user data has become one of the primary concerns of developers. When developing web applications, we often need to filter and encrypt user-entered data to prevent malicious attacks and data leaks. PHP, as a server-side language widely used in web development, provides some powerful and flexible tools to meet these needs. This article will introduce several common PHP data filtering methods and demonstrate how to use secure encryption algorithms.
2023-07-28
comment 0
671
What are the php encryption algorithms?
Article Introduction:PHP encryption algorithms include MD5 algorithm, SHA algorithm, AES algorithm, RSA algorithm, Base64 encoding, DES algorithm, RC4 algorithm, Blowfish algorithm, etc. Detailed introduction: 1. MD5 algorithm, used to convert data of any length into a fixed-length hash value. In PHP, you can use the md5() function to calculate the MD5 hash value of a string; 2. SHA algorithm, including SHA -1. SHA-256, SHA-512, etc. These algorithms have corresponding functions in PHP; 3. AES algorithm, etc.
2023-08-31
comment 0
563

How to implement RSA encryption and decryption algorithms using PHP and GMP
Article Introduction:How to use PHP and GMP to implement RSA encryption and decryption algorithm RSA encryption algorithm is an asymmetric encryption algorithm that is widely used in the field of information security. In practical applications, it is often necessary to use programming languages to implement RSA encryption and decryption algorithms. PHP is a commonly used server-side scripting language, and GMP (GNUMultiplePrecision) is a high-precision mathematical calculation library that can help us perform large number operations required in the RSA algorithm. This article will introduce how to use PHP and GMP
2023-07-28
comment 0
619

Technical analysis of secure encryption algorithms in PHP
Article Introduction:PHP (Hypertext Preprocessor) is a scripting language widely used in web development. In PHP development, secure encryption algorithms are a very important topic. This article will analyze the security encryption algorithm technology in PHP to help readers better understand and apply these technologies. 1. What is a secure encryption algorithm? A secure encryption algorithm is the process of converting sensitive information into a non-readable form. By using secure encryption algorithms, the confidentiality of data can be protected, ensuring that data is not
2023-06-29
comment 0
1017
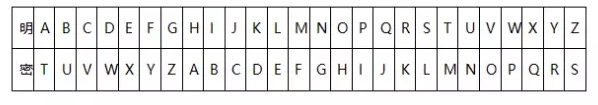
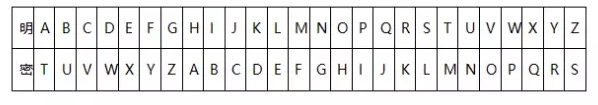
Historical encryption algorithms
Article Introduction:Introduction As a means of security, encryption algorithms are closely related to the lives of most of us. As long as you go online, you will benefit from it, because all websites that use https already use the encryption protocol TLS/SSL. Therefore, we are all passively enjoying the privacy protection and communication security brought by encryption algorithms. In addition, from the security technology level, the network layer to the host file layer, no matter which layer of encryption application or protocol is behind it, it is supported by various encryption algorithms. This article attempts to discuss the development and evolution of this encryption algorithm that is closely related to our online life from ancient times to the present, as well as the centralized key encryption algorithms that have appeared in the entire process one by one, and lead everyone to understand this interesting algorithm behind it. The main function of the encryption algorithm is to turn plaintext into ciphertext to prevent
2023-12-31
comment 0
396

How to implement RSA2 encryption algorithm using php
Article Introduction:The RSA2 algorithm is an asymmetric encryption algorithm with excellent characteristics that is widely used in secure communications. Below we will introduce how to use the php language to implement the RSA2 encryption algorithm. 1. Introduction to the RSA2 algorithm The RSA2 algorithm is an asymmetric encryption algorithm that uses two keys (public key and private key) to perform encryption and decryption operations. Among them, the public key is used to encrypt data, and the private key is used to decrypt data. The RSA2 algorithm implements encryption and decryption operations based on the large number decomposition problem (that is, the problem of factoring a large number). Its confidentiality and reliability are extremely high and it is widely used
2023-03-31
comment 0
1818

How to use PHP to prevent encryption algorithm cracking attacks
Article Introduction:In today's information age, data security is receiving more and more attention. In order to prevent hackers from cracking attacks, many websites use encryption algorithms to encrypt and store data. However, encryption algorithms are not 100% secure. As a popular programming language, PHP is widely used, and measures need to be taken to ensure the security of encryption algorithms. Below, we will introduce how to use PHP to prevent encryption algorithm cracking attacks. 1. Use a high-strength encryption algorithm. Choosing a high-strength encryption algorithm can protect data more effectively and increase the difficulty of cracking. often
2023-06-25
comment 0
1123
How to use PHP and GMP to perform RSA encryption and decryption algorithms for large integers
Article Introduction:How to use PHP and GMP to perform RSA encryption and decryption algorithm for large integers. The RSA encryption algorithm is an asymmetric encryption algorithm that is widely used in the field of data security. It implements the process of public key encryption and private key decryption based on two particularly large prime numbers and some simple mathematical operations. In the PHP language, the calculation of large integers can be realized through the GMP (GNUMultiplePrecision) library, and the encryption and decryption functions can be realized by combining the RSA algorithm. This article will introduce how to use PHP and GMP libraries to
2023-07-28
comment 0
411
Best practices for encryption algorithms in PHP programs
Article Introduction:PHP is a popular open source dynamic scripting language commonly used in the development of web applications. As cyber attacks continue to grow, developers are increasingly concerned about data security, so it is very important to write secure and powerful PHP programs. Encryption algorithms are the foundation for PHP security, and best practices for encryption algorithms help ensure maximum security of your data. 1. Importance of Encryption Algorithms When developing web applications, it is crucial to ensure the security of data. The encryption algorithm is like a lock, which ensures that sensitive data is not
2023-06-06
comment 0
426

Analyze PHP's secure encryption algorithm and digital signature technology
Article Introduction:Analysis of secure encryption algorithms and digital signature technology in PHP With the continuous development of Internet applications, data security issues have become a very important topic. In the field of PHP development, secure encryption algorithms and digital signature technology are important means to ensure the security of data transmission and storage. This article will analyze the security encryption algorithms and digital signature technologies commonly used in PHP to help readers understand how to protect data security. 1. Security encryption algorithm Symmetric encryption algorithm Symmetric encryption algorithm refers to an algorithm that uses the same key for encryption and decryption.
2023-06-30
comment 0
1241

High-speed encryption algorithm and its application in PHP
Article Introduction:With the continuous development of network technology, Web applications are becoming more and more popular, and information security in Web applications is becoming increasingly important. In order to solve the problem of information security in Web applications, people have developed many encryption algorithms, the most famous of which are RSA, DES and other algorithms. However, since decryption of encryption algorithms requires a lot of calculations and time, which will bring a large system burden, a type of encryption algorithm that can quickly encrypt and decrypt in a short time has emerged, which is a high-speed encryption algorithm. This article will introduce high-level functions in PHP
2023-06-23
comment 0
960
How to use encryption algorithm to protect user data of PHP website?
Article Introduction:How to use encryption algorithm to protect user data of PHP website? With the rapid development of the Internet, user data protection of websites has become more and more important. In PHP development, we can use encryption algorithms to protect the security of user data. This article will introduce some commonly used encryption algorithms and how to use them in PHP websites to encrypt user data. 1. Selection of encryption algorithms For PHP websites, we can choose the following commonly used encryption algorithms to protect the security of user data: 1. Symmetric encryption algorithm: This algorithm uses the same encryption algorithm.
2023-08-19
comment 0
579

Explore the future development direction and trends of PHP encryption algorithms
Article Introduction:Explore the future development direction and trend of PHP encryption algorithms. With the rapid development of modern information technology, network security issues have become increasingly prominent. Encryption algorithms, as an important means of protecting data security, have attracted widespread attention. In this field, PHP, as a widely used server-side programming language, is also actively involved in the development of encryption algorithms. This article will explore the future development direction and trends of PHP encryption algorithms and provide relevant code examples for readers' reference. 1. Trends and Challenges Strengthening the Security of Encryption Algorithms The security of encryption algorithms is to protect data completely.
2023-08-18
comment 0
701
Discussion on message encryption and decryption algorithms for developing real-time chat system with PHP
Article Introduction:Overview of message encryption and decryption algorithms for PHP development of real-time chat systems: In today's information age, protecting the security of user data has become particularly important. For real-time chat systems, message encryption and decryption algorithms are key to protecting user privacy and data security. This article will discuss how to implement message encryption and decryption in a real-time chat system developed in PHP, and give corresponding code examples. Symmetric encryption algorithm: Symmetric encryption algorithm uses the same key for encryption and decryption. In real-time chat system, using DES or AES algorithm is
2023-08-25
comment 0
923