Found a total of 137 related content

Fix software bugs with Python
Article Introduction:How to fix software bugs through Python Bug fixing is a very important part of the software development process. The existence of vulnerabilities may lead to serious consequences such as user data leakage, system crash, and even hacker attacks. As a high-level programming language widely used in software development, Python can help developers fix software vulnerabilities quickly and effectively. This article will introduce some methods and techniques on how to repair software vulnerabilities through Python. 1. Understand the vulnerability types. Before starting to fix software vulnerabilities, you first need to understand the vulnerability types.
2023-06-30
comment 0
946
哪些漏洞不用修复
Article Introduction:并非所有漏洞都必须立即修复,可以考虑漏洞风险,包括:低风险、已缓解、利用难度大、误报和仅影响非关键系统。在决定是否修复漏洞时,要考虑严重性、利用可能性、修复影响、缓解措施和替代措施。对于无需立即修复的漏洞,可采用替代缓解措施,如入侵检测、访问限制、用户教育、非关键系统补丁和漏洞管理计划。
2024-08-15
comment 0
466

Linux common vulnerability repair tutorials!
Article Introduction:Fixing common vulnerabilities in Linux systems is an important step in ensuring system security. Here is a general tutorial for fixing common vulnerabilities: Update system patches: Keeping your operating system up to date with patches is a critical step in preventing vulnerability exploitation. Use a package manager (such as yum, apt-get) to check for and install available system updates. Install the latest software versions: Update the software installed on your system to the latest versions, as new versions often fix known vulnerabilities. Make sure to install the latest packages using your package manager. Disable unnecessary services and ports: Check the services and open ports running on the system, disable unnecessary services and close unused ports. This reduces the system's exposure to potential attacks. Configure Firewall: Set up and configure a firewall to restrict network traffic and
2024-03-07
comment
319

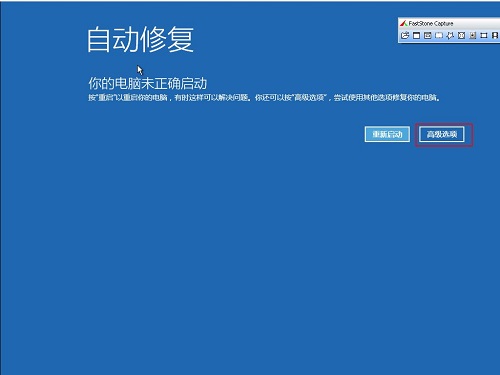
How Tencent Computer Manager fixes system vulnerabilities - Tencent Computer Manager fixes system vulnerabilities
Article Introduction:Presumably many people are using Tencent Computer Manager software on their computers, so do you know how Tencent Computer Manager fixes system vulnerabilities? Next, the editor will bring you Tencent Computer Manager's method of repairing system vulnerabilities. Interested users please hurry up Let’s take a look below. When a computer has a system vulnerability that prevents it from starting or running normally, it is a wise choice to consider using security protection software such as Tencent Computer Manager to repair it. Open Tencent Computer Manager, click "Virus Scan" and "Fix Vulnerabilities" in sequence. At this time, Tencent Computer Manager will start scanning the system for vulnerabilities.
2024-03-04
comment 0
815
360怎么查漏洞修复历史
Article Introduction:通过 360 安全卫士查询漏洞修复历史:1. 打开软件并进入系统修复模块;2. 选择漏洞修复选项;3. 查看修复历史列表;4. 点击漏洞名称查看详细信息,包括描述、补丁和系统状态。
2024-07-15
comment
799
Do system vulnerabilities need to be fixed?
Article Introduction:System vulnerabilities must be repaired in a timely manner to protect system security, improve stability, comply with compliance requirements, save costs, and keep software up-to-date. Methods to fix vulnerabilities include: reviewing vendor security bulletins, using security management solutions, disabling unnecessary services, encrypting data, and conducting security audits.
2024-05-07
comment 0
186

log4j vulnerability repair tutorial: guide you step by step to repair log4j vulnerabilities
Article Introduction:Log4j Vulnerability Repair Tutorial: Detailed guide to repair log4j vulnerabilities step by step, specific code examples are required Introduction Recently, the "log4j vulnerability" (also known as the CVE-2021-44228 vulnerability) has caused widespread attention and concern around the world. This vulnerability poses a serious security risk to applications that use the ApacheLog4j logging library. An attacker can use this vulnerability to remotely execute malicious code, resulting in complete control of the system. This article will provide you with a detailed log4j vulnerability
2024-02-21
comment
342

Log4j Vulnerability Repair Tutorial: Best Practices to Effectively Prevent and Repair Log4j Vulnerabilities
Article Introduction:Log4j vulnerability repair tutorial: Best practices to effectively prevent and repair log4j vulnerabilities, specific code examples are required. Recently, a vulnerability in an open source library called "log4j" has attracted widespread attention. The vulnerability, labeled CVE-2021-44228, affects a variety of applications and systems, triggering security alerts around the world. This article will introduce how to effectively prevent and repair log4j vulnerabilities, and provide some specific code examples. Vulnerability Overview log4j is a Java for logging
2024-02-23
comment 0
734

How Tencent Computer Manager fixes system vulnerabilities with one click - Tencent Computer Manager fixes system vulnerabilities with one click
Article Introduction:I believe that the users here like to use Tencent Computer Manager software just like the editor, but do you know how Tencent Computer Manager can fix system vulnerabilities with one click? Next, the editor will bring you Tencent Computer Manager’s one-click method of repairing system vulnerabilities. Method, interested users can take a look below. Open the [Tencent Computer Manager] software and click the [Toolbox] option. In the [Toolbox] interface, click the [Fix Vulnerability] option. On the [Tencent Computer Manager - Vulnerability Repair] interface, click the [One-click Repair] button. After waiting for the prompt [All vulnerabilities have been successfully repaired, the computer is more secure!], click the [Finish] button.
2024-03-04
comment
919

How to use Linux for security vulnerability scanning and remediation
Article Introduction:How to use Linux to scan and repair security vulnerabilities. In today's digital era, network security threats are becoming increasingly serious, and security vulnerabilities have become an important factor restricting the stability and reliability of network systems. As one of the core operating systems of network systems, Linux systems have always attracted much attention in terms of security. This article will introduce how to use Linux to scan and repair security vulnerabilities, helping users improve system security. 1. Security vulnerability scanning uses OpenVAS for vulnerability scanning. OpenVAS is an open source
2023-08-04
comment 0
1158
Do high-risk vulnerabilities need to be fixed?
Article Introduction:High-risk vulnerabilities need to be fixed. System vulnerabilities refer to defects or errors in the logical design of application software or operating system software; vulnerabilities can be exploited by criminals to attack or control the entire computer through the network implantation of Trojans, viruses, etc., and steal important information and data from your computer. information, and even damage your system; it is still important to repair high-risk system vulnerabilities in a timely manner.
2020-07-08
comment 0
6705

腾讯电脑管家怎么修复系统漏洞 腾讯电脑管家系统漏洞修复方法
Article Introduction:腾讯电脑管家是一款能够很好的保护电脑的软件,有着非常高的安全性,而且能够提供系统漏洞修复,有些用户电脑中有这款软件,但是出现了漏洞不知道怎么操作进行修复,接下来小编就来和各位分享解决方法,希望能够给广大用户们带来帮助。操作方法如下:1、双击打开软件,点击左侧菜单栏中的病毒查杀选项。2、接着点击右侧中的修复漏洞。3、等待漏洞扫描完成。4、最后点击上方的一键修复按钮就可以了。
2024-08-30
comment 0
575

php cve漏洞如何修复
Article Introduction:CVE漏洞是软件中的已知缺陷,可损害系统完整性、机密性和可用性。修复CVE漏洞需要以下步骤:确定受影响的软件或系统。应用安全补丁。禁用或卸载受影响的软件。定期更新软件。实施缓解措施,例如启用防火墙和IDS。监控系统并报告漏洞利用。修复CVE漏洞至关重要,因为它可以保护系统免受恶意攻击、防止数据泄露和维护系统完整性。
2024-08-06
comment
453

Log4j Vulnerability Remediation Guide: Make sure your system is not vulnerable to log4j vulnerabilities
Article Introduction:Log4j vulnerability repair tutorial: Protect your system from log4j vulnerabilities Summary: This article will introduce the risks and impacts of log4j vulnerabilities, as well as specific steps to repair the vulnerabilities. The article will focus on repair methods for Java backend applications and provide specific code examples. Introduction: Logging is an essential feature in the software development process. Due to its wide application, ApacheLog4j, as one of the most common Java logging frameworks, has become the focus of hacker attacks. Recently, a
2024-02-19
comment
946
Do win10 vulnerabilities need to be fixed? Detailed introduction
Article Introduction:After installing the win10 system, everyone's computer will definitely have a lot of vulnerabilities. So do the win10 vulnerabilities need to be repaired? In fact, these vulnerabilities can be repaired, otherwise they will easily lead to virus invasion. Let's take a look at the detailed introduction. Do win10 vulnerabilities need to be fixed? Answer: Win10 vulnerabilities need to be fixed. After the system has been used for a long time, there will definitely be a lot of vulnerabilities, large and small. This is very normal, but repairs are also necessary. If not repaired, there will be many problems, such as blue screen crashes, and the most troublesome thing is that there are Trojans that will use it. Vulnerabilities invade computers. Easy method to fix win10 vulnerabilities: 1. First press the shortcut key "win+i" to open windows settings. 2. Then click "Update and Security" inside.
2023-12-24
comment 0
711

Common security vulnerabilities on Linux servers and how to fix them
Article Introduction:Common security vulnerabilities on Linux servers and their repair methods With the development of the Internet, Linux servers have become the first choice for many enterprises and individuals. However, in the process of using Linux servers, we also have to face the risk of security vulnerabilities. Security vulnerabilities will bring many potential risks to the server, including data leakage, system crash, malicious code execution, etc. Therefore, it is crucial to detect and fix security vulnerabilities promptly. This article will introduce some common Linux server security vulnerabilities and provide corresponding repair methods.
2023-07-03
comment 0
1821

Python builds vulnerability repair and patch management system
Article Introduction:With the rapid development of technology, software plays an increasingly important role in our lives. However, vulnerabilities in software are inevitable. Whenever a vulnerability is discovered in software, developers need to fix it as soon as possible to ensure the security of the system. The emergence of software vulnerability repair and patch management systems has provided developers with more efficient and convenient solutions. As a popular programming language, Python excels in building software vulnerability repair and patch management systems. Python is concise, readable and maintainable
2023-06-30
comment 0
1464

How to use Linux for security hardening and vulnerability repair
Article Introduction:How to use Linux for security reinforcement and vulnerability repair In today's digital world, security has become an important factor that cannot be ignored. Especially for users using Linux operating systems, it is particularly important to reinforce and repair system vulnerabilities. This article will introduce some common methods and techniques to help you better use Linux for security reinforcement and vulnerability repair. Update your system and software First, make sure your Linux system and all installed software are up to date. Developers frequently release security updates and patches to fix
2023-08-03
comment 0
1020
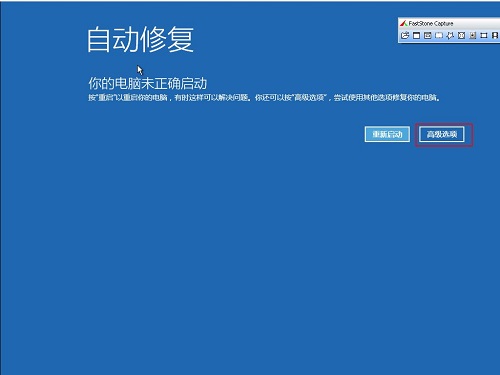
How to fix computer system vulnerabilities
Article Introduction:Repair methods include promptly updating the operating system, updating software and applications, installing and updating anti-virus software, configuring firewalls, using strong passwords and multi-factor authentication, regularly backing up data, paying attention to security awareness and behavior, and referring to the advice of security experts, etc. Detailed introduction: 1. Update the operating system in a timely manner: Operating system manufacturers will regularly release security patches to fix known vulnerabilities, ensuring that the operating system is updated in a timely manner to obtain the latest security fixes; 2. Update software and applications: In addition to the operating system, third-party Software and applications may also have vulnerabilities, update these software regularly, etc.
2023-10-31
comment 0
705

PHP vulnerability scanning and remediation tips
Article Introduction:PHP vulnerability scanning and remediation includes: scanning for vulnerabilities using tools such as Acunetix, Nessus, and BurpSuite. Fix vulnerabilities, such as updating PHP version, installing patches or modifying code. Use security libraries and frameworks. Rescan periodically to confirm the fixes are effective.
2024-05-02
comment 0
940