
This article will describe another buffer overflow situation, that is, buffer underflow. Buffer overflow has been analyzed in the previous topic (see Issue 7). The same reasons apply to buffer underflows, so the factors that cause buffer overflows will not be repeated in this article. To put it simply, buffer underflow refers to the situation where the next-level buffer is overwritten when the filling data overflows. This article describes the dangers of buffer underflow, its signs in source code, and how to fix the problem.
In C/C programs, buffer underflow is a serious vulnerability type that may cause the program to crash or Consequences such as executing malicious code. From January to October 2018, a total of 494 pieces of CVE vulnerability information were involved. Some of the vulnerabilities are as follows:
| Vulnerability Overview | |
|---|---|
| Libc Realpath buffer underflow vulnerability. The vulnerability occurs because the GNU C library does not correctly handle the relative path returned by the getcwd() system call. Other libraries It is also likely to be affected by this. On affected systems, root privileges can be obtained via the SUID binary. | |
| zutils is a compressed file processing utility package. The program supports compression/decompression, compressed file comparison, and compressed file integrity verification. zcat is one of the decompression utilities. A buffer overflow vulnerability exists in zcat in versions prior to zutils 1.8-pre2. An attacker could exploit this vulnerability to cause a denial of service or execute arbitrary code using a specially crafted compressed file. | |
| strongSwan versions prior to 5.6.3 have a buffer underflow vulnerability in the implementation. An attacker can exploit this vulnerability to exhaust resources, resulting in Denial of service. |
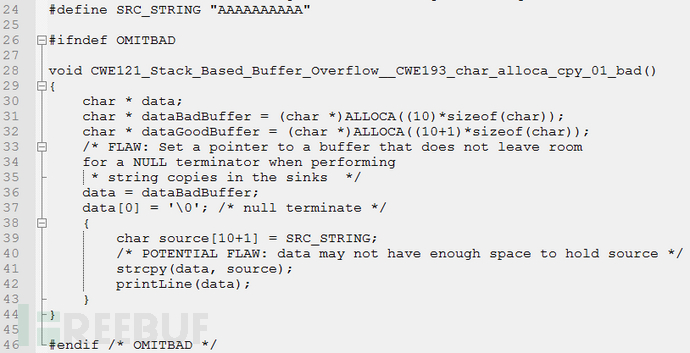
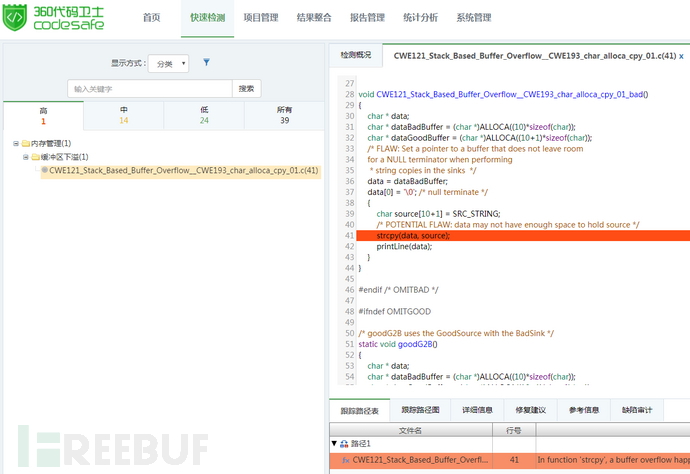
data is executed on line 36 Assignment, through the assignment operation, it can be seen that the pointer data points to dataBadBuffer. When strcpy() is used for memory copy in line 41, the source buffer length is larger than the destination The buffer length thus overflows, and the overflow part exceeds the lower boundary of dataBadBuffer, causing buffer underflow problems.
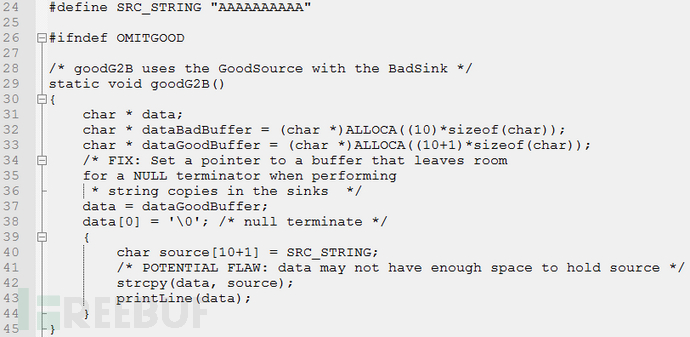
data in line 37, and replace dataPoints to dataGoodBuffer. At this time, the length of data is consistent with source. When strcpy() is used for copy operation in line 42, The source buffer is the same length as the destination buffer, thus avoiding buffer underflow problems. This problem can also be avoided through other methods such as boundary checks.

(1) Try to avoid using unsafe memory operation functions.(2) For memory operation functions that have a clear indication of the return value, the function return value should be effectively judged to determine whether the operation is successful. (3) Boundary checking must be performed when filling data into the buffer.
The above is the detailed content of What does buffer underflow in C/C++ programs mean?. For more information, please follow other related articles on the PHP Chinese website!




