
This article mainly introduces the relevant knowledge of Java sensitive information encryption processing: 1) What we want to achieve in sensitive information encryption processing; 2) What I have done in sensitive information encryption processing; 3) How to implement sensitive information encryption. It has a very good reference value. Let’s take a look at it with the editor.
1. What we want to achieve when encrypting sensitive information
Systems often need to encrypt user sensitive information Information is encrypted, and different sensitive information has different encryption requirements.
For example, when encrypting passwords, we often do not need to be reversible. After the user enters the password, the encryption rules of the system are used to directly compare the encrypted and stored password after encoding. Obtaining the comparison result can prove the legitimacy of the user login information.
Then, sometimes in order to prevent data leakage caused by being removed from the database, we have to encrypt some sensitive information (such as ID number, mobile phone number). Such data not only needs to be encrypted, but also needs to be fully displayed or masked in display and other business scenarios, which requires us to decrypt the encrypted content.
2. What have I done to encrypt sensitive information?
Recently, in order to achieve this requirement in the project, some simple designs have been made:
Note: Considering the convenience of querying when maintaining production data, the aes encryption method is used here. This encryption method has the same result as the aes encryption method of mysql, so you can directly use hex and aes_encrypt functions in sql for query; The secret salt can be saved in the configuration file.
1. Use custom annotations. Fields that need to be encrypted and decrypted in each class of the po can be added with this annotation.
2. Declare the Base class and implement the encrypt and decrypt methods. Method implementation Use java reflection and custom annotations
3. All entity objects that need to be encrypted and decrypted must inherit from the Base class
4. The encrypt method is called when the entity class is encrypted, and the encrypt method is called when decrypting. decrypt method, so that the encryption and decryption of sensitive data in the object can be realized
3. Sensitive information encryption implementation
1. First look at the effect
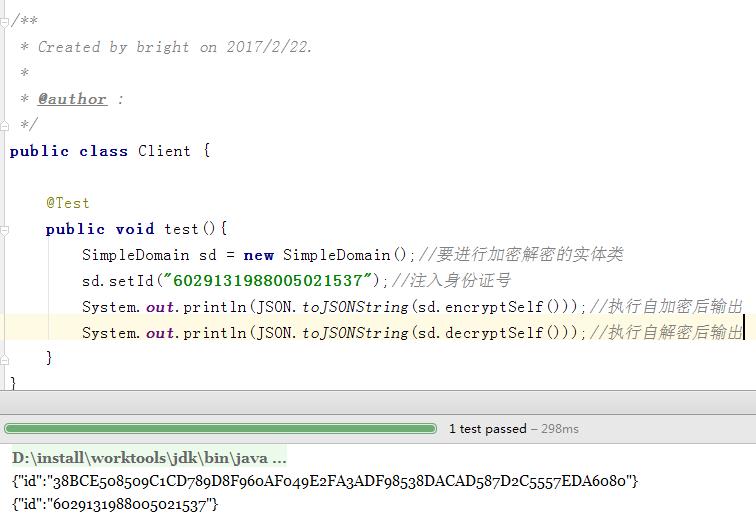
NoteIt is very clear, first set the ID number for the object, and then execute the self-encryption method , returns its own reference, and prints out the encrypted json string; executes the self-decryption method, returns its own reference, and prints out the decrypted json string of the object.
2. Design the implementation structure
crypt | |--annotation | |--DecryptFiled | |--EncryptFiled |--crypt | |--EncryptDecryptInterface |--domain | |--BaseInfo | |--SimpleDomain |--utils | |--MySqlUtils
2.1 First look at the implementation of annotations
/**
* Created by bright on 2017/2/22.
*
* @author :
*/
@Target(ElementType.FIELD)
@Retention(RetentionPolicy.RUNTIME)
public @interface EncryptFiled {
String value() default "";
}
自定义注解The implementation of the two annotations is consistent, the annotation names are just different, and the code of the other annotation will not be posted.
2.2 Define self-encryption and self-decryption interface
Base class implements the self-encryption and self-decryption method in this interface
/**
* Created by bright on 2017/2/22.
*
* @author :
*/
public interface EncryptDecryptInterface {
public <T> T encryptSelf();
public <T> T decryptSelf();
}
自定义接口2.3 Implementation of MysqlUtils
/**
* Created by bright on 2017/2/22.
*
* @author :
*/
@Component
public class MySqlUtils {
private static final String ENCRYPTTYPE= "AES";//加密方式
private static final String ENCODING = "UTF-8";//加密时编码
private static String MYSQLUTILSKEY = "aaa";//加密密盐
private static MySqlUtils mysqlUtils;//单例
private static Cipher encryptCipher ;//加密cipher
private static Cipher decryptChipher;//解密chipher
/**
* 该方法可用在spring项目中使用配置文件设置密盐,默认值为123
* @param key
*/
@Value("${mysql.column.crypt.key:123}")
public void setMysqlutilskey(String key){
MySqlUtils.MYSQLUTILSKEY = key;
}
/**
* encryptCipher、decryptChipher初始化
*/
public static void init(){
try {
encryptCipher = Cipher.getInstance(ENCRYPTTYPE);
decryptChipher = Cipher.getInstance(ENCRYPTTYPE);
encryptCipher.init(Cipher.ENCRYPT_MODE, generateMySQLAESKey(MYSQLUTILSKEY, ENCODING));
decryptChipher.init(Cipher.DECRYPT_MODE, generateMySQLAESKey(MYSQLUTILSKEY, ENCODING));
} catch (InvalidKeyException e) {
throw new RuntimeException(e);
} catch (NoSuchAlgorithmException e) {
throw new RuntimeException(e);
} catch (NoSuchPaddingException e) {
throw new RuntimeException(e);
}
}
/**
* 单例获取方法实现
* @return
*/
public synchronized static MySqlUtils getInstance(){
if(mysqlUtils == null){
mysqlUtils = new MySqlUtils();
init();
}
return mysqlUtils;
}
/**
* 加密算法
* @param encryptString
* @return
*/
public String mysqlAESEncrypt(String encryptString) {
try{
return new String(Hex.encodeHex(encryptCipher.doFinal(encryptString.getBytes(ENCODING)))).toUpperCase();
} catch (BadPaddingException e) {
throw new RuntimeException(e);
} catch (UnsupportedEncodingException e) {
throw new RuntimeException(e);
} catch (IllegalBlockSizeException e) {
throw new RuntimeException(e);
}
}
/**
* 解密算法
* @param decryptString
* @return
*/
public String mysqlAESDecrypt(String decryptString){
try {
return new String(decryptChipher.doFinal(Hex.decodeHex(decryptString.toCharArray())));
} catch (DecoderException nspe) {
throw new RuntimeException(nspe);
} catch (BadPaddingException nsae) {
throw new RuntimeException(nsae);
} catch (IllegalBlockSizeException ike) {
throw new RuntimeException(ike);
}
}
/**
* 产生mysql-aes_encrypt
* @param key 加密的密盐
* @param encoding 编码
* @return
*/
public static SecretKeySpec generateMySQLAESKey(final String key, final String encoding) {
try {
final byte[] finalKey = new byte[16];
int i = 0;
for(byte b : key.getBytes(encoding))
finalKey[i++%16] ^= b;
return new SecretKeySpec(finalKey, "AES");
} catch(UnsupportedEncodingException e) {
throw new RuntimeException(e);
}
}
}
MysqlUtils2.4 Implementation of BaseInfo class
/**
* Created by bright on 2017/2/22.
*
* @author :
*/
public class BaseInfo implements Cloneable, EncryptDecryptInterface {
/**
* 拷贝一个对象,并对新对象进行加密
* 该方法主要用在日志打印上,可防止原对象被加密而影响程序执行
* @param <T>
* @return
*/
public <T extends BaseInfo> T cloneAndEncrypt() {
T cloneT = null;
try {
cloneT = (T) this.clone();
} catch (CloneNotSupportedException e) {
e.printStackTrace();
return null;
}
if(cloneT !=null)
return cloneT.encryptSelf();
throw new RuntimeException("拷贝对象异常");
}
/**
* 重写clone方法
* @return
* @throws CloneNotSupportedException
*/
@Override
protected Object clone() throws CloneNotSupportedException {
try {
return super.clone();
} catch (CloneNotSupportedException e) {
e.printStackTrace();
return null;
}
}
/**
* 实现自加密
*
* @param <T>
* @return
*/
public <T> T encryptSelf() {
Field[] declaredFields = this.getClass().getDeclaredFields();
try {
if (declaredFields != null && declaredFields.length > 0) {
for (Field field : declaredFields) {
if (field.isAnnotationPresent(EncryptFiled.class) && field.getType().toString().endsWith("String")) {
field.setAccessible(true);
String fieldValue = (String) field.get(this);
if (StringUtils.isNotEmpty(fieldValue)) {
field.set(this, MySqlUtils.getInstance().mysqlAESEncrypt(fieldValue));
}
field.setAccessible(false);
}
}
}
} catch (IllegalAccessException e) {
throw new RuntimeException(e);
}
return (T) this;
}
/**
* 实现自解密
*
* @param <T>
* @return
*/
public <T> T decryptSelf() {
Field[] declaredFields = this.getClass().getDeclaredFields();
try {
if (declaredFields != null && declaredFields.length > 0) {
for (Field field : declaredFields) {
if (field.isAnnotationPresent(DecryptFiled.class) && field.getType().toString().endsWith("String")) {
field.setAccessible(true);
String fieldValue = (String)field.get(this);
if(StringUtils.isNotEmpty(fieldValue)) {
field.set(this, MySqlUtils.getInstance().mysqlAESDecrypt(fieldValue));
}
}
}
}
} catch (IllegalAccessException e) {
throw new RuntimeException(e);
}
return (T) this;
}
}
BaseInfo2.5 A simple object
/**
* Created by bright on 2017/2/22.
*
* @author :
*/
public class SimpleDomain extends BaseInfo{
@EncryptFiled
@DecryptFiled
private String id;
public String getId() {
return id;
}
public void setId(String id) {
this.id = id;
}
}
SimpleDomain2.6 Make a call
public class Client {
@Test
public void test(){
SimpleDomain sd = new SimpleDomain();//要进行加密解密的实体类
sd.setId("6029131988005021537");//注入身份证号
System.out.println(JSON.toJSONString(sd.encryptSelf()));//执行自加密后输出
System.out.println(JSON.toJSONString(sd.decryptSelf()));//执行自解密后输出
}
}
ClientThe above is the detailed content of Sample code sharing for Java sensitive information encryption processing. For more information, please follow other related articles on the PHP Chinese website!




