Found a total of 107 related content

Code protection technology in C++
Article Introduction:With the popularity of computer technology, computer software has become more and more important. In computer software development, C++ language is widely used. However, developers will find that their C++ code may be stolen, copied, and tampered with by criminals, leading to privacy leaks and theft of trade secrets. Therefore, protecting the security of C++ code is very important for software developers. This article will introduce several code protection techniques in C++. 1. Symbol obfuscation technology Symbol obfuscation technology is a method of converting the names, types, etc. of functions and global variables into
2023-08-22
comment 0
429

Matplotlib image saving secrets revealed
Article Introduction:Matplotlib image saving techniques revealed, specific code examples are needed Matplotlib is a Python library for drawing charts and graphics, providing rich drawing functions. Matplotlib is widely used in data analysis, scientific research, and visualization applications. Compared with displaying the image directly on the terminal, saving the image as a file can be easily shared and displayed with others. This article will introduce you to some commonly used Matplotlib image saving techniques and provide specific code examples.
2024-01-13
comment
188
Thread protection and deadlock detection technology in Java
Article Introduction:Thread protection and deadlock detection technology in Java Java, as an object-oriented programming language widely used in enterprise-level applications, has powerful multi-threaded programming capabilities. In actual application process, thread protection and deadlock detection technology are crucial, they can effectively ensure thread safety and application reliability. This article will discuss this. 1. Thread protection technology Thread protection refers to restricting and controlling shared resources to ensure that multi-threaded programs can ensure the correctness of data when accessing the same shared resource at the same time.
2023-06-09
comment 0
1098

Techniques and recommendations for protecting sensitive information in PHP
Article Introduction:PHP Sensitive Information Protection Technology and Suggestions With the development and popularization of the Internet, the protection of personal sensitive information has become more and more important. When developing websites using PHP, it is crucial to understand how to protect users' sensitive information. This article will introduce some common PHP sensitive information protection techniques and suggestions, and provide some code examples. Using the HTTPS protocol The HTTPS protocol adds an SSL/TLS encryption layer on top of the HTTP protocol to ensure the security of data during transmission. Therefore, for those who need to protect sensitive
2023-08-07
comment 0
422

Identity protection issues in face generation technology
Article Introduction:Identity protection issues in face generation technology require specific code examples. With the rapid development of artificial intelligence technology, face generation technology has gradually become one of the hot spots in research and application. Face generation technology can automatically generate realistic face images through methods such as machine learning and deep neural networks. This technology has huge potential in entertainment, artistic creation, virtual reality and other fields, but it also raises concerns about identity protection. This article will explore the identity protection issues involved in face generation technology and give corresponding code examples. one person
2023-10-09
comment 0
668

Privacy protection issues in artificial intelligence technology
Article Introduction:Privacy Protection Issues in Artificial Intelligence Technology With the development of Artificial Intelligence (AI) technology, our lives have become increasingly dependent on intelligent systems and devices. Whether it is smartphones, smart homes, or self-driving cars, artificial intelligence technology is gradually penetrating into our daily lives. However, while enjoying the convenience of artificial intelligence technology, we also face privacy protection issues. Privacy protection means that personal sensitive information should not be collected or used without authorization
2023-10-09
comment 0
748

The relationship between trusted computing technology and privacy protection
Article Introduction:With the rapid development and popularization of the Internet, people increasingly rely on the network to transmit, store and process data. The ensuing problem is data security and privacy protection. Trusted computing technology emerged as the times require, and this technology has been widely used and promoted. So what is the relationship between trusted computing technology and privacy protection? Let’s explore it together. The basic concept of trusted computing technology refers to ensuring the integrity and credibility of calculation results during the calculation process. Simply put, it is to ensure that the data and programs used as input and output are not tampered with or stolen.
2023-06-11
comment 0
858

Application of trusted computing technology in the field of environmental protection
Article Introduction:As humans become more aware of environmental protection, sustainable development has become a global consensus. In order to achieve this goal, the development of science and technology also plays a vital role. Among them, the application of trusted computing technology in the field of environmental protection is particularly worthy of attention. Trusted computing technology can ensure the integrity, confidentiality and availability of data, and can ensure the security of computing programs and execution environments through verification methods. This is because the Trusted Execution Environment (TEE), a fundamental building block of trusted computing technology, provides a secure, verifiable execution
2023-06-11
comment 0
350

How to keep your technical knowledge updated in the field of PHP development
Article Introduction:How to keep updated technical knowledge in the field of PHP development In the rapidly developing technological era, continuous learning and updating of technical knowledge are crucial for practitioners in any industry. Especially in the field of PHP development, as new technologies and frameworks are constantly emerging, maintaining updated technical knowledge is the key to success. This article will share with you some methods and suggestions on how to keep updated technical knowledge in the field of PHP development. 1. Participate in technical conferences and seminars Participating in technical conferences and seminars is an effective way to acquire the latest technical knowledge. No
2023-09-08
comment 0
395

Python analysis and tips for protecting software privacy
Article Introduction:How to conduct software privacy protection analysis and protection through Python. With the development of the Internet and mobile technology, software has become an indispensable part of people's lives. However, the problem of software privacy leakage has become increasingly serious. In order to protect users' personal privacy, developers and security experts need to use tools and technologies to analyze and protect software privacy protection. Python is a powerful programming language that can be used to develop and implement these protection measures. This article will introduce how to perform software hiding through Python
2023-06-30
comment 0
717
C++在保险科技中的客户画像分析
Article Introduction:是的,C++可以用于保险科技中的客户画像分析,其优势在于强大性能、灵活性和数据处理能力。实战案例涉及预测汽车保险风险,其中包括数据预处理、特征工程、模型训练、模型评估和部署。C++通过提供高效的数据操作、创建复杂算法和集成机器学习库,实现了准确的风险预测,从而为保险科技公司提供了深入了解客户并制定个性化保险产品的能力。
2024-05-17
comment
812
PHP communication tips: How to ensure data security?
Article Introduction:PHP communication tips: How to ensure data security? With the rapid development of the Internet, data security has become an important issue that every developer must consider. For developers who use PHP to communicate, protecting data security is crucial. This article will introduce some PHP communication techniques to ensure data security. 1. Use HTTPS protocol The HTTPS protocol is a protocol that adds SSL/TLS encryption on the basis of the HTTP protocol, which can effectively prevent data from being stolen or tampered with. Required to use HTTPS protocol
2023-08-17
comment 0
429

A review of technology for realizing real-time intelligent security system using PHP
Article Introduction:With the development of society, security work has become more and more important. What follows is the constant updating of security technology. Today's security needs are no longer limited to traditional methods such as access control, but pay more attention to real-time and intelligence. As a programming language widely used in Internet development, PHP has also begun to play an important role in the application of real-time intelligent security systems. 1. Definition of real-time intelligent security system A real-time intelligent security system is a system that integrates multiple technologies such as perception, judgment, and control. It mainly collects, processes, and applies data.
2023-06-28
comment 0
518

Linux Server Security: Advanced Technology for Web Interface Protection.
Article Introduction:Linux Server Security: Advanced Technology for Web Interface Protection With the rapid development of the Internet, Web interfaces have become an indispensable part of many companies and organizations. However, the openness of the Web interface also brings security risks to the server. In order to protect the security of the server, we need to adopt advanced technology to protect the web interface. In this article, we will explore some advanced techniques for securing web interfaces on Linux servers and provide some code examples. Use a firewall A firewall is the first line of defense for server security.
2023-09-08
comment 0
1005
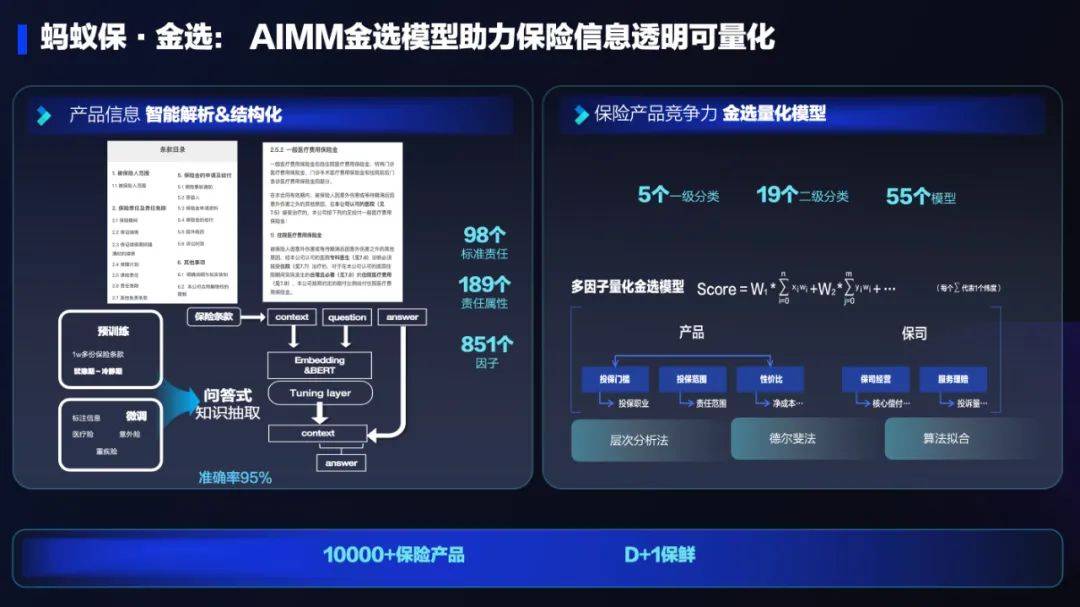
The application of AI technology in Ant Group's insurance business: innovating insurance services and bringing new experiences
Article Introduction:The importance of the insurance industry to society, people's livelihood and the national economy is self-evident. As a risk management tool, insurance provides protection and welfare for the people and promotes economic stability and sustainable development. In the context of the new era, the insurance industry is facing new opportunities and challenges, and needs continuous innovation and transformation to adapt to changes in social needs and adjustments to economic structure. In recent years, China's insurance technology has developed vigorously. Through innovative business models and advanced technological means, we actively promote the digital and intelligent transformation of the insurance industry. The goal of insurtech is to improve the convenience, personalization and intelligence of insurance services and change the face of the traditional insurance industry at an unprecedented speed. This development trend has injected new vitality into the insurance industry and made insurance products closer to the reality of the people.
2023-09-20
comment 0
265

Application and optimization of WebMan technology in online insurance platform
Article Introduction:Application and Optimization of WebMan Technology in Online Insurance Platforms With the rapid development of the Internet, more and more insurance companies have begun to transfer their business to online platforms. In order to provide a better user experience and higher efficiency, the use of WebMan technology has become an integral part of the online insurance platform. This article will introduce the application of WebMan technology in online insurance platforms and give some optimization suggestions. WebMan is a Web-based management system whose main function is to provide an easy-to-use management interface to manage
2023-08-26
comment 0
912
How does trusted computing technology ensure network security?
Article Introduction:With the continuous development of the Internet, people are paying more and more attention to the security issues of the network environment. In today's network security field, trusted computing technology has become a relatively important security method. So, what is trusted computing technology? How does it ensure network security? This article will answer them one by one for everyone. 1. What is trusted computing technology? Trusted Computing technology (Trusted Computing) is a method that ensures the security, reliability and trustworthiness of computers and network systems through means such as hardware, software and security protocols.
2023-06-11
comment 0
1096

What technology does Bitcoin use? What technology does Bitcoin use to ensure transaction security?
Article Introduction:What network technology does Bitcoin use? Bitcoin is a decentralized digital currency that uses blockchain technology to support its operation. Blockchain is a decentralized accounting technology that records Bitcoin transactions and ensures security and immutability. Blockchain is a technology based on a cryptographic consensus mechanism that ensures data security through workload proof. Bitcoin's blockchain network uses the Bitcoin network protocol, which is a special P2P network that enables seamless transactions between users. The Bitcoin network uses a protocol called the Bitcoin Protocol, which ensures the security of Bitcoin and prevents abuse. The protocol also introduces the concept of "blocks" to further ensure the security of Bitcoin and prevent abuse. The Bitcoin network also uses a type of network called “Bitcoin Nodes”
2024-02-04
comment 0
134
How to protect Word documents? Encryption techniques revealed
Article Introduction:In today's information age, Word documents have become an indispensable part of people's work and life, so document protection is particularly important. Not only must the integrity and confidentiality of the document content be protected, but the document must also be prevented from being maliciously tampered with or leaked. This article will introduce some encryption techniques to protect Word documents to help you better protect important documents. 1. Set up password protection. One of the most basic ways to protect Word documents is to set up password protection. By setting a password, you can prevent unauthorized persons from viewing or editing the document contents. in Word
2024-03-25
comment
768

HMAC technology protects PHP data integrity
Article Introduction:HMAC (Hash-basedMessageAuthenticationCode) is a technology used to protect data integrity in computer communications. It combines a hash function and a key and can be used to verify that data has not been tampered with during transmission. In network communications, data security is a very important consideration. Whether during data transmission or storage, we want to ensure data integrity, that is, the data has not been tampered with during transmission or storage. HMAC
2023-06-30
comment 0
1109