

Recently, Sangfor discovered how to exploit the remote command execution vulnerability of the Apache axis component. The essence of this vulnerability is due to the administrator's misconfiguration of AdminService. When the enableRemoteAdmin attribute is set to true, the attacker can remotely use the AdminService interface to self-publish the constructed WebService. When accessing the generated WebService interface again, it can be triggered. Internally referenced classes are used to exploit remote command execution vulnerabilities.
axis component introduction
axis full nameApache EXtensible Interaction System is the Apache extensible interaction system. axis provides the basic framework for creating server-side, client-side, and gateway SOAP operations. The current version of axis is mainly for Java, and the C-oriented version is under development. axis is not exactly a SOAP engine, but can also be used as a standalone SOAP server and a server embedded in a Servlet engine (such as Tomcat).
Vulnerability Analysis
The essence of the vulnerability is the administrator’s configuration error of AdminService. When the enableRemoteAdmin attribute is set to true, the attacker can construct the WebService to call the template.utility.Execute class in the freemarker component, and remotely use the AdminService interface to publish WebService , access the generated WebService interface again, pass in the command to be executed, and you can exploit the remote command execution vulnerability.
Vulnerability Recurrence
Build an environment of axis 1.4 tomcat6, and set the enableRemoteAdmin attribute in the AdminService configuration to true .
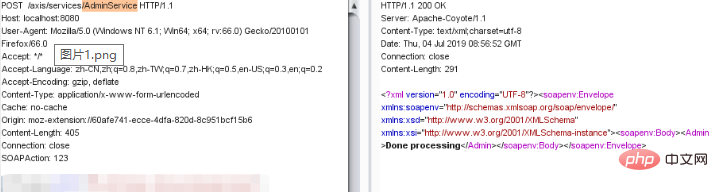
Pass in the constructed data for WebService publishing, as shown below:
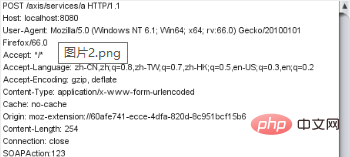
Then call the WebService interface to pass in the command and execute it, as shown below:
Repair suggestions
1. Configure URL access control policy: deployed on the axis server on the public network, you can pass The ACL prohibits access to the /services/AdminService and /services/FreeMarkerService paths.
2. Disable the axis remote management function: axis server-config.wsdd file in the WEB-INF folder in the axis directory and set the value of "enableRemoteAdmin" is false.
If you want to know more about web security, please visit: Web Server Security
The above is the detailed content of How to fix remote command execution vulnerability in Apache axis component. For more information, please follow other related articles on the PHP Chinese website!