
The content of this article is about the manual injection of php mysql in DVWA. It has a certain reference value. Now I share it with you. Friends in need can refer to it
The dvwa security level is low. When entering the sql injection page, you are prompted to enter the user id. If you enter the correct id, the id first name and surname information will be displayed.
Try to enter "'" and an error is returned. Injection points exist.
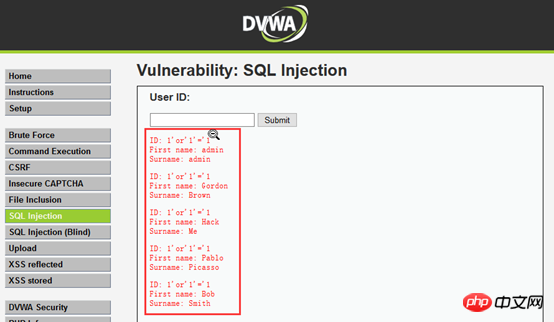
Try to traverse the database table, and the value prompted is ID. It is initially judged that it is a numeric type injection. Try entering: 1 or 1=1, try to traverse the database table. The result failed.

#1 or 1=1 failed to traverse the database table. The guessing program regarded this as a character type. You can try to enter 1' or '1'='1 and then traverse all the contents in the database. Let's try to combine different statements to get different results.
##Use the order by statement to query, enter 1'order by 1 - - The page displays normally, 1'order by 2 - - displays normally, 1'order by 3 - - an error is reported, and the query result value is judged to be 2 columns. (Note that there are spaces after - - in the statement and no spaces between - -)

Use the three built-in functions user(), database(), and version() to get the database account name, database name, and database version information. First, parameter injection 1' and 1=2 union select 1,2 - -(There is no space between - - and there is a space after - -). It is obtained that the first name is displayed as the value of the first column of the query result, and the surname is displayed as the value of the second column of the query result.


By injecting 1' and exists(select * from users) - - Guess the table name in the dvwa database (the table name in this statement is users, the table is not actually stored Username and password)
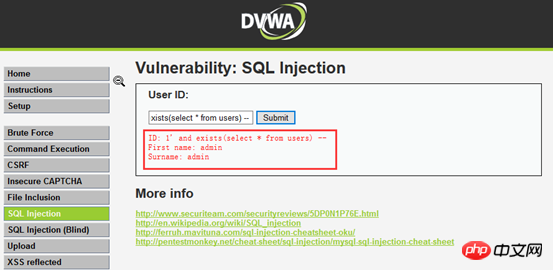
##Guess the field name: 1' and exists(select field name from table name) - -, here the field names first_name and last_name are actually tested. The actual statements 1' and exists(select first_name from users) - - and 1' and exists(select last_name from users) - - guess the field name.

## Explode the contents of the fields in the database. 1' and 1=2 union select first_name,last_name from users - - In fact, if this is a table that stores administrator accounts, then the username and password can be revealed. 
source code
 Related recommendations:
Related recommendations:
The above is the detailed content of DVWA manual injection of php+mysql. For more information, please follow other related articles on the PHP Chinese website!




