
针对PHP的网站主要存在下面几种攻击方式,这里介绍下,大家在书写php代码的时候一定要注意下,本篇文章有一定的参考性!
针对PHP的网站主要存在下面几种攻击方式:
命令注入(Command Injection)
eval注入(Eval Injection)
客户端脚本攻击(Script Insertion)
跨网站脚本攻击(Cross Site Scripting, XSS)、SQL注入攻击(SQL injection)
跨网站请求伪造攻击(Cross Site Request Forgeries, CSRF)
Session 会话劫持(Session Hijacking)
Session 固定攻击(Session Fixation)
HTTP响应拆分攻击(HTTP Response Splitting)
文件上传漏洞(File Upload Attack)
目录穿越漏洞(Directory Traversal)
远程文件包含攻击(Remote Inclusion)
动态函数注入攻击(Dynamic Variable Evaluation)
URL攻击(URL attack)
表单提交欺骗攻击(Spoofed Form Submissions)
HTTP请求欺骗攻击(Spoofed HTTP Requests)
命令注入攻击
PHP中可以使用下列5个函数来执行外部的应用程序或函数
system、exec、passthru、shell_exec、“(与shell_exec功能相同)
函数原型
string system(string command, int &return_var)
command 要执行的命令
return_var 存放执行命令的执行后的状态值
string exec (string command, array &output, int &return_var)
command 要执行的命令
output 获得执行命令输出的每一行字符串
return_var 存放执行命令后的状态值
void passthru (string command, int &return_var)
command 要执行的命令
return_var 存放执行命令后的状态值
string shell_exec (string command)
command 要执行的命令
漏洞实例
例1:
//ex1.php
<?php $dir = $_GET["dir"];
if (isset($dir))
{
echo "<pre class="brush:php;toolbar:false">";
system("ls -al ".$dir);
echo "我们提交http://www.sectop.com/ex1.php?dir=| cat /etc/passwd
提交以后,命令变成了 system("ls -al | cat /etc/passwd");

eval注入攻击
eval函数将输入的字符串参数当作PHP程序代码来执行
函数原型:
mixed eval(string code_str) //eval注入一般发生在攻击者能控制输入的字符串的时候
//ex2.php
<?php $var = "var";
if (isset($_GET["arg"]))
{
$arg = $_GET["arg"];
eval("\$var = $arg;");
echo "\$var =".$var;
}
?>
当我们提交 http://www.sectop.com/ex2.php?arg=phpinfo();漏洞就产生了
动态函数
<?php func A()
{
dosomething();
}
func B()
{
dosomething();
}
if (isset($_GET["func"]))
{
$myfunc = $_GET["func"];
echo $myfunc();
}
?>
程序员原意是想动态调用A和B函数,那我们提交http://www.sectop.com/ex.php?func=phpinfo 漏洞产生
防范方法
尽量不要执行外部命令
使用自定义函数或函数库来替代外部命令的功能
使用escapeshellarg函数来处理命令参数
使用safe_mode_exec_dir指定可执行文件的路径
esacpeshellarg函数会将任何引起参数或命令结束的字符转义,单引号“'”,替换成“\'”,双引号“"”,替换成“\"”,分号“;”替换成“\;”
用safe_mode_exec_dir指定可执行文件的路径,可以把会使用的命令提前放入此路径内
safe_mode = On
safe_mode_exec_di r= /usr/local/php/bin/
客户端脚本植入
客户端脚本植入(Script Insertion),是指将可以执行的脚本插入到表单、图片、动画或超链接文字等对象内。当用户打开这些对象后,攻击者所植入的脚本就会被执行,进而开始攻击。
可以被用作脚本植入的HTML标签一般包括以下几种:
<script>标签标记的javascript和vbscript等页面脚本程序。在<script>标签内可以指定js程序代码,也可以在src属性内指定js文件的URL路径<br/><object>标签标记的对象。这些对象是java applet、多媒体文件和ActiveX控件等。通常在data属性内指定对象的URL路径<br/><embed>标签标记的对象。这些对象是多媒体文件,例如:swf文件。通常在src属性内指定对象的URL路径<br/><applet>标签标记的对象。这些对象是java applet,通常在codebase属性内指定对象的URL路径<br/><form>标签标记的对象。通常在action属性内指定要处理表单数据的web应用程序的URL路径</script>
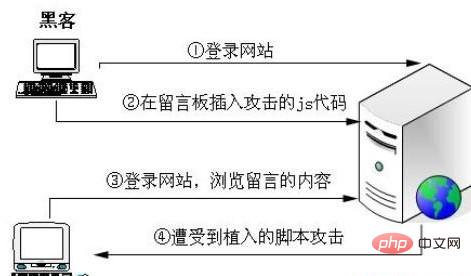
客户端脚本植入的攻击步骤
1、攻击者注册普通用户后登陆网站
2、打开留言页面,插入攻击的js代码
3、其他用户登录网站(包括管理员),浏览此留言的内容
4、隐藏在留言内容中的js代码被执行,攻击成功
Example
Database
CREATE TABLE `postmessage` (
`id` int(11) NOT NULL auto_increment,
`subject` varchar(60) NOT NULL default ”,
`name` varchar(40) NOT NULL default ”,
`email` varchar(25) NOT NULL default ”,
`question` mediumtext NOT NULL,
`postdate` datetime NOT NULL default '0000-00-00 00:00:00′,
PRIMARY KEY (`id`)
) ENGINE=MyISAM DEFAULT CHARSET=gb2312 COMMENT='User's message' AUTO_INCREMENT=69;
//add.php Insert message
//list.php Message list
//show.php Display message
Submit the message below
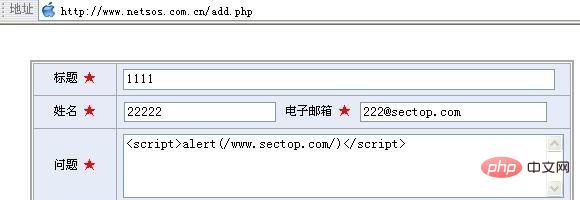
The js script will be executed when browsing this message
Insert <script>while(1){windows.open();}</script> infinite pop-up box
Insert<script>location.href="http://www.sectop.com";</script> Jump to the phishing page
Or use other self-constructed js code to attack
Methods of prevention
Generally use the htmlspecialchars function to convert special characters into HTML encoding
Function prototype
string htmlspecialchars (string string, int quote_style, string charset)
string is the string to be encoded
quote_style Optional, the value can be ENT_COMPAT, ENT_QUOTES, ENT_NOQUOTES, the default value ENT_COMPAT, which means only converting double quotes but not single quotes. ENT_QUOTES, means double quotes and single quotes All must be converted. ENT_NOQUOTES, indicating that double quotes and single quotes are not converted.
charset is optional, indicating the character set used.
The function will convert the following special characters into html encoding:
& —-> &
" —-> "
' —-> '
> —-> >
Put the 98th of show.php Change the line to
Then check the vulnerability page where js is inserted
XSS Cross Site Scripting Attack
##Cross-site scripting is mainly used by attackers to read cookies or other personal data of website users. Once the attacker obtains this data, he can pretend to be this user to log in to the website and obtain this user's permissions.
General steps for cross-site scripting attacks:
1. The attacker sends the xss http link to the target user in some way.
2. The target user logs in to this website and opens the link sent by the attacker during the login period. xss link
3. The website executed this xss attack script
4. The target user page jumped to the attacker's website, and the attacker obtained the target user's information
5. The attacker used the target user's information Log in to the website and complete the attack




