1. PHP form verification
In this chapter we will introduce how to use PHP to verify the form data submitted by the client.
Note: We need to consider security when processing PHP forms. In this chapter we will demonstrate the secure processing of PHP form data. In order to prevent hackers and spam, we need to perform data security verification on the form.
The HTML form introduced in this chapter contains the following input fields: Must and optional text fields, radio buttons, and submit buttons.
2. Example display
The code is as follows:
php.cn
PHP 表单验证实例 * 必需字段。
您输入的内容是:"; echo $name; echo "
"; echo $email; echo "
"; echo $website; echo "
"; echo $comment; echo "
"; echo $gender; ?>
The output effect is as shown on the right
3. Practical explanation
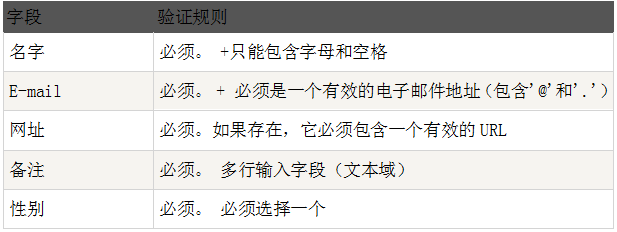
1. Verification rules
2. Text fields
The "Name", "E-mail", and "Website" fields are text input elements, and the "Remarks" field is a textarea. The HTML code is as follows:
"Name":
E-mail:
Website:
Remarks:
3. Radio button
"Gender" The fields are radio buttons and the HTML code looks like this:
gender:
4. Form elements
">
Note: What is the $_SERVER["PHP_SELF"] variable?
So, $_SERVER["PHP_SELF"] will send the form data to the current page instead of jumping to a different page.
Note:
The predefined characters are:
The $_SERVER["PHP_SELF"] variable may be used by hackers!
When hackers use cross-site scripting HTTP links to attack, the $_SERVER["PHP_SELF"] server variable will also be embedded in the script. The reason is that cross-site scripting is appended to the path of the executable file, so the string $_SERVER["PHP_SELF"] will contain the JavaScript program code behind the HTTP link.
Note: XSS is also called CSS (Cross-Site Script), a cross-site scripting attack. Malicious attackers insert malicious HTML code into a Web page. When a user browses the page, the HTML code embedded in the Web page will be executed, thereby achieving the special purpose of the malicious user.
Specify the following form file name as "test_form.php":
##
">
That's fine.
//m.sbmmt.com/ test_form.php/%22%3E%3Cscript%3Ealert('hacked')%3C/script%3E
Please note that any JavaScript code can be added in the ">
Attempt to exploit this vulnerability failed!
7. Use PHP to validate form data
First of all, we process all data submitted by users through PHP's htmlspecialchars() function
When we use the htmlspecialchars() function, the user tries to submit the following text. Domain:
This code will not is executed because it will be saved as HTML escaped code, as shown below:
##
The above code is safe and can be displayed normally on the page or inserted into the email.
##When the user submits the form, we will do the following two things. Things:
Use the PHP trim() function to remove unnecessary characters (such as spaces, tabs, newlines) in user input data.
Use the PHP stripslashes() function to remove backslashes (\) in user input data
Next let us write these filtering functions in In a function we define ourselves, this can greatly improve the reusability of the code. Name the function test_input()
Now, we can detect $ through the test_input() function. For all variables in _POST, the script code is as follows:
4. Summary
Note that when we execute the above script, we will use $_SERVER["REQUEST_METHOD"] to detect whether the form has been submitted. If REQUEST_METHOD is POST, the form will be submitted - and the data will be validated. If the form is not submitted validation will be skipped and displayed blank.
The use of input items in the above examples is optional, and it can be displayed normally even if the user does not enter any data.
In the next chapter we will introduce how to verify the data entered by the user

![Front-end Vue3 actual combat [handwritten vue project]](https://img.php.cn/upload/course/000/000/068/639b12e98e0b5441.png)
![APIPOST tutorial [Popularization of technical concepts related to network communication]](https://img.php.cn/upload/course/000/000/068/63996f34c6c94370.png)