
Course 23917
Course Introduction:Small cases for quick calculations on various graphics

Course 6644
Course Introduction:In today's Internet era, many people want to enter the IT industry, and then they start to crazily learn C/C++, python, Java and other languages. They have learned a lot of languages, but when it comes to actual projects, they still know nothing. I think many novices think that the more languages they learn, the better, but this is not the case. Until later, I got inspiration from some big guys. For novices, computer network knowledge is the most important than the language itself.

Course 5951
Course Introduction:"Playing with JavaScript: Audio Calculator Example" introduces how to use JavaScript to create a simple calculator function.
Course 2897
Course Introduction:If you have any questions, add WeChat: Le-studyg; this course is an in-depth exploration of the internal working principles of computer systems. It starts from the macro application level and gradually goes down to the bottom of the hardware, revealing how all levels of the computer system work together. By studying this course, students will master the entire process from application software to hardware implementation, laying a solid foundation for future technology research and development and innovation.

Course 2283
Course Introduction:If you have any questions, add WeChat: Le-studyg; This course is an in-depth analysis of the core concepts, principles and ideas of computer programming languages. By studying this course, students will master the basic elements of programming languages, understand the advantages and disadvantages of different programming paradigms, and the philosophical ideas of programming languages. This course focuses on the combination of theory and practice, cultivating students' programming thinking and practical abilities, and laying a solid foundation for future study and career.
2023-11-14 23:55:21 0 1 79
What are the performance numbers next to components in the Vue dev tools?
2023-11-09 14:46:48 0 1 305
2023-11-04 16:37:58 0 1 250
How to copy Excel FV function in PHP?
2023-11-04 15:54:09 0 1 254
CSS scope custom properties are not recognized when used to evaluate variables in the parent scope
2023-11-01 21:53:10 0 1 180

Course Introduction:With the popularization of the Internet and the acceleration of digital life, personal privacy has become the focus of social attention. Whether in daily life or in the digital world, our personal privacy faces different security risks. In order to protect personal privacy, trusted computing technology has been widely used in cloud computing, Internet of Things, big data analysis and other fields. This article will explore the impact of trusted computing technology on personal privacy. 1. Definition and principles of trusted computing technology Trusted computing technology refers to ensuring the credibility, integrity and integrity of computing processes and results in computer systems.
2023-06-11 comment 0 582
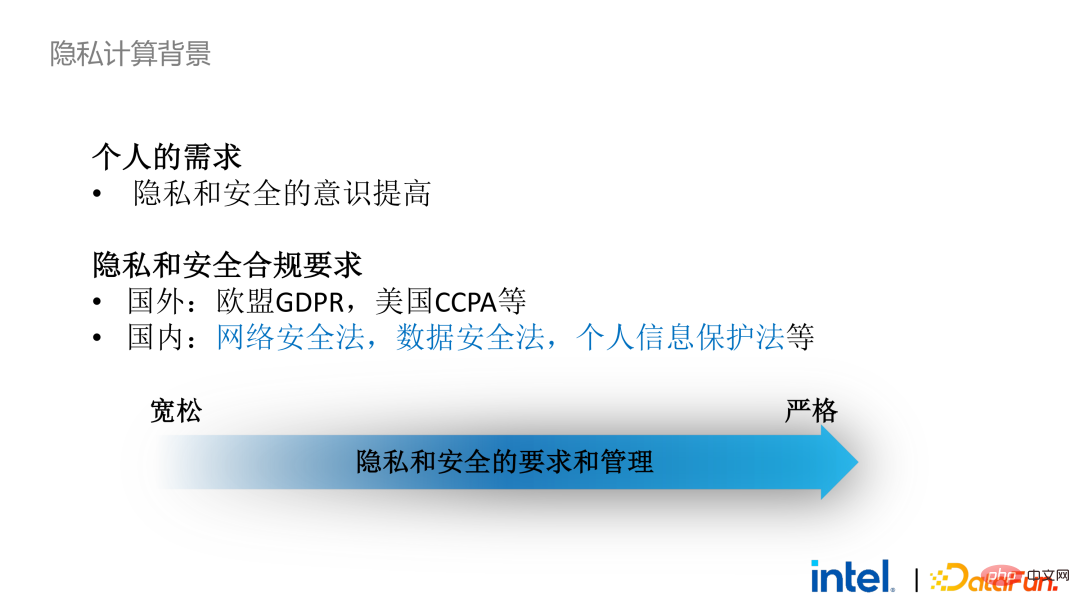
Course Introduction:01 Background and Current Situation of Privacy Computing 1. Background of Privacy Computing Privacy computing has now become a necessity. On the one hand, individual users’ demands for personal privacy and information security have become stronger. On the other hand, there are a large number of privacy and security-related laws and regulations issued, such as the European Union’s GDPR, the United States’ CCPA and domestic personal information protection laws. Regulations and policies have gradually changed from loose to strict, mainly reflected in rights and interests, implementation scope and execution. Strength, etc. Taking GDPR as an example, since it came into effect in 2018, more than 1,000 cases have emerged, with a total fine of more than 11 billion, and the highest single fine exceeds 5 billion (Amazon). 2. Current status of privacy computing In this context, data security has changed from optional to mandatory. This results in a large number of
2023-04-28 comment 0 1104

Course Introduction:With the rapid development of digitization and networking, big data has become an indispensable resource in today's Internet era. But at the same time, the risk of personal privacy leaks also increases. In order to protect data security and privacy, trusted computing technology emerged as the times require. This article will explore the application of trusted computing technology in the field of data privacy protection. First, we need to understand the concept of trusted computing technology. Trusted computing technology refers to establishing a protection mechanism for computing tasks and computing results through various means such as hardware, software, and protocols when performing computing tasks in an untrusted environment.
2023-06-11 comment 0 883

Course Introduction:With the rapid development and popularization of the Internet, people increasingly rely on the network to transmit, store and process data. The ensuing problem is data security and privacy protection. Trusted computing technology emerged as the times require, and this technology has been widely used and promoted. So what is the relationship between trusted computing technology and privacy protection? Let’s explore it together. The basic concept of trusted computing technology refers to ensuring the integrity and credibility of calculation results during the calculation process. Simply put, it is to ensure that the data and programs used as input and output are not tampered with or stolen.
2023-06-11 comment 0 858
Course Introduction:Data assets have become a key tool in product and service design, but centralized collection of user data puts personal privacy at risk and, in turn, exposes organizations to legal risks. Starting in 2016, people began to explore how to use the ownership and origin of data under the protection of user privacy, which made federated learning and federated analysis a hot spot of concern. As the scope of research continues to expand, federated learning has begun to be applied to broader fields such as the Internet of Things. So, what is federated learning? Federated learning is a machine learning setup in which multiple entities collaborate to solve machine learning problems under the coordination of a central server or service provider. Raw data for each client is stored locally and is not exchanged or transferred; instead, it is implemented using focused data updates for instant aggregation
2023-04-29 comment 0 1204