How to use SpringBoot+SpringSecurity+jwt to implement verification
Environment
springBoot 2.3.3
springSecurity 5.0
- ##jjwt 0.91
<dependency>
<groupId>io.jsonwebtoken</groupId>
<artifactId>jjwt</artifactId>
<version>0.9.1</version>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-security</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>Please ignore the file naming

The role of these two classes is to provide error return processing information classes for users to access unauthorized resources and carry error tokens. To use these two classes, you only need to Just configure it in the security configuration file and just useUserDetailsServiceImpl Login information verification/** * @author Bxsheng * @blogAddress www.kdream.cn * @createTIme 2020/9/17 * since JDK 1.8 * 当用户在没有授权的时候,返回的指定信息 */ @Component public class jwtAccessDeniedHandler implements AccessDeniedHandler { @Override public void handle(HttpServletRequest httpServletRequest, HttpServletResponse httpServletResponse, AccessDeniedException e) throws IOException, ServletException { System.out.println("用户访问没有授权资源"); System.out.println(e.getMessage()); httpServletResponse.sendError(HttpServletResponse.SC_UNAUTHORIZED, e==null?"用户访问没有授权资源":e.getMessage()); } }Copy after login/** * @author Bxsheng * @blogAddress www.kdream.cn * @createTIme 2020/9/17 * since JDK 1.8 */ @Component public class JwtAuthenticationEntryPoint implements AuthenticationEntryPoint { @Override public void commence(HttpServletRequest httpServletRequest, HttpServletResponse httpServletResponse, AuthenticationException e) throws IOException, ServletException { System.out.println("用户访问资源没有携带正确的token"); System.out.println(e.getMessage()); httpServletResponse.sendError(HttpServletResponse.SC_UNAUTHORIZED, e==null?"用户访问资源没有携带正确的token":e.getMessage()); } }Copy after login
This class directly inherits UserDetailsService for login information verification, and then enter the account password When logging in, this class will be entered to verify the information. Of course I am directly using a hard-coded password here. Normally the user’s information and permission information should be obtained from the databaseJwtTokenUtils jwt packaging class@Service public class UserDetailsServiceImpl implements UserDetailsService { @Override public UserDetails loadUserByUsername(String s) throws UsernameNotFoundException { //直接写死数据信息,可以在这里获取数据库的信息并进行验证 UserDetails userDetails = User.withUsername(s).password(new BCryptPasswordEncoder().encode("123456")) .authorities("bxsheng").build(); return userDetails; } }Copy after login
This class directly uses the class in the article of slyh's [SpringBoot JWT to implement login permission control (code))]((https://www.yisu.com/article/257119.htm).JwtAuthenticationFilter Custom verification jwtpackage cn.kdream.securityjwt.utlis; import io.jsonwebtoken.*; import java.util.Date; import java.util.HashMap; import java.util.Map; /** * @author Bxsheng * @blogAddress www.kdream.cn * @createTIme 2020/9/16 * since JDK 1.8 */ public class JwtTokenUtils { public static final String TOKEN_HEADER = "Authorization"; public static final String TOKEN_PREFIX = "Bearer "; public static final String SECRET = "jwtsecret"; public static final String ISS = "echisan"; private static final Long EXPIRATION = 60 * 60 * 3L; //过期时间3小时 private static final String ROLE = "role"; //创建token public static String createToken(String username, String role, boolean isRememberMe){ Map map = new HashMap(); map.put(ROLE, role); return Jwts.builder() .signWith(SignatureAlgorithm.HS512, SECRET) .setClaims(map) .setIssuer(ISS) .setSubject(username) .setIssuedAt(new Date()) .setExpiration(new Date(System.currentTimeMillis() + EXPIRATION * 1000)) .compact(); } //从token中获取用户名(此处的token是指去掉前缀之后的) public static String getUserName(String token){ String username; try { username = getTokenBody(token).getSubject(); } catch ( Exception e){ username = null; } return username; } public static String getUserRole(String token){ return (String) getTokenBody(token).get(ROLE); } private static Claims getTokenBody(String token){ Claims claims = null; try{ claims = Jwts.parser().setSigningKey(SECRET).parseClaimsJws(token).getBody(); } catch(ExpiredJwtException e){ e.printStackTrace(); } catch(UnsupportedJwtException e){ e.printStackTrace(); } catch(MalformedJwtException e){ e.printStackTrace(); } catch(SignatureException e){ e.printStackTrace(); } catch(IllegalArgumentException e){ e.printStackTrace(); } return claims; } //是否已过期 public static boolean isExpiration(String token){ try{ return getTokenBody(token).getExpiration().before(new Date()); } catch(Exception e){ System.out.println(e.getMessage()); } return true; } }Copy after login
This class directly uses slyh's [SpringBoot JWT to implement login permission control (code))](( https://www.yisu.com/article /257119.htm))) in the article's class. The main function of this class is to verify jwt information. It mainly carries token requests, parses jwt and sets it in the security context. Saving the permission information contained in the token to the context is one of the purposes of this approach. You can authenticate userssecurity configuration information/** * @author Bxsheng * @blogAddress www.kdream.cn * @createTIme 2020/9/16 * since JDK 1.8 */ public class JwtAuthenticationFilter extends BasicAuthenticationFilter { public JwtAuthenticationFilter(AuthenticationManager authenticationManager) { super(authenticationManager); } @Override protected void doFilterInternal(HttpServletRequest request, HttpServletResponse response, FilterChain chain) throws IOException, ServletException { String tokenHeader = request.getHeader(JwtTokenUtils.TOKEN_HEADER); //如果请求头中没有Authorization信息则直接放行了 if(tokenHeader == null || !tokenHeader.startsWith(JwtTokenUtils.TOKEN_PREFIX)){ chain.doFilter(request, response); return; } //如果请求头中有token,则进行解析,并且设置认证信息 if(!JwtTokenUtils.isExpiration(tokenHeader.replace(JwtTokenUtils.TOKEN_PREFIX,""))){ //设置上下文 UsernamePasswordAuthenticationToken authentication = getAuthentication(tokenHeader); SecurityContextHolder.getContext().setAuthentication(authentication); } super.doFilterInternal(request, response, chain); } //获取用户信息 private UsernamePasswordAuthenticationToken getAuthentication(String tokenHeader){ String token = tokenHeader.replace(JwtTokenUtils.TOKEN_PREFIX, ""); String username = JwtTokenUtils.getUserName(token); // 获得权限 添加到权限上去 String role = JwtTokenUtils.getUserRole(token); List<GrantedAuthority> roles = new ArrayList<GrantedAuthority>(); roles.add(new GrantedAuthority() { @Override public String getAuthority() { return role; } }); if(username != null){ return new UsernamePasswordAuthenticationToken(username, null,roles); } return null; } }Copy after login
@EnableGlobalMethodSecurity(prePostEnabled = true) Enable prePostEnabled annotation authorizationStartup class@Configuration @EnableWebSecurity @EnableGlobalMethodSecurity(prePostEnabled = true) public class SecurityJwtConfig extends WebSecurityConfigurerAdapter { @Autowired private jwtAccessDeniedHandler jwtAccessDeniedHandler; @Autowired private JwtAuthenticationEntryPoint jwtAuthenticationEntryPoint; @Override protected void configure(HttpSecurity http) throws Exception { http.cors().and().csrf().disable().authorizeRequests() .antMatchers(HttpMethod.OPTIONS,"/**") .permitAll() .antMatchers("/").permitAll() //login 不拦截 .antMatchers("/login").permitAll() .anyRequest().authenticated() //授权 .and() // 禁用session .sessionManagement().sessionCreationPolicy(SessionCreationPolicy.STATELESS); // 使用自己定义的拦截机制,拦截jwt http.addFilterBefore(new JwtAuthenticationFilter(authenticationManager()), UsernamePasswordAuthenticationFilter.class) //授权错误信息处理 .exceptionHandling() //用户访问资源没有携带正确的token .authenticationEntryPoint(jwtAuthenticationEntryPoint) //用户访问没有授权资源 .accessDeniedHandler(jwtAccessDeniedHandler); } @Bean public PasswordEncoder passwordEncoder(){ //使用的密码比较方式 return new BCryptPasswordEncoder(); } }Copy after login
I configured three methods in the startup class, one is used for login information, and the other two are set to require permission accessEffectDirect access to user information that requires authorization@SpringBootApplication @RestController public class SecurityJwtApplication { private final AuthenticationManagerBuilder authenticationManagerBuilder; public SecurityJwtApplication(AuthenticationManagerBuilder authenticationManagerBuilder) { this.authenticationManagerBuilder = authenticationManagerBuilder; } public static void main(String[] args) { SpringApplication.run(SecurityJwtApplication.class, args); } @GetMapping("/") public String index(){ return "security jwt"; } @PostMapping("/login") public String login(@RequestParam String u,@RequestParam String p){ // 登陆验证 UsernamePasswordAuthenticationToken token = new UsernamePasswordAuthenticationToken(u, p); Authentication authentication = authenticationManagerBuilder.getObject().authenticate(token); SecurityContextHolder.getContext().setAuthentication(authentication); //创建jwt信息 String token1 = JwtTokenUtils.createToken(u,"bxsheng", true); return token1; } @GetMapping("/role") @PreAuthorize("hasAnyAuthority('bxsheng')") public String roleInfo(){ return "需要获得bxsheng权限,才可以访问"; } @GetMapping("/roles") @PreAuthorize("hasAnyAuthority('kdream')") public String rolekdream(){ return "需要获得kdream权限,才可以访问"; } }Copy after login
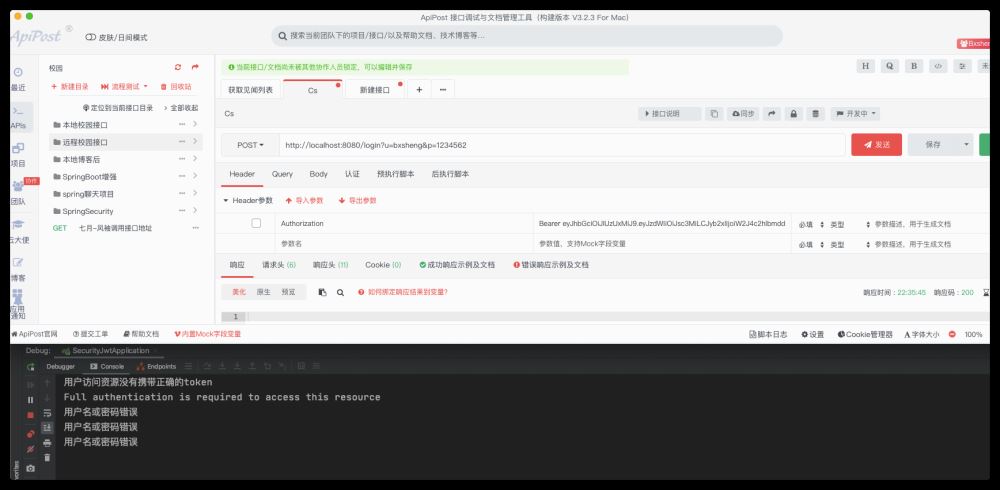
Directly accessing resource information that only requires authorization without using a token will enter the JwtAuthenticationEntryPoint class
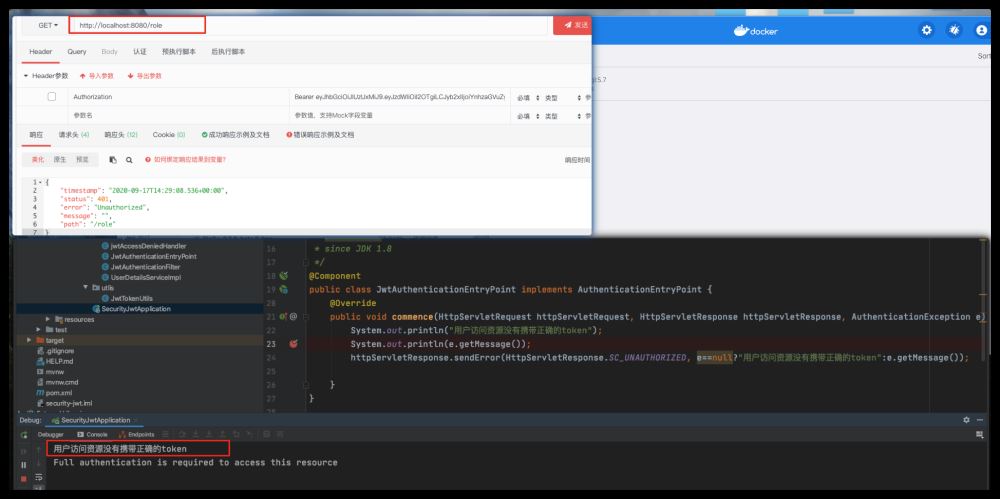
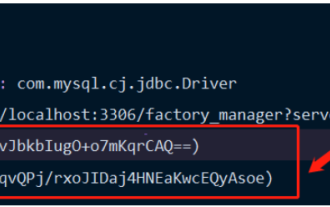
Access the login method in the startup class and get the token informationBecause I use a fixed password, I use When accessing with an incorrect password, you can capture the exception information in springboot's global exception handling/** * @author Bxsheng * @blogAddress www.kdream.cn * @createTIme 2020/9/17 * since JDK 1.8 */ @RestControllerAdvice public class Error { @ExceptionHandler(BadCredentialsException.class) public void badCredentialsException(BadCredentialsException e){ System.out.println(e.getMessage());//用户名或密码错误 // throw new BadCredentialsException(e.getMessage()); } }Copy after loginGet the token correctly and access protected resources
There is hard-coded bxsheng permission information in it, so normally the resource information identified by bxsheng can be obtained.Successfully obtained information
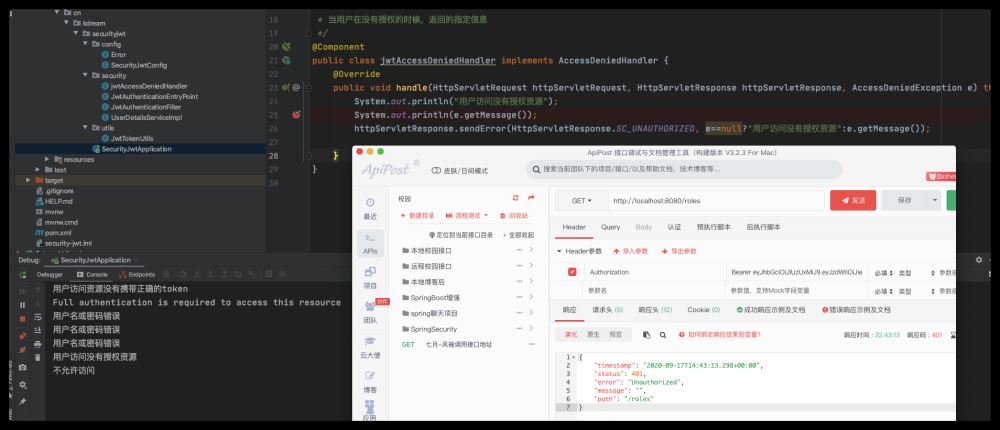
Attempt to obtain unauthorized resource information
Using token to directly access unauthorized resource information will enter the jwtAccessDeniedHandler class
The above is the detailed content of How to use SpringBoot+SpringSecurity+jwt to implement verification. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How Springboot integrates Jasypt to implement configuration file encryption
Jun 01, 2023 am 08:55 AM
How Springboot integrates Jasypt to implement configuration file encryption
Jun 01, 2023 am 08:55 AM
Introduction to Jasypt Jasypt is a java library that allows a developer to add basic encryption functionality to his/her project with minimal effort and does not require a deep understanding of how encryption works. High security for one-way and two-way encryption. , standards-based encryption technology. Encrypt passwords, text, numbers, binaries... Suitable for integration into Spring-based applications, open API, for use with any JCE provider... Add the following dependency: com.github.ulisesbocchiojasypt-spring-boot-starter2. 1.1Jasypt benefits protect our system security. Even if the code is leaked, the data source can be guaranteed.
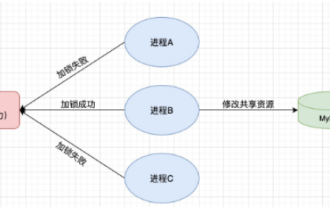 How to use Redis to implement distributed locks in SpringBoot
Jun 03, 2023 am 08:16 AM
How to use Redis to implement distributed locks in SpringBoot
Jun 03, 2023 am 08:16 AM
1. Redis implements distributed lock principle and why distributed locks are needed. Before talking about distributed locks, it is necessary to explain why distributed locks are needed. The opposite of distributed locks is stand-alone locks. When we write multi-threaded programs, we avoid data problems caused by operating a shared variable at the same time. We usually use a lock to mutually exclude the shared variables to ensure the correctness of the shared variables. Its scope of use is in the same process. If there are multiple processes that need to operate a shared resource at the same time, how can they be mutually exclusive? Today's business applications are usually microservice architecture, which also means that one application will deploy multiple processes. If multiple processes need to modify the same row of records in MySQL, in order to avoid dirty data caused by out-of-order operations, distribution needs to be introduced at this time. The style is locked. Want to achieve points
 How to use ThinkPHP6 for JWT authentication?
Jun 12, 2023 pm 12:18 PM
How to use ThinkPHP6 for JWT authentication?
Jun 12, 2023 pm 12:18 PM
JWT (JSONWebToken) is a lightweight authentication and authorization mechanism that uses JSON objects as security tokens to securely transmit user identity information between multiple systems. ThinkPHP6 is an efficient and flexible MVC framework based on PHP language. It provides many useful tools and functions, including JWT authentication mechanism. In this article, we will introduce how to use ThinkPHP6 for JWT authentication to ensure the security and reliability of web applications
 How to solve the problem that springboot cannot access the file after reading it into a jar package
Jun 03, 2023 pm 04:38 PM
How to solve the problem that springboot cannot access the file after reading it into a jar package
Jun 03, 2023 pm 04:38 PM
Springboot reads the file, but cannot access the latest development after packaging it into a jar package. There is a situation where springboot cannot read the file after packaging it into a jar package. The reason is that after packaging, the virtual path of the file is invalid and can only be accessed through the stream. Read. The file is under resources publicvoidtest(){Listnames=newArrayList();InputStreamReaderread=null;try{ClassPathResourceresource=newClassPathResource("name.txt");Input
 Comparison and difference analysis between SpringBoot and SpringMVC
Dec 29, 2023 am 11:02 AM
Comparison and difference analysis between SpringBoot and SpringMVC
Dec 29, 2023 am 11:02 AM
SpringBoot and SpringMVC are both commonly used frameworks in Java development, but there are some obvious differences between them. This article will explore the features and uses of these two frameworks and compare their differences. First, let's learn about SpringBoot. SpringBoot was developed by the Pivotal team to simplify the creation and deployment of applications based on the Spring framework. It provides a fast, lightweight way to build stand-alone, executable
 How to use JWT and JWE for API authentication and encryption in PHP
Jun 17, 2023 pm 02:42 PM
How to use JWT and JWE for API authentication and encryption in PHP
Jun 17, 2023 pm 02:42 PM
With the development of the Internet, more and more websites and applications need to provide API interfaces for data interaction. In this case, API authentication and encryption become very important issues. As a popular authentication and encryption mechanism, JWT and JWE are increasingly used in PHP. Well, this article will explain how to use JWT and JWE for API authentication and encryption in PHP. Basic concepts of JWT JWT stands for JSONWe
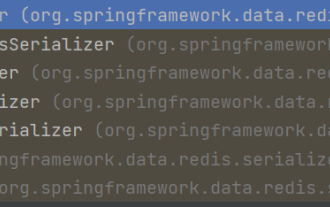 How SpringBoot customizes Redis to implement cache serialization
Jun 03, 2023 am 11:32 AM
How SpringBoot customizes Redis to implement cache serialization
Jun 03, 2023 am 11:32 AM
1. Customize RedisTemplate1.1, RedisAPI default serialization mechanism. The API-based Redis cache implementation uses the RedisTemplate template for data caching operations. Here, open the RedisTemplate class and view the source code information of the class. publicclassRedisTemplateextendsRedisAccessorimplementsRedisOperations, BeanClassLoaderAware{//Declare key, Various serialization methods of value, the initial value is empty @NullableprivateRedisSe
 Analysis of secure JWT token generation and verification technology in PHP
Jul 01, 2023 pm 06:06 PM
Analysis of secure JWT token generation and verification technology in PHP
Jul 01, 2023 pm 06:06 PM
Analysis of Secure JWT Token Generation and Verification Technology in PHP With the development of network applications, user authentication and authorization are becoming more and more important. JsonWebToken (JWT) is an open standard (RFC7519) for securely transmitting information in web applications. In PHP development, it has become a common practice to use JWT tokens for user authentication and authorization. This article will introduce secure JWT token generation and verification technology in PHP. 1. Basic knowledge of JWT in understanding how to generate and