 Database
Database
 Redis
Redis
 The principle and implementation method of distributed locks implemented by Redis
The principle and implementation method of distributed locks implemented by Redis
The principle and implementation method of distributed locks implemented by Redis
With the popularity of distributed systems, distributed locks are becoming more and more important. Distributed lock is a mechanism that ensures that only one process or thread can operate at the same time in a distributed system. Distributed locks are a very common problem in many applications in distributed environments. Redis is a high-performance in-memory database that supports multiple data structures and is widely used in distributed locks. This article will introduce the principle and implementation method of distributed locks implemented by Redis.
1. The principle of distributed lock implemented by Redis
Implementing a lock in a distributed system requires solving some problems, such as how to achieve mutual exclusion and how to ensure consistency. For Redis to implement distributed locks, the main principle is to ensure lock mutual exclusion and consistency through Redis transactions. Redis transactions provide the ability to package multiple commands into a transaction and then execute them all at once. When issuing a transaction, the server will start recording a sequence of Redis commands executed by the transaction.
Therefore, Redis mainly has the following three steps to implement distributed locks:
1. Try to acquire the lock
In Redis, you can use the SETNX command (SET if Not eXists ) to determine whether a key exists. If it does not exist, it returns 1 and sets the value of the key. If the key already exists, it returns 0. Therefore, the SETNX command can be used to implement the process of acquiring the lock.
2. Set the lock timeout
In order to prevent locking, you need to set a timeout for the lock. When the lock holder has not released the lock after a period of time, the lock will will be forcibly released.
3. Release the lock
Use the DEL command in the Redis transaction to release the lock and delete the lock key from Redis.
2. How Redis implements distributed locks
Through the introduction of the above steps, we can know that the main principle of Redis implementing distributed locks is to grab the lock through the SETNX command, thereby passing the transaction to perform locking and unlocking operations. On this basis, we will introduce two ways to implement distributed locks in Redis: based on Redis single node and based on Redis cluster.
1. Based on Redis single node
We can easily implement distributed locks based on Redis single node by simply using the Redis SETNX and DEL commands. The code is as follows.
public Boolean tryLock(String key, String value, long expireTime) {
Jedis jedis = jedisPool.getResource();
String result = jedis.set(key, value, "NX", "PX", expireTime);
jedis.close();
return "OK".equalsIgnoreCase(result);
} Among them, key is the resource that needs to be locked, value is the unique identifier of the lock, and expireTime is the timeout time of the lock.
For the process of trying to obtain a lock, you can try to set a non-existent key through the SetNX command. If the key exists, it means that the lock has been acquired by other clients. After the lock is successfully locked, the lock identification and timeout time need to be set. At the same time, it is necessary to ensure that the lock holder has the opportunity to release the lock before the timeout period expires, otherwise the lock will be forcibly released.
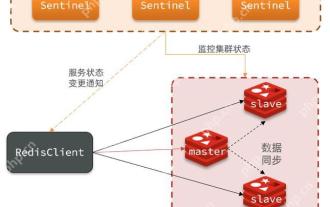
2. Based on Redis cluster
In a Redis cluster environment, the implementation based on a single node cannot meet the high availability requirements. Therefore, we need to implement distributed locks based on Redis cluster through Redis Cluster mode.
In Redis Cluster mode, Redis divides the nodes in the cluster into different slots, and each slot stores different key-value pairs. Therefore, we can allocate different locks to different slots to achieve high availability of distributed locks. In Redis Cluster mode, the code for Redis to implement distributed locks is as follows.
public boolean tryLock(String key, String value, int expireTime) {
JedisCluster jedisCluster = jedisClusterFactory.getJedisCluster();
String result = jedisCluster.set(key, value, "NX", "PX", expireTime);
return "OK".equalsIgnoreCase(result);
} Among them, key is the resource that needs to be locked, value is the unique identifier of the lock, and expireTime is the timeout time of the lock.
In Redis Cluster mode, the SET command will store key and value to the correct node. By distinguishing locks in different slots, we can achieve high availability of distributed locks and avoid single points of failure.
3. Summary
This article mainly introduces the principle and implementation method of Redis to implement distributed locks. Distributed locks based on Redis single node can be realized by simply using SETNX and DEL commands. In Redis Cluster mode, we can allocate different locks to different slots to achieve high availability of distributed locks and avoid single points of failure. The implementation of distributed locks needs to consider many factors, including lock mutual exclusion, consistency, and high availability. In practical applications, it is necessary to choose the appropriate lock implementation method according to the specific situation.
The above is the detailed content of The principle and implementation method of distributed locks implemented by Redis. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)
 Redis master-slave replication failure troubleshooting process
Jun 04, 2025 pm 08:51 PM
Redis master-slave replication failure troubleshooting process
Jun 04, 2025 pm 08:51 PM
The steps for troubleshooting and repairing Redis master-slave replication failures include: 1. Check the network connection and use ping or telnet to test connectivity; 2. Check the Redis configuration file to ensure that the replicaof and repl-timeout are set correctly; 3. Check the Redis log file and find error information; 4. If it is a network problem, try to restart the network device or switch the alternate path; 5. If it is a configuration problem, modify the configuration file; 6. If it is a data synchronization problem, use the SLAVEOF command to resync the data.
 Quick location and handling of Redis cluster node failures
Jun 04, 2025 pm 08:54 PM
Quick location and handling of Redis cluster node failures
Jun 04, 2025 pm 08:54 PM
The quick location and processing steps for Redis cluster node failure are as follows: 1. Confirm the fault: Use the CLUSTERNODES command to view the node status. If the fail is displayed, the node will fail. 2. Determine the cause: Check the network, hardware, and configuration. Common problems include memory limits exceeding. 3. Repair and restore: Take measures based on the reasons, such as restarting the service, replacing the hardware or modifying the configuration. 4. Notes: Ensure data consistency, select appropriate failover policies, and establish monitoring and alarm systems.
 Methods and strategies to solve the problem of split brain in Redis cluster
Jun 04, 2025 pm 08:42 PM
Methods and strategies to solve the problem of split brain in Redis cluster
Jun 04, 2025 pm 08:42 PM
Effective solutions to the problem of split brain in Redis cluster include: 1) Network configuration optimization to ensure connection stability; 2) Node monitoring and fault detection, real-time monitoring with tools; 3) Failover mechanism, setting high thresholds to avoid multiple master nodes; 4) Data consistency guarantee, using replication function to synchronize data; 5) Manual intervention and recovery, and manual processing if necessary.
 Performance comparison and joint application scenarios between Redis and RabbitMQ
Jun 04, 2025 pm 08:45 PM
Performance comparison and joint application scenarios between Redis and RabbitMQ
Jun 04, 2025 pm 08:45 PM
Redis and RabbitMQ each have their own advantages in performance and joint application scenarios. 1.Redis performs excellently in data reading and writing, with a latency of up to microseconds, suitable for high concurrency scenarios. 2.RabbitMQ focuses on messaging, latency at milliseconds, and supports multi-queue and consumer models. 3. In joint applications, Redis can be used for data storage, RabbitMQ handles asynchronous tasks, and improves system response speed and reliability.
 Configuration suggestions for improving Redis persistence performance
Jun 04, 2025 pm 08:48 PM
Configuration suggestions for improving Redis persistence performance
Jun 04, 2025 pm 08:48 PM
Methods to improve Redis persistence performance through configuration include: 1. Adjust the save parameters of RDB to reduce the snapshot generation frequency; 2. Set the appendfsync parameter of AOF to everysec; 3. Use AOF and RDB in combination; 4. Use no-appendfsync-on-rewrite parameters to optimize AOF rewrite performance; 5. Enable hybrid persistence mode. These configurations can improve performance while ensuring data security.
 Methods to implement data deduplication using Redis sets (Sets)
Jun 04, 2025 pm 08:33 PM
Methods to implement data deduplication using Redis sets (Sets)
Jun 04, 2025 pm 08:33 PM
The Redis collection is selected to implement data deduplication because it supports quick insertion and search, and it automatically deduplication. 1) The Redis collection is based on an ordered collection structure without repeat elements, and is suitable for scenarios where quick insertion and query are required. 2) But you need to pay attention to its memory usage, because each element occupies memory. 3) It can be optimized for use through shard storage, regular cleaning and combined with other storage.
 How to use PHP combined with AI to achieve text error correction PHP syntax detection and optimization
Jul 25, 2025 pm 08:57 PM
How to use PHP combined with AI to achieve text error correction PHP syntax detection and optimization
Jul 25, 2025 pm 08:57 PM
To realize text error correction and syntax optimization with AI, you need to follow the following steps: 1. Select a suitable AI model or API, such as Baidu, Tencent API or open source NLP library; 2. Call the API through PHP's curl or Guzzle and process the return results; 3. Display error correction information in the application and allow users to choose whether to adopt it; 4. Use php-l and PHP_CodeSniffer for syntax detection and code optimization; 5. Continuously collect feedback and update the model or rules to improve the effect. When choosing AIAPI, focus on evaluating accuracy, response speed, price and support for PHP. Code optimization should follow PSR specifications, use cache reasonably, avoid circular queries, review code regularly, and use X
 Tools and metrics to monitor the health status of Redis clusters
Jun 04, 2025 pm 08:39 PM
Tools and metrics to monitor the health status of Redis clusters
Jun 04, 2025 pm 08:39 PM
Through tools such as redis-cli, RedisInsight, Prometheus and Grafana, as well as focusing on memory usage, number of connections, cluster node status, data consistency and performance indicators, the health status of the Redis cluster can be effectively monitored.






