 web3.0
web3.0
 Is BitoPro a fraud? Is it safe? Analysis of the security of BitoPro and common fraud methods of BitoPro
Is BitoPro a fraud? Is it safe? Analysis of the security of BitoPro and common fraud methods of BitoPro
Is BitoPro a fraud? Is it safe? Analysis of the security of BitoPro and common fraud methods of BitoPro
Is BitoPro Coin Quest Exchange safe? How to prevent fraud?
This article will introduce in detail the compliance, security measures and common fraud methods of BitoPro coin exchange to help users use the platform safely.

Is BitoPro Coin Trust Exchange legal?
BitoPro Coin Trust is a legally registered cryptocurrency exchange in Taiwan. Its founder and CEO Mr. Zheng Guangtai is also the first chairman of the Virtual Currency Business Association (VASP Association). BitoPro has obtained compliance certification from Taiwan’s Money Laundering Prevention Law and went online in 2018. It is one of Taiwan’s top three cryptocurrency exchanges. BitoPro cooperates with FamilyMart convenience stores, and users can use FamilyMart consumption points to exchange for virtual currency. It is recommended that users directly use the more comprehensive BitoPro platform to trade.
Is BitoPro Coin Quarantine Exchange safe?
BitoPro is committed to ensuring the safety of user assets. In addition to obtaining the compliance license from the Financial Commission, it has also passed the ISO 27001 information security management system certification and provides users with Lockton Insurance and a fiat currency trust contract signed with Far East Bank to ensure the security of funds.
- ISO 27001 certification: Ensure information security and stability and reduce risks.
- Crypto Asset Insurance: User assets are covered by insurance.
- Fire currency trust contract: Cooperate with Far East Bank to further protect user funds.
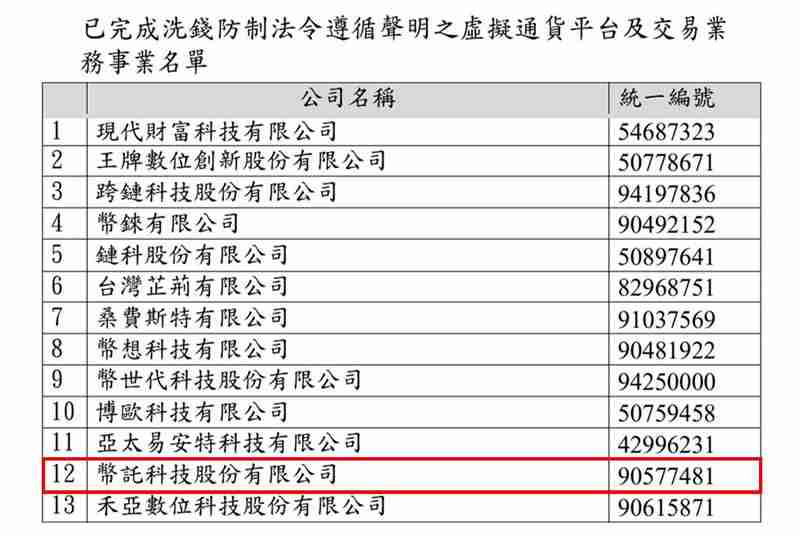
Compliance of BitoPro Coin Holdings
BitoPro complies with relevant regulations of the Financial Commission and has completed the CPC Money Laundering Prevention Law certification. In addition, BitoPro commissioned PwC and Dow Jones Risk & Compliance for real-name verification of customers, and is the first exchange in Taiwan to implement a real-name system.
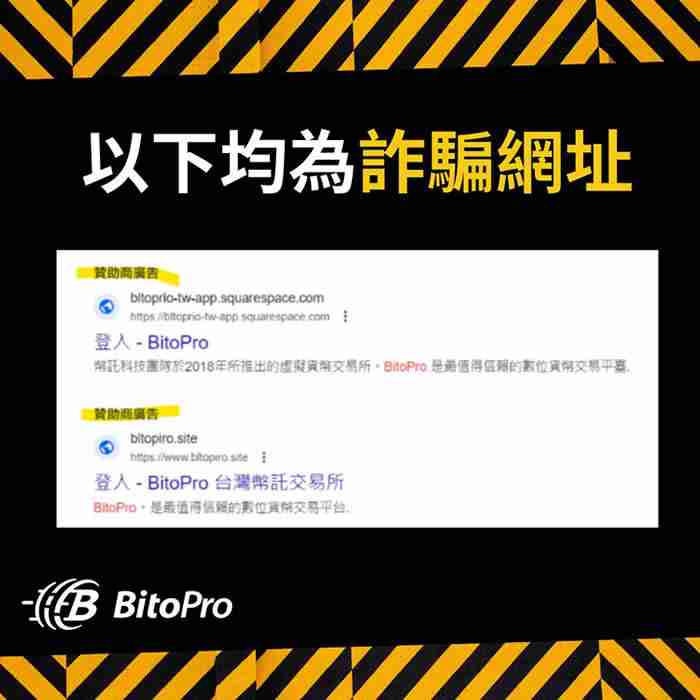
Common fraud methods for BitoPro coin custody
Although BitoPro itself is not a fraud platform, we still need to be wary of criminals using their names to commit fraud. Here are some common techniques:
1. Phishing website/application: Criminals forge BitoPro official website or APP to induce users to disclose personal information or funds. Please be sure to visit the official website: //m.sbmmt.com/link/2f4e2fe0d640b5eca5eaa6de05759928

2. Fake employees: Criminals pretend to be BitoPro employees, contact users through social media and other channels, and defraud funds or account information. Please do not trust information from unofficial channels.
3. Head Account: Fraud Group publishes false recruitment information, inducing job seekers to register for BitoPro accounts and use their accounts for illegal activities such as money laundering. Never disclose personal information and account passwords easily.
What should I do if I get cheated on BitoPro coin custody?
If you suspect fraud, please take the following steps immediately:
1. Stop depositing: Stop sending money to any suspicious accounts immediately.
2. Collect evidence: Keep all relevant evidence, such as chat history, transaction history, etc.
3. Report to the exchange: Contact BitoPro official customer service to report and provide relevant evidence:
- Submit the question: //m.sbmmt.com/link/ac411f98b72734d56053360159f88447
- Telectronic customer service: 886-2-86668968
- Email: support@bitopro.com
4. Call the police: Report the case to the local police and provide the collected evidence. Please note that the 165 anti-fraud line is for consultation only and is not a formal reporting channel.
The above is the detailed content of Is BitoPro a fraud? Is it safe? Analysis of the security of BitoPro and common fraud methods of BitoPro. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1378
1378
 52
52
 How to configure Debian Apache log format
Apr 12, 2025 pm 11:30 PM
How to configure Debian Apache log format
Apr 12, 2025 pm 11:30 PM
This article describes how to customize Apache's log format on Debian systems. The following steps will guide you through the configuration process: Step 1: Access the Apache configuration file The main Apache configuration file of the Debian system is usually located in /etc/apache2/apache2.conf or /etc/apache2/httpd.conf. Open the configuration file with root permissions using the following command: sudonano/etc/apache2/apache2.conf or sudonano/etc/apache2/httpd.conf Step 2: Define custom log formats to find or
 How Tomcat logs help troubleshoot memory leaks
Apr 12, 2025 pm 11:42 PM
How Tomcat logs help troubleshoot memory leaks
Apr 12, 2025 pm 11:42 PM
Tomcat logs are the key to diagnosing memory leak problems. By analyzing Tomcat logs, you can gain insight into memory usage and garbage collection (GC) behavior, effectively locate and resolve memory leaks. Here is how to troubleshoot memory leaks using Tomcat logs: 1. GC log analysis First, enable detailed GC logging. Add the following JVM options to the Tomcat startup parameters: -XX: PrintGCDetails-XX: PrintGCDateStamps-Xloggc:gc.log These parameters will generate a detailed GC log (gc.log), including information such as GC type, recycling object size and time. Analysis gc.log
 How to implement file sorting by debian readdir
Apr 13, 2025 am 09:06 AM
How to implement file sorting by debian readdir
Apr 13, 2025 am 09:06 AM
In Debian systems, the readdir function is used to read directory contents, but the order in which it returns is not predefined. To sort files in a directory, you need to read all files first, and then sort them using the qsort function. The following code demonstrates how to sort directory files using readdir and qsort in Debian system: #include#include#include#include#include//Custom comparison function, used for qsortintcompare(constvoid*a,constvoid*b){returnstrcmp(*(
 How to optimize the performance of debian readdir
Apr 13, 2025 am 08:48 AM
How to optimize the performance of debian readdir
Apr 13, 2025 am 08:48 AM
In Debian systems, readdir system calls are used to read directory contents. If its performance is not good, try the following optimization strategy: Simplify the number of directory files: Split large directories into multiple small directories as much as possible, reducing the number of items processed per readdir call. Enable directory content caching: build a cache mechanism, update the cache regularly or when directory content changes, and reduce frequent calls to readdir. Memory caches (such as Memcached or Redis) or local caches (such as files or databases) can be considered. Adopt efficient data structure: If you implement directory traversal by yourself, select more efficient data structures (such as hash tables instead of linear search) to store and access directory information
 How to configure firewall rules for Debian syslog
Apr 13, 2025 am 06:51 AM
How to configure firewall rules for Debian syslog
Apr 13, 2025 am 06:51 AM
This article describes how to configure firewall rules using iptables or ufw in Debian systems and use Syslog to record firewall activities. Method 1: Use iptablesiptables is a powerful command line firewall tool in Debian system. View existing rules: Use the following command to view the current iptables rules: sudoiptables-L-n-v allows specific IP access: For example, allow IP address 192.168.1.100 to access port 80: sudoiptables-AINPUT-ptcp--dport80-s192.16
 How debian readdir integrates with other tools
Apr 13, 2025 am 09:42 AM
How debian readdir integrates with other tools
Apr 13, 2025 am 09:42 AM
The readdir function in the Debian system is a system call used to read directory contents and is often used in C programming. This article will explain how to integrate readdir with other tools to enhance its functionality. Method 1: Combining C language program and pipeline First, write a C program to call the readdir function and output the result: #include#include#include#includeintmain(intargc,char*argv[]){DIR*dir;structdirent*entry;if(argc!=2){
 How to learn Debian syslog
Apr 13, 2025 am 11:51 AM
How to learn Debian syslog
Apr 13, 2025 am 11:51 AM
This guide will guide you to learn how to use Syslog in Debian systems. Syslog is a key service in Linux systems for logging system and application log messages. It helps administrators monitor and analyze system activity to quickly identify and resolve problems. 1. Basic knowledge of Syslog The core functions of Syslog include: centrally collecting and managing log messages; supporting multiple log output formats and target locations (such as files or networks); providing real-time log viewing and filtering functions. 2. Install and configure Syslog (using Rsyslog) The Debian system uses Rsyslog by default. You can install it with the following command: sudoaptupdatesud
 Debian mail server SSL certificate installation method
Apr 13, 2025 am 11:39 AM
Debian mail server SSL certificate installation method
Apr 13, 2025 am 11:39 AM
The steps to install an SSL certificate on the Debian mail server are as follows: 1. Install the OpenSSL toolkit First, make sure that the OpenSSL toolkit is already installed on your system. If not installed, you can use the following command to install: sudoapt-getupdatesudoapt-getinstallopenssl2. Generate private key and certificate request Next, use OpenSSL to generate a 2048-bit RSA private key and a certificate request (CSR): openss



