
This article mainly introduces the basic principles of permission control in Linux systems.
In the Linux system, all our operations are essentially operations of process accessing files. To access files, we need to obtain the corresponding access permissions first, and the access permissions are obtained through the security model in the Linux system.
For the security model in Linux systems, we need to know the following two points:
Note that MAC and DAC are not mutually exclusive. DAC is the most basic security model and is usually the most commonly used access control mechanism that Linux must have. MAC is an enhanced security mechanism built on DAC. , is an optional module. Before access, Linux systems usually do a DAC check first. If it fails, the operation fails directly; if it passes the DAC check and the system supports the MAC module, it then does a MAC permission check.
To distinguish the two, we call the Linux system that supports MAC SELinux, which means that it is a security-enhanced system for Linux.
Here, we will talk about the DAC security model in Linux systems.
DAC Security ModelThe core content of DAC is: In Linux, a process theoretically has the same permissions as the user executing it. Everything involved is centered around this core.
User and Group ID Information ControlUser, group, password information
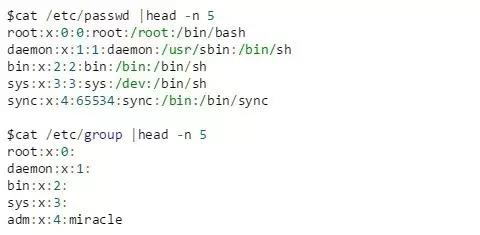
Save user and group information through /etc/passwd and /etc/group, and save passwords and their change information through /etc/shadow, with one record per line.
Users and groups are represented by UID and GID respectively. A user can belong to multiple groups at the same time. By default, each user must belong to a GID with the same UID value and the same name.
For /etc/passwd, each record field is user name: Password (encrypted and saved in /etc/shadow): UID: GID (default UID): Description comment: Home directory: Login shell (first run program of)
For /etc/group, the fields of each record are group name: password (generally there is no group password): GID: group member user list (comma-separated user UID list)
For /etc/shadow, the fields of each record are: Login name: Encrypted password: Last modification time: Minimum time interval: Maximum time interval: Warning time: Inactivity time:
Example
The following are examples of user and group information. The password information in /etc/shadow is encrypted and stored, no example is provided.
file type
File types in Linux are as follows:
Access Control Group
Divided into three groups for control:
Configurable permissions
Common (but not all) permission values are given below, including:
Example
You can check its file type and permissions through ls -l, and modify the permissions through chmod.
for example,
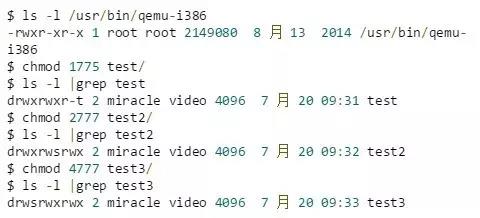
In the output, the first character indicates the file type, among which, ordinary file (-), directory file (d), socket file (s), pipe file (p), character file (c), block file (b), link file (l); The -rwxr-xr-x part starting from the second character represents the permission bit of the file, with a total of 9 bits.
For the file /usr/bin/qemu-i386, the meaning of this permission control is:
Permissions set for test/, test2/, test3/:
Process permissions
For processes, the following attributes are related to file access permissions:
Example
We can use ps and top to select and view processes with euid and ruid. Or use top to view the euid and ruid
of the processExample to view via top:
First enter top to get something like the following
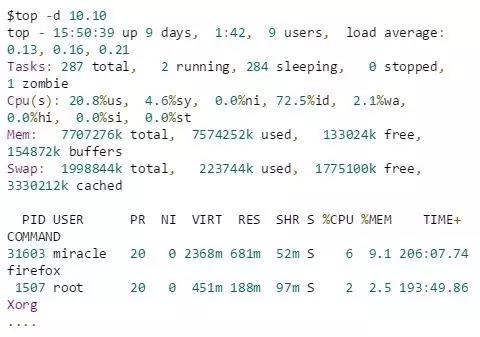
Here, the -d option is used to extend the refresh frequency of top for ease of operation. As can be seen here, only the USER field represents the effective user id of the corresponding process.
Open the display options of read user id:
a. While the top command is running, enter f, and you will see a line similar to the following:
b. Enter c to turn on the display switch of Real user name.
c. Finally, press Return to return to top, and you will see the real user id option. Enter `o` at this time to adjust the column order. Finally we can see the output including `effective user id` and `real user id` as follows:
Permission control policy for process access filesrule
Rough permission control strategy for process access files
For a process to access files, the most important thing is euid, so its permission attributes are all centered on euid.
Modify permission attributes through exec execution file
When calling an executable file through exec:
as follows:
Modify permission attributes through setuid(uid) system call
When modifying permission attributes through setuid(uid):
Example
Let’s give a few more special examples:
set-user-id
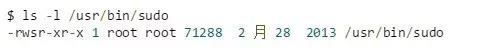
As mentioned earlier, the meaning of this output is that, for the /usr/bin/sudo file,
After this setting, the owner has read, write, and execute permissions, which is no different. But for ordinary user processes that do not belong to the root group, it is quite different.
When an ordinary user process executes the sudo command, it obtains execution permissions through x in others, and then uses s in user to temporarily have the permissions of the owner (root) of the sudo executable file, that is, super permissions.
This is also why ordinary users can execute many commands with administrator privileges through the sudo command.
stick-bit is set

After this setting, everyone has read, write, and execute permissions for the /tmp directory. This is no different. However, the sticky bit t is set in the others part, and its function is quite different.
If the directory does not have the sticky bit set, anyone with write permissions to the directory can delete any files and subdirectories in it, even if he is not the owner of the corresponding file and does not have read or write permission; after the sticky bit is set, The user can only write or delete files and subdirectories that belong to him.
This is why anyone can write files and directories to the /tmp directory, but can only write and delete files or directories they own.
Give an application fragment of the man program to describe the use of set-user-id and saved set-user-id
The man program can be used to display online help manuals. The man program can be installed to specify set-user-ID or set-group-ID for a specified user or group.
The man program can read or overwrite files in certain locations, which is usually configured by a configuration file (usually /etc/man.config or /etc/manpath.config) or command line options.
The man program may execute some other commands to process the file containing the displayed man page.
To prevent processing errors, man switches between two privileges: the privileges of the user running the man command, and the privileges of the owner of the man program.
The main thread that needs to be grasped: When only man is executed, the process privileges are the privileges of the man user. When a child process is executed through man (such as a shell command through !bash), the user switches to the current user. After execution, the user switches to the current user. Switch back.
The process is as follows:
Let’s take a look at what will happen if man starts a shell:
Actually, the way we describe how man uses the setuid function is not particularly correct, because the program may set-user-ID to root. At this time, setuid will change all three uids into the id you set, but we Only the effective user ID needs to be set.
The above is the detailed content of Basic principles of Linux permission control. For more information, please follow other related articles on the PHP Chinese website!




