How Laravel fixes website vulnerabilities
The following tutorial column is developed by Laravel to introduce you to Laravel's method of repairing website vulnerabilities. I hope it will be helpful to friends in need!

The Laravel framework is a development framework currently used by many websites and APP operators. Because there are so many websites used, many attackers are constantly attacking We conducted vulnerability testing on the website. When we conducted vulnerability testing on the system, we found that there was a REC vulnerability. It was mainly an XSRF vulnerability. Let's analyze the vulnerability in detail, how to exploit it, and how to fix it. Record.
The exploitation of this Laravel REC vulnerability requires conditions. The APP_KEY must be leaked before it can be successfully exploited and triggered. Our SINE security technology discovered a total of There are two places where website vulnerabilities can occur. The first is the cookies field in the Post packet, and the other is the HTTP header field where malicious total code can be inserted into the website backend.
Let’s build it Let’s take a look at the environment for website vulnerability testing. We use linux centos system, PHP5.5 version, the database is mysql, and it is built using apache environment. The Laravel version used is 5.6.28. First, we go to the official website to download the version and unzip it to the apache setting. Website directory path. First of all, in our post data, we can see that in our code, we will call more than a dozen classes, call objects in the classes, and assign parameters. In the cookies and verifycsrftoken values, we found that app_key can be used for vulnerability exploitation. First we use cookies to reproduce it:

The code is as follows:
POST / HTTP/1.2 Host: 127.0.0.2:80 Cookie: safe_SESSION=PHPSTORM; 5LqG5L+d6K+B5omA6L6T5Ye655qE57yW56CB5L2N5Y+v6K+75a2X56ym77yMQmFzZTY05Yi25a6a5LqG5LiA5Liq57yW56CB6KGo77yM5Lul5L6/6L+b6KGM57uf5LiA6L2s5o2i44CC57yW56CB6KGo55qE5aSn5bCP5Li6Ml42PTY077yM6L+Z5Lmf5pivQmFzZTY05ZCN56ew55qE55Sx5p2l44CCDQoNCkJhc2U2NOe8lueggeihqA==; Content-Type: application/x-www-form- Connection: open Content-Length: 1
The above code is in the cookies column. The encrypted value is what we want The forged attack code submits the POST request to the website. It will first decrypt the APP_key and assign it a value. If the decryption is successful, the value in the cookies will be verified and deserialized, and then If the vulnerability occurs, the RCE vulnerability will be triggered.
Let’s test the vulnerability using the http header method. First, we will construct a code similar to cookies, as follows:
POST / HTTP/1.2 Host: 127.0.0.2:80 X-XSRF-TOKEN: +B5omA6L6T5Ye655qE57yW56CB5L2N5Y+v6K+75a2X56ym77yMQmFzZTY05Yi25a6a5LqG5LiA5Liq57yW56CB6KGo77yM5Lul5L6/6L+b6KGM57uf5LiA6L2s5o2i44CC57yW56CB6KGo55qE5aSn5bCP5Li6Ml42PTY077yM6L+Z5Lmf5pivQmFzZTY05ZCN56ew55qE55Sx5p2l44CCDQoNCkJhc2U2NOe8lueggeihqA==; Content-Type: application/x-www-form- Connection: open Content-Length: 1
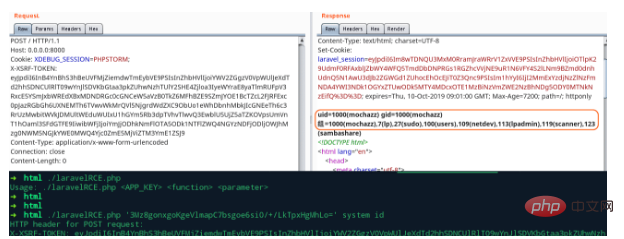
Look here at the X-XSRF-TOKEN: value. The Laravel framework will judge and verify this value during the submission process. If the decryption is successful, the deserialization operation will be performed. I won’t go through it one by one here. Introduction and explanation.
How to fix Laravel's vulnerability?
Our SINE security technology upgraded the Laravel version and found that the latest 5.6.30 version has the rce vulnerability Repairs have been made. From our code comparison, we can see that the decryption and parsing operations of cookies have been judged, and the static::serialized() value has been written more. This is also added to X-XSRF-TOKEN. Value. If you don’t know much about the code, you can also find a professional website security company to repair it. This is the website vulnerability detection and testing for Laravel. I also hope that through this sharing, more people can understand it. Website vulnerabilities, the causes of vulnerabilities, and how to fix them. Only when the website is safe can we open up our hands and feet to develop the market and do a good job in marketing.
The above is the detailed content of How Laravel fixes website vulnerabilities. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)
 How to implement a referral system in Laravel?
Aug 02, 2025 am 06:55 AM
How to implement a referral system in Laravel?
Aug 02, 2025 am 06:55 AM
Create referrals table to record recommendation relationships, including referrals, referrals, recommendation codes and usage time; 2. Define belongsToMany and hasMany relationships in the User model to manage recommendation data; 3. Generate a unique recommendation code when registering (can be implemented through model events); 4. Capture the recommendation code by querying parameters during registration, establish a recommendation relationship after verification and prevent self-recommendation; 5. Trigger the reward mechanism when recommended users complete the specified behavior (subscription order); 6. Generate shareable recommendation links, and use Laravel signature URLs to enhance security; 7. Display recommendation statistics on the dashboard, such as the total number of recommendations and converted numbers; it is necessary to ensure database constraints, sessions or cookies are persisted,
 How to use accessors and mutators in Eloquent in Laravel?
Aug 02, 2025 am 08:32 AM
How to use accessors and mutators in Eloquent in Laravel?
Aug 02, 2025 am 08:32 AM
AccessorsandmutatorsinLaravel'sEloquentORMallowyoutoformatormanipulatemodelattributeswhenretrievingorsettingvalues.1.Useaccessorstocustomizeattributeretrieval,suchascapitalizingfirst_nameviagetFirstNameAttribute($value)returningucfirst($value).2.Usem
 What are Repository Contracts in Laravel?
Aug 03, 2025 am 12:10 AM
What are Repository Contracts in Laravel?
Aug 03, 2025 am 12:10 AM
The Repository pattern is a design pattern used to decouple business logic from data access logic. 1. It defines data access methods through interfaces (Contract); 2. The specific operations are implemented by the Repository class; 3. The controller uses the interface through dependency injection, and does not directly contact the data source; 4. Advantages include neat code, strong testability, easy maintenance and team collaboration; 5. Applicable to medium and large projects, small projects can use the model directly.
 How to use subqueries in Eloquent in Laravel?
Aug 05, 2025 am 07:53 AM
How to use subqueries in Eloquent in Laravel?
Aug 05, 2025 am 07:53 AM
LaravelEloquentsupportssubqueriesinSELECT,FROM,WHERE,andORDERBYclauses,enablingflexibledataretrievalwithoutrawSQL;1.UseselectSub()toaddcomputedcolumnslikepostcountperuser;2.UsefromSub()orclosureinfrom()totreatsubqueryasderivedtableforgroupeddata;3.Us
 How to create a RESTful API with Laravel?
Aug 02, 2025 pm 12:31 PM
How to create a RESTful API with Laravel?
Aug 02, 2025 pm 12:31 PM
Create a Laravel project and configure the database environment; 2. Use Artisan to generate models, migrations and controllers; 3. Define API resource routing in api.php; 4. Implement the addition, deletion, modification and query methods in the controller and use request verification; 5. Install LaravelSanctum to implement API authentication and protect routes; 6. Unify JSON response format and handle errors; 7. Use Postman and other tools to test the API, and finally obtain a complete and extensible RESTfulAPI.
 Laravel MVC: architecture limitations
Aug 03, 2025 am 12:50 AM
Laravel MVC: architecture limitations
Aug 03, 2025 am 12:50 AM
Laravel'simplementationofMVChaslimitations:1)Controllersoftenhandlemorethanjustdecidingwhichmodelandviewtouse,leadingto'fat'controllers.2)Eloquentmodelscantakeontoomanyresponsibilitiesbeyonddatarepresentation.3)Viewsaretightlycoupledwithcontrollers,m
 Understanding MVC: How Laravel Implements the Model-View-Controller Pattern
Aug 02, 2025 am 01:04 AM
Understanding MVC: How Laravel Implements the Model-View-Controller Pattern
Aug 02, 2025 am 01:04 AM
LaravelimplementstheMVCpatternbyusingModelsfordatamanagement,Controllersforbusinesslogic,andViewsforpresentation.1)ModelsinLaravelarepowerfulORMshandlingdataandrelationships.2)ControllersmanagetheflowbetweenModelsandViews.3)ViewsuseBladetemplatingfor
 How to handle recurring payments with Laravel Cashier?
Aug 06, 2025 pm 01:38 PM
How to handle recurring payments with Laravel Cashier?
Aug 06, 2025 pm 01:38 PM
InstallLaravelCashierviaComposerandconfiguremigrationandBillabletrait.2.CreatesubscriptionplansinStripeDashboardandnoteplanIDs.3.CollectpaymentmethodusingStripeCheckoutandstoreitviasetupintent.4.SubscribeusertoaplanusingnewSubscription()anddefaultpay







