1. LDAP injection
LDAP (Light Directory Access Portocol) is a lightweight directory access protocol based on the X.500 standard, providing services and protocols for accessing directory database methods. Commonly used to form directory services with directory databases. The directory is a professional distributed database optimized for query, browsing and search. It organizes data in a tree structure, similar to the file directory in Linux/Unix systems. It is suitable for storing data that does not change frequently, such as public certificates, security keys, and company physical device information, in the directory. Similar to SQL, LDAP is a search protocol with query syntax and the risk of potential injection attacks. LDAP injection refers to an attack method in which the input string when the client sends a query request contains some special characters, causing the original query structure of LDAP to be modified, thereby allowing access to more unauthorized data.
This article takes the JAVA language source code as an example to analyze the causes and repair methods of the LDAP injection vulnerability in the CWE ID 90: Improper Neutralization of Special Elementsused in an LDAP Query ('LDAP Injection') sample. For details, please see:
-
CWE ID 90: Improper Neutralization of Special Elements used in an LDAP Query ('LDAP Injection')
http://cwe .mitre.org/data/definitions/90.html
-
CWE ID 639: Authorization Bypass ThroughUser-Controlled Key
http://cwe.mitre.org/ data/definitions/639.html
2. Dangers of LDAP injection
LDAP injection is introduced by using users Parameters generate malicious LDAP queries to bypass access control and user privilege escalation by constructing LDAP filters. Through the construction of normal filters, AND and OR operation injection is implemented to obtain sensitive information.
From January 2018 to January 2019, there were a total of 4 vulnerability information related to it in CVE. Some of the vulnerabilities are as follows:
##CVE Number | Overview |
CVE-2018-12689 | phpLDAPadmin 1.2.2 allowed via cmd.php? LDAP injection with a crafted serverid parameter in the cmd=loginform request or a crafted username and password in the login panel. |
CVE-2018-5730 | MIT krb5 1.6 or later allows authenticated kadmin to add principals to the LDAP Kerberos database by providing "linkdn" and "containerdn" database parameters to bypass the DN container check, or by providing the DN string as an extension to the DN container check. |
CVE-2016-8750 | Apache Karaf before 4.0.8 uses the LDAPLoginModule to authenticate users through LDAP. However, the username is not encoded correctly and is therefore vulnerable to an LDAP injection attack, resulting in a denial of service. |
CVE-2011-4069 | PacketFence html/admin/login.php before 3.0.2 allows remote attackers to conduct an LDAP injection attack via a crafted Username bypasses authentication. |
3. Sample code
The example comes from Samate Juliet Test Suite for Java v1.3 (https://samate.nist.gov/SARD/testsuite.php), source File name: CWE90_LDAP_Injection__connect_tcp_01.java.
3.1 Defect Code
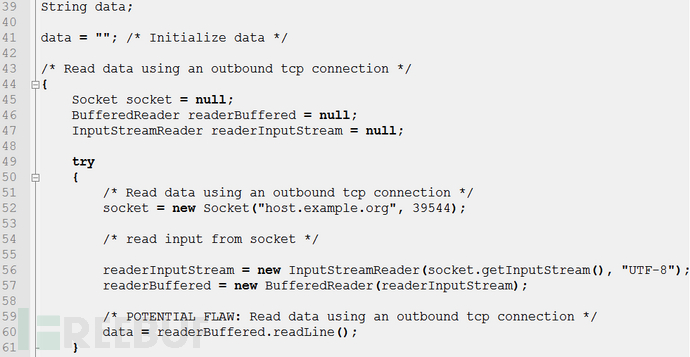
In the above example code lines 39-61, the program makes a TCP connection and reads the Socket The data is assigned to the variable data, an LDAP query statement is dynamically constructed on line 118, and executed on line 119. LDAP encapsulates common object classes for personnel organizations. For example, a person contains attributes such as last name (sn), first name (cn), phone number (telephoneNumber), and password (userPassword). This query is to verify whether there is an employee named variable data, but it does not perform any filtering on the content of variable data. Using the simplest injection method, if the value of the incoming parameter is "*", then the constructed dynamic query condition is "(cn=*)", which can query the information of all employees, leading to information leakage.
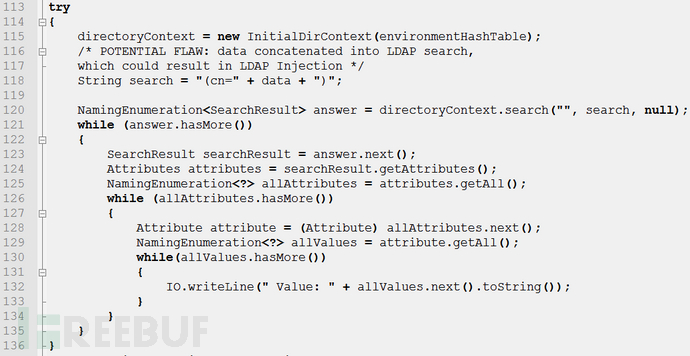
After testing the sample code above with 360 Code Guard, it was found that there was an "LDAP injection" vulnerability, and the security level was rated as high. The source of data pollution and data flow direction can be obtained through trace path analysis and the defect is reported at line 120 of the code, as shown in Figure 1
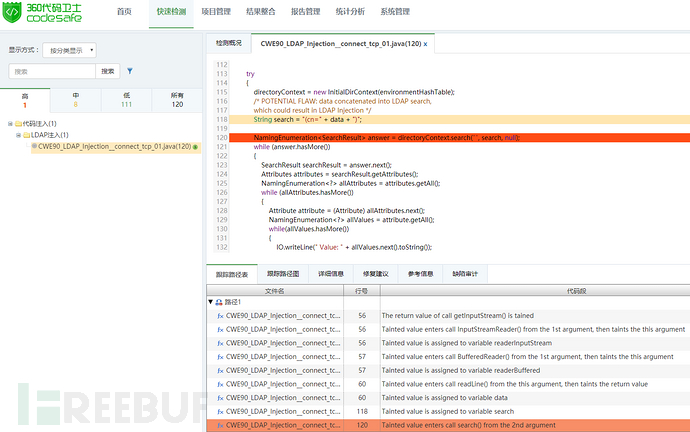
Figure 1: LDAP injection Detection example
3.2 Fix code
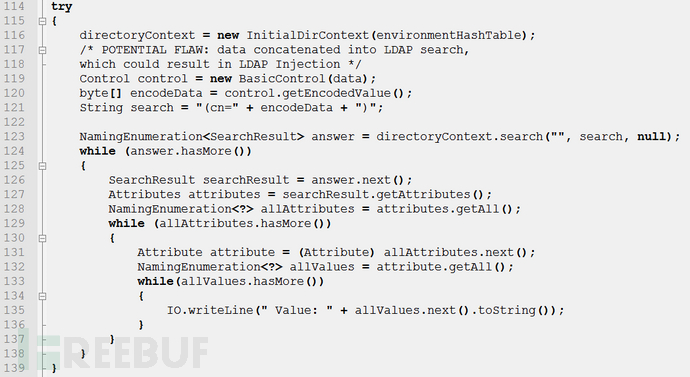
In the above fix code, line 119 uses javax. naming.ldap Extension class under the package BaseControl receives the parameters that need to be processed, line 120 control The object calls the getEncodedValue() method to receive the parameters data is encoded, and the encoded value is the ASN.1BER encoding value corresponding to the character. The encoded byte array does not contain special characters involved in command parsing, and an LDAP query statement with normal structure and content can be constructed, thus avoiding the occurrence of LDAP injection.
Use 360 Code Guard to detect the repaired code, and you can see that there is no "LDAP injection" defect. As shown in Figure 2:
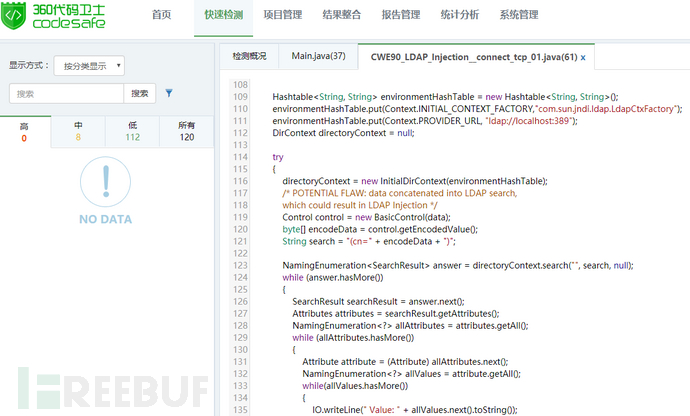
Figure 2: Detection results after repair
4. How to avoid LDAP injection
The root cause of LDAP injection is that attackers use LDAP metacharacters to modify the meaning of LDAP queries. When constructing an LDAP filter, programmers need to clarify which characters should be treated as command parsing and which characters should be treated as data parsing. In order to prevent attackers from invading programmers' various preset situations, a whitelist method should be used to ensure that the user-controlled values in LDAP queries come entirely from a predetermined character set and should not contain any LDAP metacharacters. If user-controlled numerical range requirements must contain LDAP metacharacters, the corresponding encoding mechanism should be used to escape the meaning of these metacharacters in LDAP queries.
like&,! ,|,=,,,,,-,",',; these characters are not used under normal circumstances. If they appear in the user's input, they need to be escaped with backslashes.
-
There are also some characters such as (,), \, *, /, NUL. These characters not only need to be processed with backslashes, but also the characters must be converted into corresponding ASCII code values.
The above is the detailed content of How to understand LDAP injection. For more information, please follow other related articles on the PHP Chinese website!





