
SSH is a widely used protocol for secure remote access to Linux servers. Most users use SSH connections with default settings to connect to remote servers. However, the default configuration presents security risks and requires caution.
In order to protect servers with open SSH access, especially when using public IP addresses, disabling root account logins is necessary. Cracking the root password will become easier, so we need to strengthen SSH security.
Here’s how to secure your SSH server connection on Linux:
In order to achieve this goal, you first need to disable SSH access for the root user and create a new user with root privileges. Turning off server access for the root user is a defensive strategy that prevents attackers from breaking into your system. For example, you can create a user named "exampleroot" as follows:
useradd -m exampleroot passwd exampleroot usermod -aG sudo exampleroot
The following is a brief description of the above commands:
After the user creation process, some changes need to be made to the sshd_config file. You can find this file in /etc/ssh/sshd_config. Open the file using any text editor and make the following changes to it:
# Authentication: #LoginGraceTime 2m PermitRootLogin no AllowUsers exampleroot
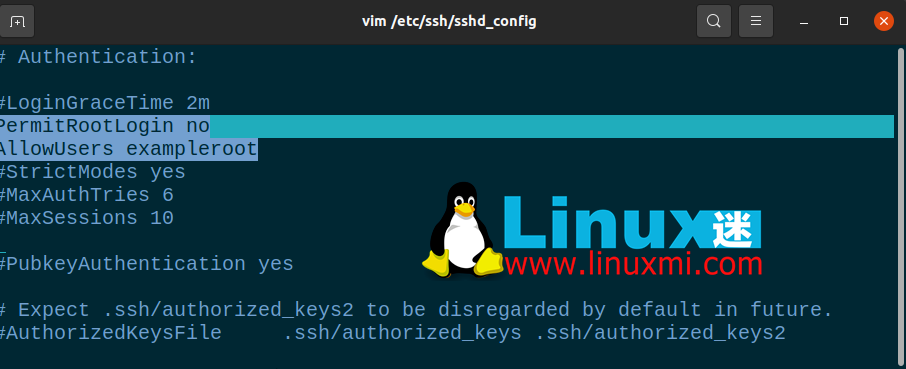
PermitRootLogin line will prevent the root user from gaining remote access using SSH. Including exampleroot in the AllowUsers list will grant the necessary permissions to the user.
Finally, restart the SSH service using the following command:
linuxmi@linuxmi /home/linuxmi/www.linuxmi.com ⚡ sudo systemctl restart ssh
If it fails and you receive an error message, try the following commands. This may vary depending on the Linux distribution you are using.
linuxmi@linuxmi /home/linuxmi/www.linuxmi.com sudo systemctl restart sshd
The default SSH connection port is 22. Of course, all attackers know this and therefore need to change the default port number to ensure SSH security. Although an attacker can easily find new port numbers through an Nmap scan, the goal here is to make the attacker's job more difficult.
To change the port number, open **/etc/ssh/sshd_config** and make the following changes to the file:
Include /etc/ssh/sshd_config.d/*.confPort 22099
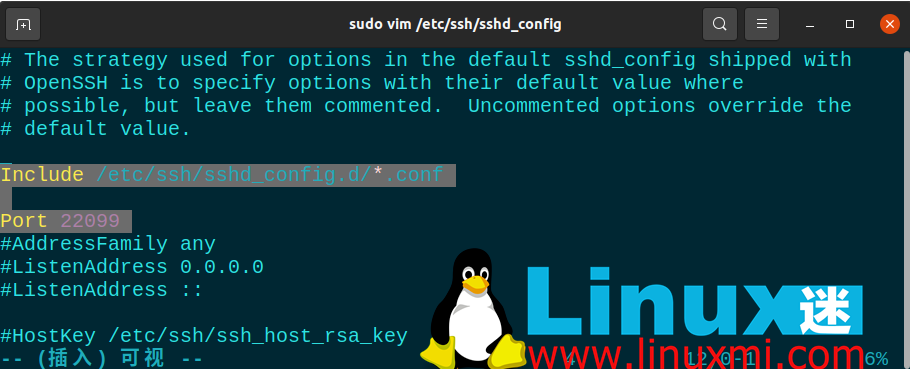
After this step, use sudo systemctl restart ssh to restart the SSH service again. Now you can access your server using the port you just defined. If you are using a firewall, you must also make the necessary rule changes here. When running the netstat -tlpn command, you can see that your SSH port number has changed.
There may be users on your system that you accidentally created without a password. To prevent such users from accessing the server, you can set the PermitEmptyPasswords line value in the sshd_config file to no.
PermitEmptyPasswords no
By default, you can try entering your password as many times as necessary to access the server. However, an attacker could exploit this vulnerability to brute force the server. You can automatically terminate an SSH connection after a certain number of attempts by specifying the number of allowed password attempts.
To do this, change the MaxAuthTries value in the sshd_config file.
MaxAuthTries 3
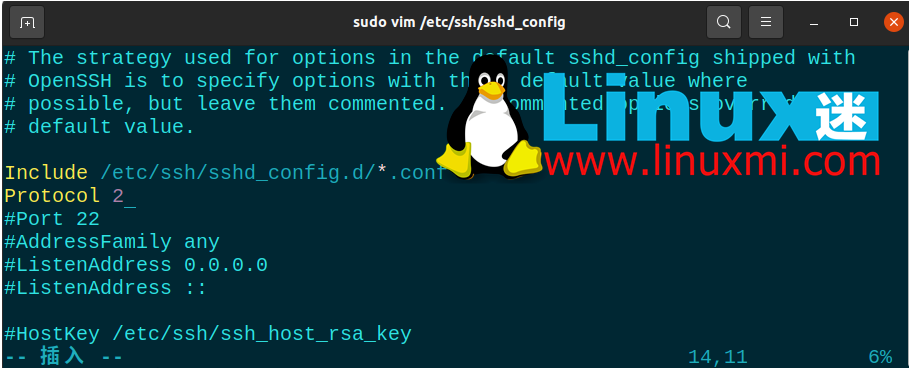
SSH 的第二个版本发布是因为第一个版本中存在许多漏洞。默认情况下,您可以通过将Protocol参数添加到sshd_config文件来启用服务器使用第二个版本。这样,您未来的所有连接都将使用第二个版本的 SSH。
Include /etc/ssh/sshd_config.d/*.conf Protocol 2
攻击者可以尝试通过 SSH 连接的端口转发来访问您的其他系统。为了防止这种情况,您可以在sshd_config文件中关闭AllowTcpForwarding和X11Forwarding功能。
X11Forwarding no AllowTcpForwarding no
连接到服务器的最安全方法之一是使用 SSH 密钥。使用 SSH 密钥时,无需密码即可访问服务器。另外,您可以通过更改sshd_config文件中与密码相关的参数来完全关闭对服务器的密码访问。
创建 SSH 密钥时,有两个密钥:Public和Private。公钥将上传到您要连接的服务器,而私钥则存储在您将用来建立连接的计算机上。
在您的计算机上使用ssh-keygen命令创建 SSH 密钥。不要将密码短语字段留空并记住您在此处输入的密码。如果将其留空,您将只能使用 SSH 密钥文件访问它。但是,如果您设置了密码,则可以防止拥有密钥文件的攻击者访问它。例如,您可以使用以下命令创建 SSH 密钥:
ssh-keygen
大多数情况下,防火墙使用自己的标准框架阻止访问,旨在保护服务器。但是,这并不总是足够的,您需要增加这种安全潜力。
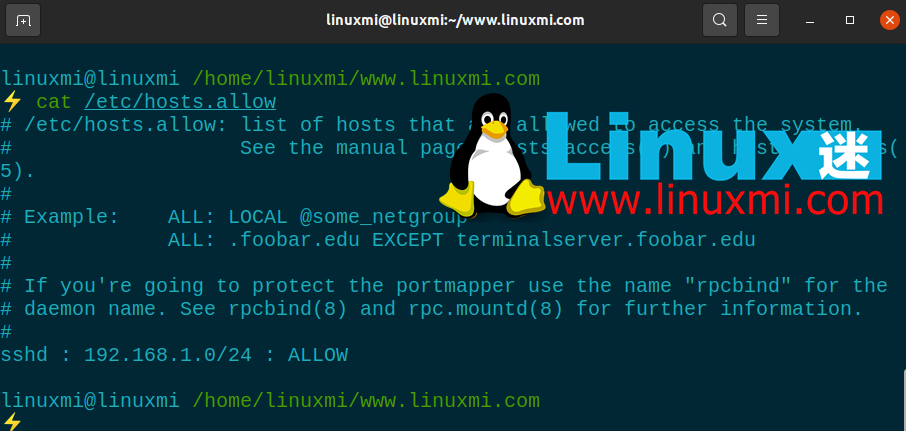
为此,请打开**/etc/hosts.allow**文件。通过对该文件进行的添加,您可以限制 SSH 权限,允许特定 IP 块,或输入单个 IP 并使用拒绝命令阻止所有剩余的 IP 地址。
下面您将看到一些示例设置。完成这些之后,像往常一样重新启动 SSH 服务以保存更改。
所有服务器管理员都应该考虑数据和数据安全问题。服务器安全是一个非常敏感的问题,因为攻击的主要焦点是 Web 服务器,它们几乎包含有关系统的所有信息。由于大多数服务器都在 Linux 基础架构上运行,因此熟悉 Linux 系统和服务器管理非常重要。
SSH 安全只是保护服务器的方法之一。可以通过停止、阻挡或减缓攻击来最大程度地减少您受到的伤害。除了提供 SSH 安全性之外,您还可以实施许多不同的方法来保护您的 Linux 服务器。
The above is the detailed content of 8 Ways to Secure SSH Server Connections on Linux. For more information, please follow other related articles on the PHP Chinese website!




