 Java
Java
 javaTutorial
javaTutorial
 How does Java framework open source community participation deal with security threats?
How does Java framework open source community participation deal with security threats?
How does Java framework open source community participation deal with security threats?
The open source community provides key advantages to Java framework security through collective intelligence, continuous monitoring, and early detection. In practice, the community responded quickly to the Log4Shell vulnerability, releasing security patches, contributing tools, and sharing information. Individuals and organizations can join the community, follow updates, contribute code, participate in events, and report bugs, thereby contributing to the security of the Java framework and ensuring its continued reliability in enterprise development.

The Java framework open source community participates in security threats and writes a security chapter
Introduction
With the widespread adoption of Java frameworks in enterprise application development, it is critical to keep them secure. This article explores the critical role of the open source community in identifying and addressing security threats to Java frameworks, and provides a practical example of how active community participation can enhance the security of the framework.
The importance of community participation
The open source community provides the following key advantages for Java framework security:
- Collective wisdom: The community brings together security experts, developers, and users, whose collective knowledge and experience can quickly identify and resolve threats.
- Continuous monitoring: The community continuously monitors the framework, looks for vulnerabilities, and quickly fixes discovered issues.
- Early Detection: Community members can enhance the security of the framework by contributing new features and patches, allowing it to detect and mitigate potential threats early.
Practical Case: Responding to Log4j Vulnerabilities
In December 2021, a serious vulnerability named Log4Shell was discovered in the widely used Java framework Log4j. This vulnerability allows attackers to execute arbitrary code via log messages, posing a serious threat to millions of applications.
The Java community responded quickly and comprehensively to Log4Shell:
- Quick patch: Log4j maintainers released security patches before they were widely exploited Bug fixed.
- Community Contributions: Community members have created tools and guidance to help affected organizations detect and remediate vulnerabilities.
- Information Sharing: The community actively shares information about vulnerabilities and their mitigations through discussion forums, blogs, and social media.
Suggestions for participating in the community
The following suggestions can help individuals and organizations actively participate in the Java framework open source community:
- Join related Mailing lists and community forums.
- Follow the official documentation and updates of the framework.
- Contribute code, documentation and security reports.
- Participate in community events such as conferences and hackathons.
- Report discovered vulnerabilities or security issues promptly.
Conclusion
The Java Framework open source community plays a vital role in protecting the framework from security threats by providing collective intelligence, continuous monitoring, and early detection role. By actively participating in the community, individuals and organizations can help strengthen the security of the Java framework and ensure its continued reliability in enterprise application development.
The above is the detailed content of How does Java framework open source community participation deal with security threats?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1378
1378
 52
52
 Perfect Number in Java
Aug 30, 2024 pm 04:28 PM
Perfect Number in Java
Aug 30, 2024 pm 04:28 PM
Guide to Perfect Number in Java. Here we discuss the Definition, How to check Perfect number in Java?, examples with code implementation.
 Weka in Java
Aug 30, 2024 pm 04:28 PM
Weka in Java
Aug 30, 2024 pm 04:28 PM
Guide to Weka in Java. Here we discuss the Introduction, how to use weka java, the type of platform, and advantages with examples.
 Smith Number in Java
Aug 30, 2024 pm 04:28 PM
Smith Number in Java
Aug 30, 2024 pm 04:28 PM
Guide to Smith Number in Java. Here we discuss the Definition, How to check smith number in Java? example with code implementation.
 Java Spring Interview Questions
Aug 30, 2024 pm 04:29 PM
Java Spring Interview Questions
Aug 30, 2024 pm 04:29 PM
In this article, we have kept the most asked Java Spring Interview Questions with their detailed answers. So that you can crack the interview.
 Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Java 8 introduces the Stream API, providing a powerful and expressive way to process data collections. However, a common question when using Stream is: How to break or return from a forEach operation? Traditional loops allow for early interruption or return, but Stream's forEach method does not directly support this method. This article will explain the reasons and explore alternative methods for implementing premature termination in Stream processing systems. Further reading: Java Stream API improvements Understand Stream forEach The forEach method is a terminal operation that performs one operation on each element in the Stream. Its design intention is
 TimeStamp to Date in Java
Aug 30, 2024 pm 04:28 PM
TimeStamp to Date in Java
Aug 30, 2024 pm 04:28 PM
Guide to TimeStamp to Date in Java. Here we also discuss the introduction and how to convert timestamp to date in java along with examples.
 Java Program to Find the Volume of Capsule
Feb 07, 2025 am 11:37 AM
Java Program to Find the Volume of Capsule
Feb 07, 2025 am 11:37 AM
Capsules are three-dimensional geometric figures, composed of a cylinder and a hemisphere at both ends. The volume of the capsule can be calculated by adding the volume of the cylinder and the volume of the hemisphere at both ends. This tutorial will discuss how to calculate the volume of a given capsule in Java using different methods. Capsule volume formula The formula for capsule volume is as follows: Capsule volume = Cylindrical volume Volume Two hemisphere volume in, r: The radius of the hemisphere. h: The height of the cylinder (excluding the hemisphere). Example 1 enter Radius = 5 units Height = 10 units Output Volume = 1570.8 cubic units explain Calculate volume using formula: Volume = π × r2 × h (4
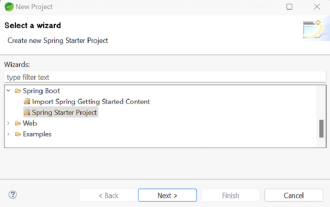 How to Run Your First Spring Boot Application in Spring Tool Suite?
Feb 07, 2025 pm 12:11 PM
How to Run Your First Spring Boot Application in Spring Tool Suite?
Feb 07, 2025 pm 12:11 PM
Spring Boot simplifies the creation of robust, scalable, and production-ready Java applications, revolutionizing Java development. Its "convention over configuration" approach, inherent to the Spring ecosystem, minimizes manual setup, allo




